Remove Ykcol virus ransomware and recover .ykcol files
New version releases are a common thing in the ransomware underground. The prolific Locky strain is no exception. Less than a month since the previous iteration called Lukitus surfaced, the architects of this massive campaign have come up with an update. The brand new edition appends the .ykcol extension to ransomed data, hence its catalogued denomination. This post provides a comprehensive report on this one.
Table of Contents
What is the Ykcol ransomware?
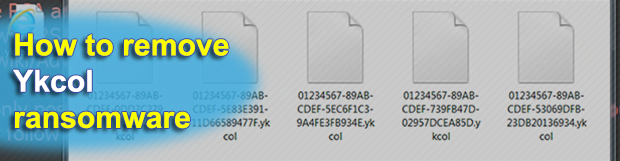
Although security analysts and infected users refer to this Locky variant as Ykcol, that’s somewhat of a misnomer. To eliminate ambiguity, it’s worth stating from the get-go that the contagion is still Locky, except it has acquired a couple of new features. First off, the main distinguishing hallmark sign is the new .ykcol extension being suffixed to every encrypted file. Secondly, the ransom notes are now named ykcol.htm and ykcol.bmp. And thirdly, its distribution process via malspam has come to revolve around booby-trapped emails with the subject “Status of invoice”. Of course it makes sense predicting that more spam waves are imminent, so other themes are very likely to appear soon as well.
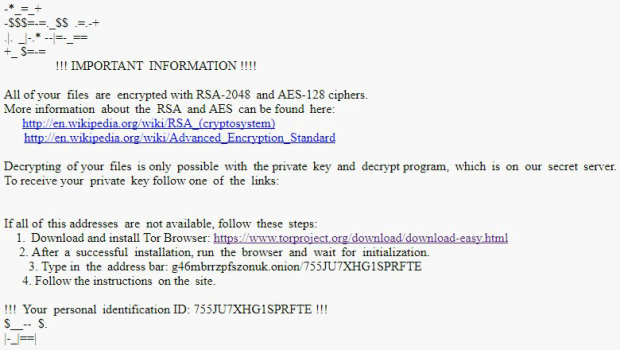
The malicious email attachment is a 7z archive. The extracted random-named VBS entity is the one to blame for deploying the contamination routine proper. Once loaded, this file covertly downloads Ykcol ransomware onto the computer. From that moment on, things get entirely out of hand. The blackmail Trojan fires up a scan for valuable data. It peeks inside all non-system paths on hard drive volumes, as well as removable drives and network shares. When a matching file is found along the way, it gets cryptographically skewed through the use of asymmetric RSA-2048 and symmetric AES-128 ciphers. This activity results in blocking access to targeted files, meaning that the victim will no longer be able to open or edit them.
Like it has been mentioned, there is a byproduct of this unauthorized data processing – the hostage entries get the .ykcol string added at the end. There is actually more tweaking, though. The extension is prepended with 36 hexadecimal characters to make it impossible to work out what file it is. Here’s an example: a spreadsheet named, say, Schedule.xls will turn into something like 644JU6XH-G0SPRFTE-0A5B2D4A-0A78AF2AB2FE.ykcol. The ransomware also leaves how-to’s regarding the decryption options the user has. These are files named ykcol.htm and ykcol.bmp, where a random 4-character line may be inserted in between the name and extension. The BMP version of the ransom notes substitutes the desktop background to put additional pressure on the victim.
According to the crooks’ recommendations, the user is supposed to download and install Tor Browser, type a specific URL in the address bar, and follow instructions on the site named Locky Decryptor Page. The recovery boils down to sending 0.25 BTC (about $1,000) to the perpetrators, after which they will purportedly provide the private decryption key along with the automatic decryptor. Well, in real world, trusting kidnappers isn’t a good call. The same applies to cyber attacks like this. Nobody can guarantee a successful outcome if you agree to the threat actors’ terms, so your data might stay corrupted regardless. It’s always a better idea to try everything else first. The steps below are a good starting point.
Ykcol ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Ykcol ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by Ykcol ransomware
Workaround 1: Use file recovery software
It’s important to know that the Ykcol ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether Ykcol ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓