Remove WannaSister ransomware and decrypt .UIWIX virus

The recent disconcerting WannaCry ransomware incident has obviously inspired other cybercrooks to follow suit. A slew of replicas started popping up thick and fast, some of them crude but some tailored professionally enough to become a major problem. The latest one of these derivatives dubbed UIWIX resembles its more successful prototype by the same exploit-based distribution vector. However, its makers went somewhat further in a few ways.
Table of Contents
What is WannaSister UIWIX ransomware?
The new UIWIX ransomware is a file-encrypting infection that uses WannaSister.exe process to make its toxic impact. The executable name is reminiscent of the newsmaking WannaCry virus, which has been running rampant over the past fortnight. Although there appears to be a tangible imitation hue in this new campaign, the two samples were most likely developed independently. One of the key differences in terms of behavior is that the WannaSister UIWIX ransom Trojan reportedly utilizes a fileless infection mechanism. In other words, it is executed in memory rather than be launched from a certain system location to which its payload was dropped at an early phase of the compromise. Such a stealth approach allows the threat to fly under the radar of antimalware tools.
Having contaminated a Windows computer, WannaSister UIWIX first performs some reconnaissance. In particular, it checks the system for traces of a virtual machine. If one is detected, the attack won’t proceed. This is another clever move aimed at preventing analysts from reverse engineering the ransomware code. The pest goes equipped with a built-in list of targeted file formats. So it cross-checks the data stored on the computer and network drives against these criteria in order to single out the most potentially valuable documents, images, videos, databases and the like. Then, it applies a combo of two cryptographic algorithms to make the files inaccessible. These cryptosystems include RC4 and AES-256 in CBC (Cipher Block Chaining) mode.
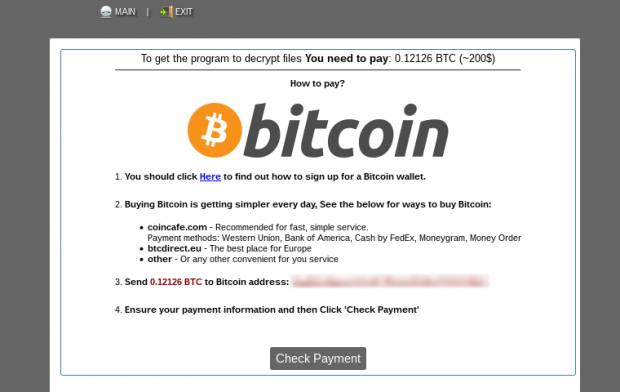
As part of the data skewing routine, the WannaSister pest renames targeted files. Specifically, it keeps the original names unchanged but appends them with the ._[victim ID].UIWIX string, where the unique ID part consists of 10 digits. So for instance, a file named Prices.xlsx will turn into something like Prices.xlsx._8323679218.UIWIX. Another byproduct of the attack is the emergence of plaintext ransom notes called _DECODE_FILES.txt. These will be dropped into affected folders with hostage data and the desktop. Interestingly, the extortionists apparently confused concepts as they wrote, “All your personal files are decoded” in the intro of the recovery manual. It should have been “encoded” instead. To proceed with the decryption, the victim is instructed to install Tor Browser and visit one of the URLs listed in the how-to document. Ultimately, the infected person ends up on the UIWIX payment page, which tells them to submit 0.12 BTC (about 300 USD) to a victim-specific Bitcoin address.
It’s noteworthy that WannaSister UIWIX ransomware and WannaCry baddie have some common ground in terms of the propagation methods. The newcomer also employs EternalBlue, the same NSA exploit used by the more prolific counterpart. This exploit allows the threat actors behind the attack to leverage SMB (Server Message Block) vulnerabilities for injecting the malicious code into computers behind the would-be victims’ back. Unfortunately, the crypto implementation is too robust to crack in this case, so plagued users are either bound to buy the decryption service from the felons or try some forensic tips and tricks.
WannaSister UIWIX ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download WannaSister UIWIX ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by WannaSister UIWIX ransomware
Workaround 1: Use file recovery software
It’s important to know that the WannaSister UIWIX ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether WannaSister UIWIX ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓