.DOT file virus: spam delivering malicious .dot extension attachments
An ongoing malspam campaign spreads malicious .dot files claiming to contain sensitive information about recipients. The emails look targeted as they address users by name and even provide their home address. However, the password-protected .dot entities attached to these messages are actually linked to a malware botnet distributing the Crypt0L0cker ransomware.
Table of Contents
What is the .dot file virus?
Computer users in the United Kingdom and several other locations run the risk of unknowingly installing a piece of ransomware while routinely looking over messages in their email inbox. This online ambush is being set up by the cybercriminal group behind the file-encrypting ransomware called Crypt0L0cker, alias TorrentLocker. The spam wave in question involves .dot file attachments and exploits Microsoft Word macros in order to execute arbitrary code on target machines. This trick gained notoriety for deploying perpetrating software on a large scale. Macros are disabled in Office documents by default, but once an unsuspecting user fires the associated Visual Basic for Applications (VBA) script for whatever reason, depositing bad code on the system is a mere technicality as long as a skilled threat actor is at the helm of such a campaign. Crypt0L0cker, in its turn, will encode all of the victim’s personal files and request a ransom in the Bitcoin cryptocurrency in exchange for the decryption service.
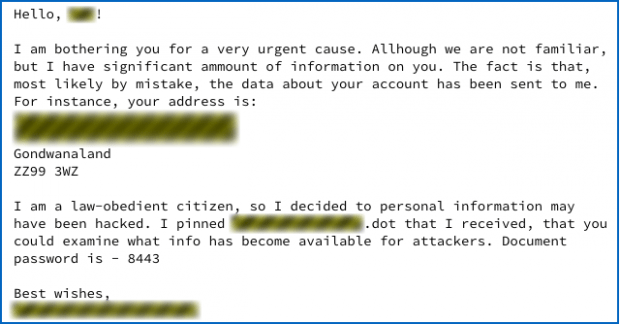
The involvement of email spam in the process of ransomware distribution is a very widespread tactic with ransomware operators. The novel trend revolves around sending a file called [recipient’s name].dot to numerous people over email. The body of such emails will start with the one of the following phrases: “Hello, [target’s actual name]! I am bothering you for a very urgent cause. Although we are not familiar, I have significant amount of information on you. The fact is that, most likely by mistake, the data about your account has been sent to me,” or “I am disturbing you for a very important occasion. Though you don’t know me, I have significant amount of individual info about you. The fact is that, most probably mistakenly, the data about your account has been emailed to me.” Despite the fact that these intros are full of misspellings and other mistakes, they are supposed to serve as the catch to entice the user into learning more. The rest of the text instructs the recipient to open the attached .dot file, which supposedly contains the totality of leaked confidential data.
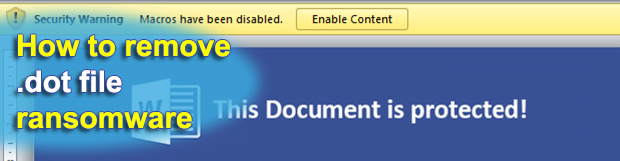
Again, DOT stands for “document template” format closely linked with MS Word. Interestingly, the attachment is password-protected, the password proper being provided in the message body. Once the user enters it, they will see a word processor window open up. Originally, there is no relevant content in it other than the alert saying “This document is protected!”. A yellowish “Security Warning” in the upper part of the window recommends the victim to enable content in order to see the purported information. What happens in fact, though, is the offending VBA script starts running in the background. It establishes a connection with a compromised web server and downloads a malicious payload behind the scenes.
Such a complex contamination chain ends up promoting the Crypt0Locker ransomware onto a computer. First, it identifies potentially valuable files located on local drives, removable media and network drives. Then, it encrypts every matching entry while leaving the filenames unaltered. Finally, the infection displays a ransom note asking for digital cash. This is one of the most dangerous crypto threats currently in the wild.
As far as this compromise vector goes, avoiding the necessity of paying this hefty ransom is a matter of not opening the booby-trapped .dot file received via email – as simple as that. However, social engineering has always been an effective medium for malware proliferation, because some people just can’t resist the temptation of finding out what’s inside. If the Crypt0L0cker ransomware has made its way into a PC, it may be possible to restore the jumbled files by means of conventional forensics.
.dot extension automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by .dot extension
Workaround 1: Use file recovery software
It’s important to know that the .dot extension creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the extension under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether .dot extension has been completely removed
Again, file removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other extension, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this extension and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓