TorrentLocker ransomware removal and file decryption
Although TorrentLocker was believed to have gone extinct, it has risen from the ashes. The name of this threat echoes back to 2015, when it denoted one of the most devastating and widespread samples of file-encrypting malware. Now in 2017 the infection has gotten a more powerful extortion toolkit and a new set of external attributes. Learn the current characteristics of this pest and get a list of steps to handle the aftermath of such an attack.
Table of Contents
What is TorrentLocker?
TorrentLocker, also referred to as Crypt0L0cker, is a standalone strain of ransomware that takes one’s important information hostage and requests a fee for recovery. Its activity revolves around the use of cryptography for scrambling popular types of files stored on a target workstation. To add insult to injury, its bad impact reaches local and network drives, as well as removable media containing personal documents, images, videos, databases, certificates and many more formats of data that pose potential value to a victim. As it has been mentioned, TorrentLocker re-emerged recently, after almost two years of inactivity. This isn’t a common thing in the cyber extortion environment. The fine-tuned edition mostly zeroes in on European countries, with Italy and Denmark being targeted most heavily.
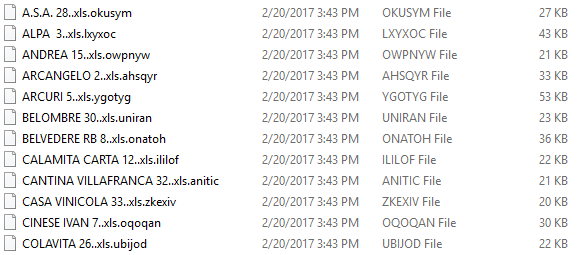
As far as Italian incidents go, the threat actors have been employing a top-notch tactic for the distribution. They have somehow managed to generate numerous spam emails signed by the country’s Posta Elettronica Certificata, which is a reputable local authority generally associated with an elevated degree of security. Consequently, the booby-trapped messages are not blacklisted by spam filters and look safe enough to open. Regardless of the specific localization, the anatomy of the attack further involves a JavaScript email attachment disguised as an invoice that will trigger the ransomware routine immediately. The first thing TorrentLocker does when inside a computer is it looks for data to be encrypted. It goes equipped with a list of targeted file extensions, so every matching entry found inside local HDD volumes, network shares and plugged-in memory devices is subject to mutilation. After the program applies a military-grade cryptographic algorithm, all the valuable information becomes inaccessible. Furthermore, the trojan appends every such file with a unique string of characters that will follow the original extension.
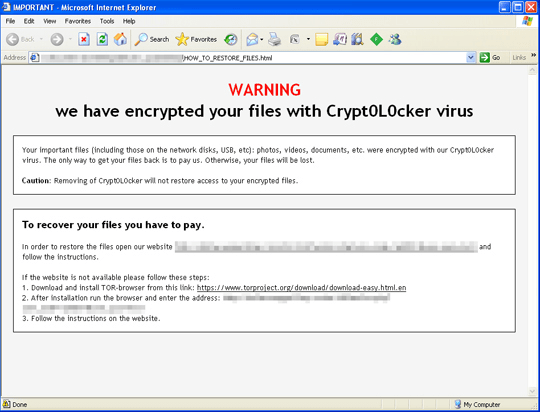
Then, the victim interaction phase of the compromise takes root. TorrentLocker creates ransom notes called HOW_TO_RESTORE_FILES.txt and HOW_TO_RESTORE_FILES.html inside affected folders and the desktop. These are, essentially, walkthroughs for data restoration through paying a ransom. The warning in them, which goes, “We have encrypted your files with Crypt0L0cker virus,” adds some finishing strokes to the formidable extortion masterpiece. The how-to’s tell the victim to download and install Tor browser, visit their personal decryption page and get details about the crooks’ Bitcoin wallet address and the size of the ransom. The monetary facet of the deal is usually somewhere in the range of 0.5 – 1 BTC, although the amount tends to fluctuate.
Another bad news for those who fall victim to the updated TorrentLocker ransomware is that it now accommodates a data-stealing component. This means that users’ passwords and other confidential information is potentially at risk, so it’s not only the cryptographic assault that will cause trouble. Paying the ransom, no doubt, is an awfully uncomforting thing, even if sensitive records are at stake. So take your time before making the final decision, and do not fail to try the methods below right away – these are best practice tips for data recovery without having to meet malefactors’ demands.
TorrentLocker file automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download TorrentLocker ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the file and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by TorrentLocker file
Workaround 1: Use file recovery software
It’s important to know that the TorrentLocker file creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the file under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether TorrentLocker file has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the file itself does not belong inside your computer. Incidentally, it often comes with other file, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this file and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓