Remove and decrypt RSA-4096 ransomware virus
The use of RSA-4096 public-key encryption is not restricted to legitimate purposes such as the protection of classified governmental or military documents. This extremely strong cryptosystem has also become a dangerous instrument in extortionists’ hands. Ransomware plagues like TeslaCrypt demonstrate how technologies preventing data leakage can turn into an inalienable part of cybercrime infrastructure.
The newer editions of TeslaCrypt have opened Pandora’s box in that they feature uncrackable encryption. Some ransom trojans employ the Advanced Encryption Standard, or AES, where the encoding and recovery tokens are the same. This method has been implemented incorrectly in a number of attack incidents, which allowed researchers to retrieve the public key and thus decipher victims’ files. As opposed to that, RSA uses different keys. The private one can become available to the infected user on condition that they go through a ransom payment process. Furthermore, the randomization and size of the keys are tangible enough for the calculation routine to be useless. RSA-4096 is therefore an insuperable obstacle to data recovery.
The operators of TeslaCrypt virus appear to be taking the payload distribution seriously. They kicked off with mass spam campaigns that would lure people into clicking a booby-trapped email attachments. Then, they switched the tactic and started leveraging exploit kits, including Neutrino and Angler. Now, an additional mechanism that the scammers are using to push their trojan is by compromising sites built with open-source content management systems like WordPress and Joomla.
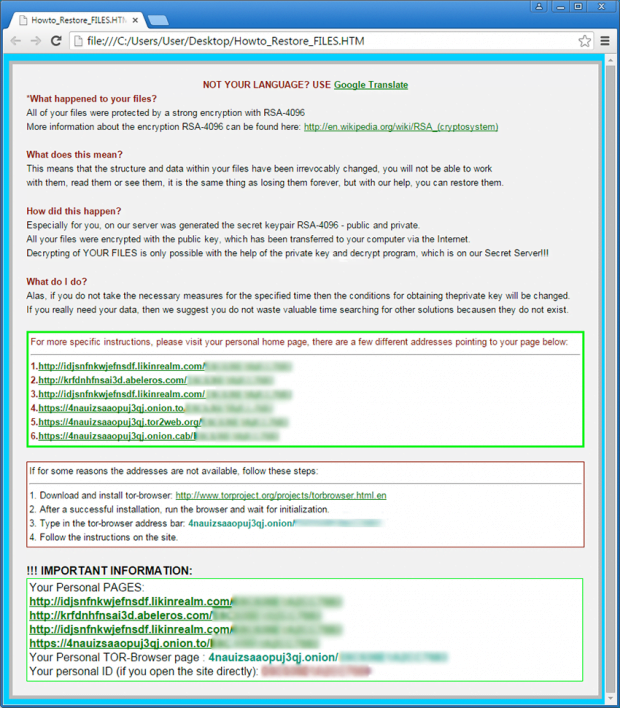
One way or another, the infected users find themselves in a situation where their important files on the hard disk and network shares become encrypted and hence unavailable. The trojan provides restoration instructions in a separate document named Howto_RESTORE_FILES, HELP_TO_DECRYPT_YOUR_FILES or similar. It says “All of your files were protected by a strong encryption with RSA-4096” and lists the steps to submit the fee, which ranges from 300 to 500 USD. The money is to be sent to a Bitcoin address specified in the instructions.
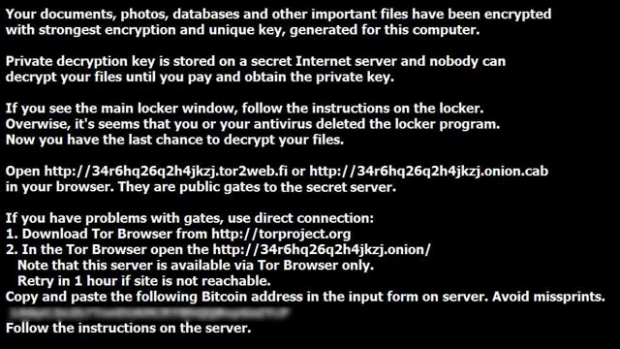
The ransomed files also get a new extension which is different for every new iteration of TeslaCrypt. The most recent ones are .mp3, .micro, .ttt and .xxx. The infection also replaces the victim’s wallpaper with a black-and-white image containing the recovery walkthrough. Having clicked on the suggested TOR Browser link, the user ends up on the Decryption Service page designed for processing payments and hosting the decrypt tool.
Once again, trying to overcome RSA-4096 encryption is a nail-biting experience because the private recovery key is stored on the secret server controlled by the cyber thugs. Given this unfortunate peculiarity, the applicable methods aren’t plentiful. And yet, the hostage files can be restored from a backup, if any, and in some cases through the use of Volume Shadow Copies or recovery software.
Table of Contents
RSA-4096 ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download RSA-4096 ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by RSA-4096 ransomware
Workaround 1: Use file recovery software
It’s important to know that the RSA-4096 ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether RSA-4096 ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓