AGL electricity bill email scam infecting with Cryptolocker virus
Crypto infections are no longer indiscriminate in terms of whom they compromise and where. The latest newsmaking story involves a widespread strain of file-encrypting malware, which is deposited onto the computers of commercial and retail customers of AGL Energy, one of the biggest electricity facilities in Australia. The criminals have been deploying an intricate phishing campaign, duping the targeted users into downloading a booby-trapped ZIP file.
AGL customers currently run the risk of catching a sample of crypto ransomware, most likely CryptoLocker or a variant named Crypt0L0cker. The distributors of this high-severity infection are using all their guile to convince people into downloading what appears to be their monthly bill. A professionally designed “Your electricity bill” email has been sent to thousands of Australians allegedly on behalf of AGL Energy, containing the total amount due and a button that says “View your Bill”. This message has the company’s logo in it and provides a replica of the organization’s Privacy Policy and other standard technicalities.
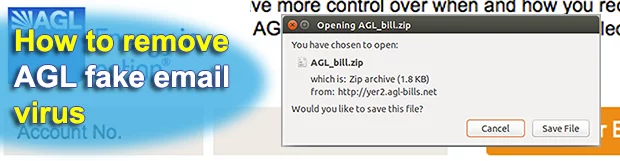
The next phase of the phishing attack involves a redirect to a fake landing page disguised as the customer’s personal account with the electricity services provider. It says “My AGL Monthly Bill”. In order to download the invoice, though, the user needs to first enter the Captcha code, which adds an aura of legitimacy and trust to the whole blatant ruse. After the pseudo authorization, the user can finally download AGL_bill.zip file. This object contains a hidden JavaScript component tasked with downloading CryptoLocker (Crypt0L0cker) to the machine in a furtive fashion.
The dialog that appears before the ZIP archive is downloaded says that its size is only 1.8 KB. This, obviously, looks suspicious from the start. If the user is gullible enough to click the Save File button, a fast-flux network of malicious domains will come into play. There are multiple URLs engaged in this hoax, so it’s problematic for the regulatory entities to take them all down in one shot. This explains why such campaigns might persevere for weeks. Meanwhile, the malefactors are making money by applying crypto to deny the availability of the victims’ personal data.
CryptoLocker or another breed of ransomware, which may arrive to Windows PCs through this scheme, scans the local drives, mapped and unmapped network drives as well as removable media in order to locate files with popular extensions. It also reaches out to the Command and Control server to obtain the public key for encryption routine. When the Trojan is done encoding data on the targeted computer, it displays recovery demands in .html, .txt and .bmp documents. According to those instructions, the user can purchase the private key and the decryptor for $200-500. The ransom is payable in Bitcoins.
To avoid scams of this sort, be sure to pay attention to details. The fact that the invoice is a ZIP file in this case is quite suspicious. And so is the unusually small size of this archive. Furthermore, it may be a good idea to try and open the dubious email attachment on a smartphone – there will be an error most of the time, while it would all go smooth if the message were legit. If the contamination has taken place, follow a data recovery workaround and get rid of the ransomware.
Table of Contents
AGL email automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download AGL extension remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the fake and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by AGL email
Workaround 1: Use file recovery software
It’s important to know that the AGL email creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the email under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether AGL email has been completely removed
Again, extension removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the fake itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this scam and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓





