Decrypt Crypt0L0cker virus: Crypt0L0cker removal and file recovery

The predicament where a computer program calling itself the Crypt0L0cker says it has encrypted one’s personal files is an awful mishap. To begin with, this ransomware isn’t kidding when making such statements. Secondly, buying decryption seems to be the only applicable method to get the data back. This post explains the anatomy of this malware and advises on restoring the encrypted files without surrendering to the extortion.
The first samples of Crypt0L0cker were discovered in late spring this year, and the virus has gone through a few nosedives as well as upswings ever since. Notwithstanding this operational instability, it’s still afloat and its malicious infrastructure appears to be evolving. This infection bears a strong resemblance to TorrentLocker, a once dominating ransomware that infected tens of thousands of machines across the globe within a fairly short time span. The upgrade includes hardly any significant changes, except the name presented to the victims and a number of geo restrictions applied at the dawn of the campaign, where only non-U.S. users would be targeted. Essentially, the strategy is invariable: the virus stealthily encrypts the PC owner’s personal files and then comes into the open with ransom payment recommendations so that the information can be decrypted.
The dark side of social engineering is the scammers’ favorite trick to drop the malign executable on computers. In particular, Crypt0L0cker has been distributed with deceptive emails designed to appear as if they were sent by governmental and other official institutions. These may include fake traffic violation notices and order notifications containing ZIP attachments, which actually carry the ransomware payload. A more recent technique is the post office hoax, where people receive messages with links to track the status of delivery or schedule the delivery for a later date. Once these links are clicked, the dangerous code gets immediately executed on the machine.
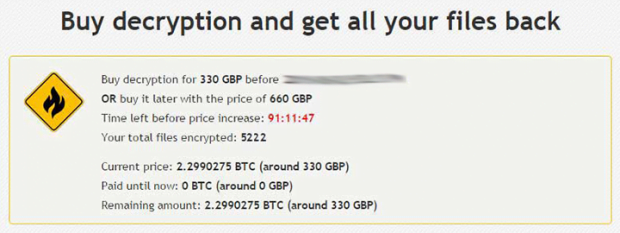
The next phase is to inconspicuously scan all hard drive volumes for files with popular extensions, but the virus isn’t after the ones that are compulsory for normal functioning of the operating system. The spotted select files then get encrypted with asymmetric cryptography standard, which means that the public and private key are the prerequisites for decryption. The essential portion of these mandatory details is kept outside the PC and cannot be retrieved until Crypt0L0cker’s demands have been met. The ransom details are displayed to the attacked user in the form of a txt or html file named DECRYPT_INSTRUCTIONS. The victim is provided with a hyperlink to the Buy Decryption site, which can only be accessed via Tor network. The ransom that must be paid amounts to 2.2 BTC, or around 600 USD, and it doubles unless the user submits the payment within a 96-hour deadline.
The RSA-2048 algorithm leveraged by Crypt0L0cker is impossible to bypass or crack, but this doesn’t necessarily mean that the ransom is the only way to retrieve stolen files, every one of which becomes appended with the “.encrypted” suffix. There’s a couple of workarounds that can contribute to restoration of the data, ransomware removal being only a part of the solution that doesn’t fix the problem altogether. To avoid such assaults in the future, be sure to abstain from opening attachments and clicking links in dubious-looking emails. And certainly, keeping file backups in the cloud is the main precaution in scenarios like this.
Table of Contents
Crypt0L0cker file automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Crypt0L0cker ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the file and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by Crypt0L0cker file
Workaround 1: Use file recovery software
It’s important to know that the Crypt0L0cker file creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the file under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether Crypt0L0cker file has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the file itself does not belong inside your computer. Incidentally, it often comes with other file, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this file and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓