CryptoLocker virus removal and ransomware files decryption
There are computer threats that no longer pose risk once removed. In contrast to this overwhelming majority, even after a ransom Trojan is eliminated, its effects persevere. Files affected by the CryptoLocker ransomware are not recoverable unless the victim agrees to the terms of the imposed buyout and submits money to the extortionists. In some cases, though, restoring the data is feasible beyond that. Continue reading to learn fresh details on this matter.
The story of CryptoLocker is accompanied by conspiracy theories and intricacy. This strain was originally launched in 2013 and it was one of the few viable infections of its kind at that time. The outrageous campaign drew close attention of the authorities, which resulted in its takedown less than a year after. The Gameover ZeuS botnet, which was liable for distributing the virus in question, went extinct and there was hope that the problem was finally solved. Nevertheless, the relief turned out temporary. Computer users around the globe are still suffering the consequences of CryptoLocker attacks. The explanation of this is the emergence of several copycats that were found to have a different origin.
The contemporary iterations of this pest do the exact same thing: they spread with email attachments, encrypt the victims’ personal files and demand a fee for decryption. The distribution seems quite trivial: a user receives a message over email that impersonates some reputable organization. This email contains an attachment masqueraded as something innocuous and interesting, for instance a confidential delivery notice or an Excel payroll. The moment this file is opened is when the compromise commences.
The Trojan looks for data on the physical disk and mapped network drives, in particular files with prevalent extensions, such as .jpg, .pdf, .doc, .xls, .psd, etc. Every such object then becomes encrypted with RSA standard. The encryption key dubbed “public” is generated and kept on the PC, and the decryption “private” key is sent to the scammers’ Command and Control server. The ransomware also attempts to delete all shadow copies of files in a bid to make the associated recovery activity inefficient. The recent variant of this ransom threat was found to append files with .micro extension.
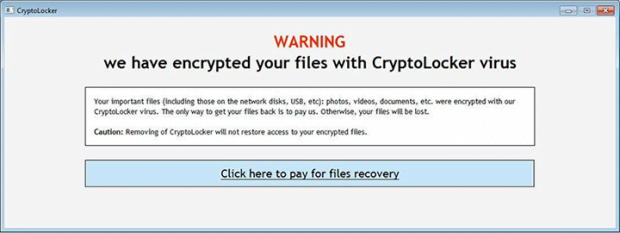
Then, the malicious software opens an interface that says “Your personal files are encrypted.” The warning screen goes on to state the following: “Encryption was produced using unique public key RSA-4096 generated for this computer. To decrypt files, you need to obtain the private key.” The victim has a time span of 72 hours to pay 0.5 BTC and get the decryption performed. In case the deadline is not met, the CryptoLocker operators threaten to destroy the private key and therefore make the information irrecoverable. By the way, the fraudsters’ appetite appears to have shrunk as the previous editions of their malware would extort 2 Bitcoins, which is about 700 USD. However, even the current amount, which is 4 times less, isn’t a pleasure to pay.
Specific ransom instruction files are additional attributes of this infection. The Trojan creates the following documents on the desktop and in every folder as long as it holds locked files: HOW_TO_RECOVER_FILES.html and HOW_TO_RECOVER_FILES.txt. These basically repeat the same info as on the main GUI – pay Bitcoins, get the key, decode the data. All in all, submitting the money is the last thing to do. Before even pondering over paying, do not fail to try the techniques that can upset the cybercriminals.
Table of Contents
CryptoLocker ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download CryptoLocker ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by CryptoLocker ransomware
Workaround 1: Use file recovery software
It’s important to know that the CryptoLocker ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether CryptoLocker ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓