.wallet file: no ransom to amagnus@india.com, stopper@india.com, lavandos@pr.com

A new ransomware plague is roving the Internet in search of victims. Its distinctive feature is the .wallet extension being appended to all personal files stored on a PC and network drives. The extension will also contain the attackers’ email address, which may be amagnus@india.com, stopper@india.com, or lavandos@pr.com. Researchers have denominated this strain the Dharma ransomware based on another possible file extension it may leverage.
Table of Contents
What are [amagnus@india.com].wallet, [stopper@india.com].wallet, [lavandos@pr.com].wallet?
It turns out that the .wallet ransomware is a successor of the infamous infection called CrySiS, whose distribution campaign closed down several weeks ago. To their credit, the developers released the Master Decryption Keys back then so that victims could restore their data. In the case of the Dharma baddie, the threat actors behind it probably forked the code of CrySiS and produced new crypt keys that were not published during the above-mentioned leak. Perhaps this whole story is nothing but a rebranding, operators being the same individuals. One way or another, the .wallet extension virus is now in the wild. It is extremely harmful and cannot be decrypted for free for the time being.
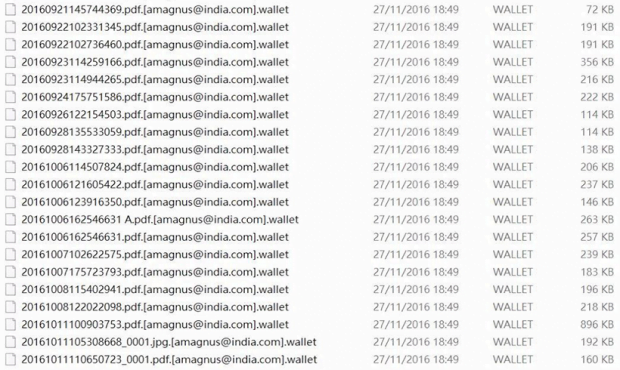
So, what happens to your files if this ransomware hits your machine? It utilizes a military-grade cryptographic standard to deny the accessibility of important data. Furthermore, there is another byproduct of this compromise: the infection changes filenames. It appends every scrambled entry with one of the following strings: .[amagnus@india.com].wallet, .[stopper@india.com].wallet, or .[lavandos@pr.com].wallet. By the way, the final component of this extension may also be .dharma or .zzzzz, depending on the particular variant of the malady or the affiliate spreading it. For instance, an object named “document.docx” will end up morphing into “document.docx.[amagnus@india.com].wallet”, where the email part may be different.
The indication of perpetrators’ contact details directly in the filename is self-explanatory. The adversaries want the victim to reach them via email. Then, they will send a walkthrough in response. On the one hand, there is nothing good about this predicament; on the other, it may be possible to negotiate with the crooks and try to get the price down. The ransom for one computer typically amounts to 2 Bitcoins, but it tends to get several times bigger if the .wallet file virus infects an organization with multiple machines. Another way to learn the preliminary recovery steps is through ransom notes. The Dharma pest leaves README.txt and README.jpg files on the desktop, highlighting the essentials of data decryption.
The distributors of the .wallet ransomware chiefly use spam to deposit their bad code onto PCs. Therefore, it’s strongly recommended to refrain from opening rogue email attachments that pretend to be receipts, ISP complaints and suchlike eye-catching subjects. If the breach has taken place, be sure to start with the methods below. These techniques may help restore some files beyond the ransom method.
.Wallet extension automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by .Wallet extension
Workaround 1: Use file recovery software
It’s important to know that the .Wallet extension creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the extension under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether .Wallet extension has been completely removed
Again, file removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other extension, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this extension and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓