Crypt0L0cker 2017 decryption tool and virus removal

This article is about one of the longest-lasting online extortion campaigns to date. Originally known as TorrentLocker, the currently active ransomware called Crypt0L0cker has been around since late April 2015. Its authors have been able to get away with their filthy business because they craftily conceal their trail through the use of hard-to-track Bitcoin cryptocurrency and The Onion Router technology.
Table of Contents
What is Crypt0L0cker 2017?
Crypt0L0cker 2017 is ransom Trojan that propagates through spam, encrypts all important data on a computer and demands Bitcoins for decryption. Over the course of its evolution, the infection underwent a number of tweaks. Each one of the previous versions appended a victim’s files with a certain extension, including .enc and .encrypted. As opposed to its precursors, the edition that’s presently in rotation employs a bit of randomness in terms of labeling scrambled data entries. It concatenates a random 6-character extension to every encoded file. For example, a photograph named Pic.bmp will morph into something like Pic.bmp.ayncxo. Of course any and all attempts to open the mutilated file will return an error.
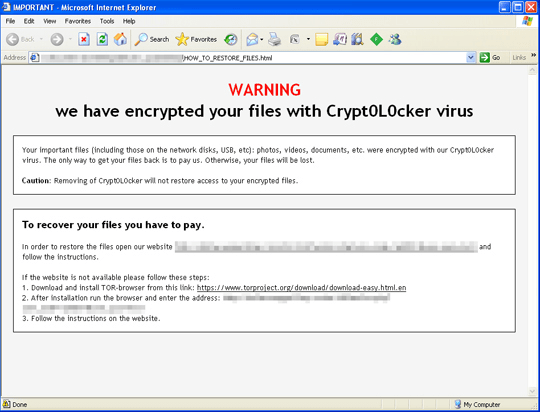
Although the new extension format is a hurdle to identification of the strain, Crypt0L0cker exhibits more characteristics that won’t leave room for doubt as to what particular threat you’re dealing with. It drops ransom notes, which are files that alert victims on the mishap and provide preliminary recovery directions. The latest variant of this crypto ransomware creates the following ransom manuals: HOW_TO_RESTORE_FILES.html and HOW_TO_RESTORE_FILES.txt. Finding them is a no-brainer, because they appear on the desktop as well as in folders containing no-longer-accessible files. The wording in these how-to documents is invariable throughout different iterations. They read, “Your important files, including those on the network disks, USB, etc.): photos, videos, documents, etc. were encrypted with our Crypt0L0cker virus. The only way to get your files back is to pay us. Otherwise, your files will be lost.”
By following the instructions, infected users end up on a Tor page that tells them to buy decryption. This transaction presupposes that a payment of about 0.5 BTC is submitted to the attackers. There is a time limit of 120 hours, or 5 days, to send the ransom, otherwise the amount will become twice as big. The plagued user can also learn the total number of their encrypted files on the “Buy Decryption” page. The criminals also provide an option to decode one file for free, the only restriction being that its size should be less than 1 megabyte.
As it’s been mentioned, the crooks at the helm of Crypt0L0cker 2017 campaign use spam as a means of payload distribution. They leverage a botnet to generate massive spam waves that deliver the ransomware downloader to thousands of computers in one hit. The attachments tend to be tricky Microsoft Word files that prompt recipients to enable macros, or ZIP archives that contain malicious JavaScript objects. No matter which infection vector is the case, opening these entities will instantly initiate ransomware deployment process in the system. If the breach has occurred and all your personal data has been locked down, the steps below should be the starting point to solve the problem. The ransom should be the last resort, so try everything alternate first.
Crypt0L0cker 2017 ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Crypt0L0cker 2017 ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by Crypt0L0cker 2017 ransomware
Workaround 1: Use file recovery software
It’s important to know that the Crypt0L0cker 2017 ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether Crypt0L0cker 2017 ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓