TeslaCrypt 2.0 removal: Howto_RESTORE_FILES.txt (.html/.bmp) and .vvv extensions

Viruses that take their victims’ files hostage are categorized as “ransomware” and are at the very forefront of cybercrime for the time being. Rather than dupe users into purchasing something they don’t need, these infections feature a viable model where one’s data actually gets encrypted and the payment is essentially the sole prerequisite for reobtaining access to the personal information. TeslaCrypt 2.0 is but one of many such threats, but its latest version’s characteristics are fairly unique.
The TeslaCrypt ransom trojan has gone through quite a few iterations before it took its current shape. Each time a new variant came live, the chiselers would improve the code to address potential weak links that were previously discovered. As a result, the end users are now facing an advanced pest that spreads regardless of geolocation attributes and the detection strength of security solutions installed on machines. One of the key ‘refinements’ is the intense involvement of exploit kits in the routine of delivering the harmful payload, making it virtually impossible to keep the contamination from taking place. The user visits a legitimate site that’s been hacked, gets redirected to the Angler EK’s landing page, and the rest of the malware injection process is then outsourced to the surreptitious program finding and harnessing security vulnerabilities in software like Adobe Flash, Adobe Acrobat, Java or outdated web browsers.
Once the initial portion of TeslaCrypt files have been uploaded to the computer via the mode described above, several malicious objects end up in the AppData\Roaming directory. One of these is a random-named executable which, when launched, disables the Command Line tool, Registry Editor, Task Manager, and MSConfig. This is, obviously, intended to prevent the victim from terminating the trojan’s operation. What also happens is the ransomware scans the machine’s hard drive, in particular its sections corresponding to letters, as well as external media if plugged in. The purpose of this activity is to locate the user’s personal files such as images in different formats, documents, PDF items, movies and many others. Incidentally, some builds of this infection are known to target the data related to popular video games, including game mods, player profiles and saved data.
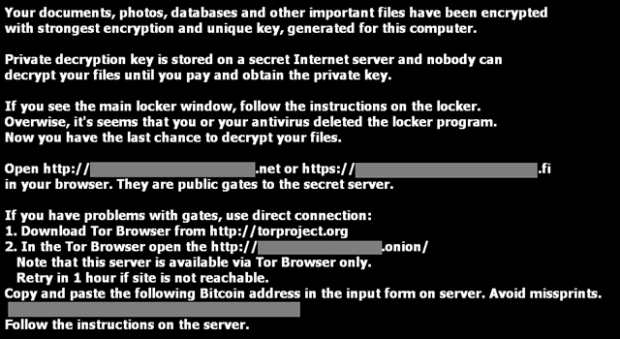
On the next phase of the attack, TeslaCrypt encrypts the detected files with AES, which stands for “Advanced Encryption Standard”. The modified desktop background, as well as the Howto_RESTORE_FILES.txt Howto_RESTORE_FILES.html and Howto_RESTORE_FILES.bmp image files that are created inside multiple folders, instruct the victim on data recovery, providing links to their personal payment pages. The extortion implies paying about $500 in Bitcoins to activate the decryption service, where the amount may slightly vary.
Aside from the encryption proper, the user’s files are also skewed in the way they appear: the .vvv or .ccc extensions will follow the original ones, so it’s an additional symptom. There have been attempts to carry out proofs of concept for brute-forcing and otherwise attacking the Advanced Encryption Standard, but they haven’t been successful for the most part. Although it may seem that TeslaCrypt victims are therefore bound to pay the ransom, it’s not quite so. Don’t fail to read and try the directions below and learn your options in this cryptographic quagmire.
Table of Contents
TeslaCrypt ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download TeslaCrypt ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by TeslaCrypt ransomware
Workaround 1: Use file recovery software
It’s important to know that the TeslaCrypt ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether TeslaCrypt ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓