Remove MySearch.com virus in Chrome, Firefox and IE [upd. Feb 2019]
![Remove MySearch.com virus in Chrome, Firefox and IE [upd. Feb 2019]](https://soft2secure.com/wp-content/uploads/remove-mysearch-com.png)
A hijacked web browser is a calamity to the user because a great deal of control over online surfing vectors is no longer at their discretion. This problem originates on the software level, where a mischievous program generically categorized as ‘adware’ gets aboard the computer in a sneaky way. The bad code changes a number of key Internet-related settings on the host system and thus leads to redirects that the admin cannot cease by regular means.
Table of Contents
What is the MySearch.com virus?
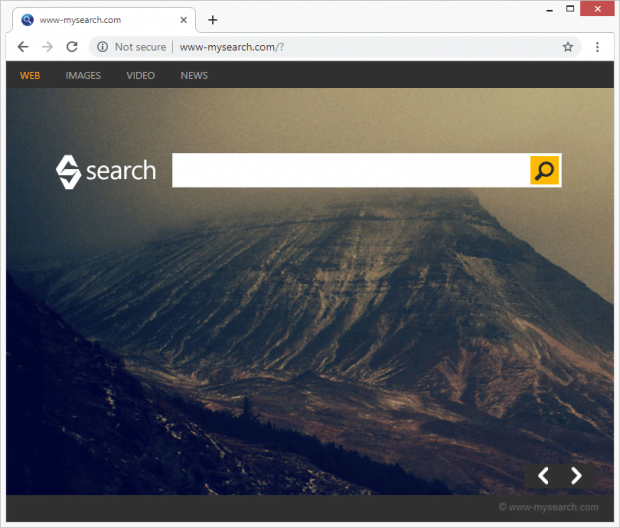
In case MySearch.com or My-Search.com keeps appearing in the location bar of multiple browsers on a PC, these repeated occurrences should be interpreted as a telltale sign of a malware issue. Obviously, since none of the above pages actually accommodates genuine data lookup value, people do not visit them purposefully. The recent spike in traffic to these domains, therefore, seems counterintuitive at first sight, but it can be explained as follows: a potentially unwanted program, or PUP, gets installed onto a machine over a workflow that requires no clear approval. This app’s automatically obtained privileges enable it to also bypass the user consent milestone when making changes to the way web navigation clients are configured.
The dissemination of MySearch.com adware hangs upon a vast multitude of setup packages available on both authoritative and semi-backstreet resources online. Bundles can work wonders promoting software on a large scale, but this efficiency is questionably favorable in the event a malicious utility is being pushed. For example, a package involving the rogue browser helper object called FullTab has been busted red-handed for a drive-by that ends up also installing My-Search.com browser redirect virus. Pro forma, the user is notified of this accompanying event on an interstitial screen of the wizard, but we’re all prone to overlooking these sorts of terms in fine print, aren’t we?
This trespass has got evident consequences. The default search and homepage in the major web browsers, including Chrome, Firefox and Internet Explorer, are the settings primarily targeted by the malign add-on in question. It doesn’t matter which URLs were assigned for these parameters before the hijack, they will be transformed into MySearch.com, Search.MySearch.com, My-Search.com or www-mysearch.com afterwards. To further top it off, the infection’s effect also applies to shortcuts for random Windows applications so that the act of executing them will co-occur with the imposed landing page popping in one’s preferred browser.
Essentially, MySearch.com is designed for ads display, where sponsored links come up above and below web results. The goal of this whole malvertising campaign, which has been afloat since 2016 all the way up to 2019, is to monetize the traffic pilfered from users so defiantly. Sponsored content on the SERPs (search engine results page) is the instrument for this guile. After all, since MySearch.com is not a site of the victim’s choice and it points to an infection, measures should be adopted to get rid of the corresponding obtrusive extension.
MySearch.com adware automatic removal
The extermination of MySearch.com hijacker can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped out from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
2. The scan will come up with a list of detected items. Click Fix Threats to get the adware removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the infection. However, it might be a good idea to consider ascertaining the adware is gone for good.
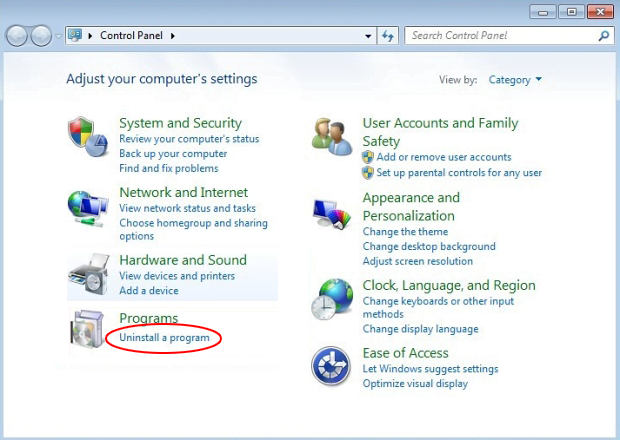
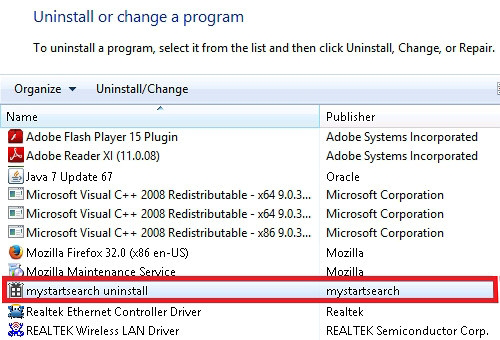
Remove MySearch.com adware using Control Panel
- Open Control Panel. On Windows XP / Windows 8, go to Add or Remove Programs. If your OS is Windows Vista / Windows 7 / Windows 10, choose Uninstall a program

- Look down the list and locate an app that appears fishy. Click the Uninstall/Change (Change/Remove) option to get the intruder removed if spotted

MySearch.com adware removal by resetting the affected browser
Please take into consideration that as effective as it is, the procedure of restoring browser defaults will lead to the loss of personalized settings such as saved passwords, bookmarks, browsing history, cookies, etc. In case you are not certain this outcome is suitable despite its obvious efficiency, it’s advised to follow the automatic removal method described in one of the previous sections of this tutorial.
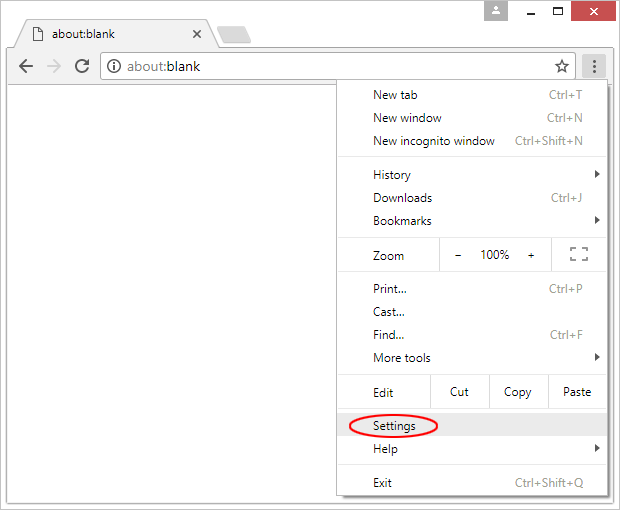
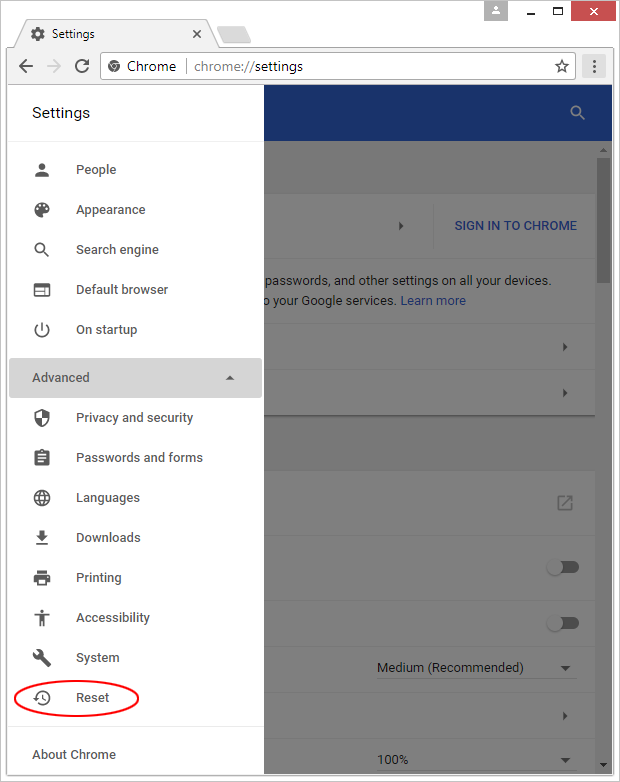
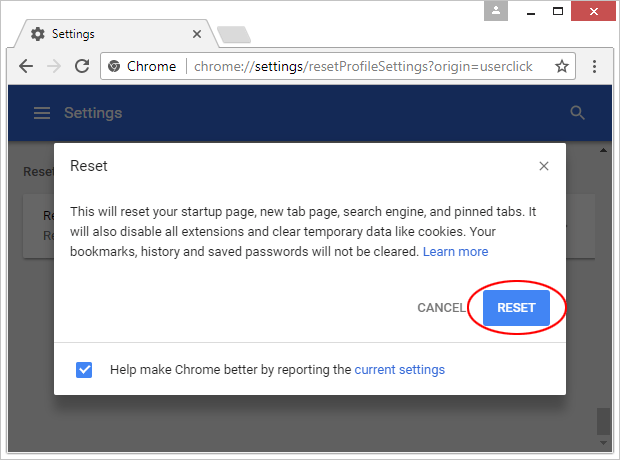
Reset Google Chrome
- Click on the Chrome menu icon and select Settings

- Locate the Advanced option under Settings and click on it to expand the menu. Then, pick the Reset button at the bottom

- When a new screen appears, hit Reset once again

- Chrome will now display a confirmation dialog box listing the types of data that will be lost if you proceed. Read the message carefully and, if you’re sure, click Reset

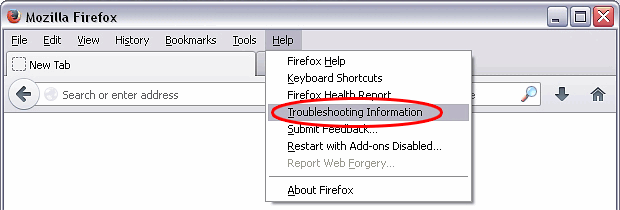
Reset Mozilla Firefox
- Click on Help menu and select Troubleshooting Information from the drop-down list, or type about:support in the URL field

- On the Troubleshooting Information screen, click Refresh Firefox option and confirm the procedure on another dialog

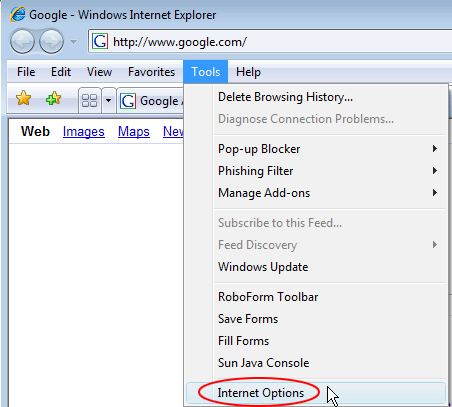
Reset Internet Explorer
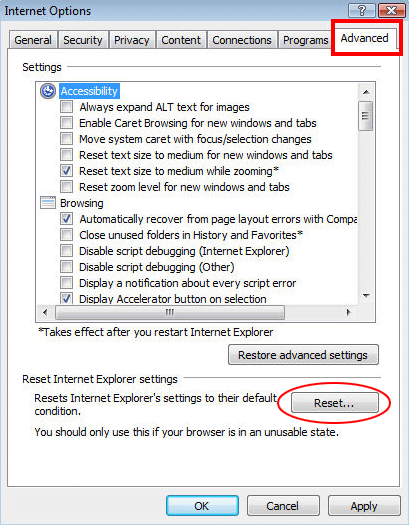
- In IE, go to Tools and select Internet Options from the list

- Hit the Advanced tab and click on the Reset option

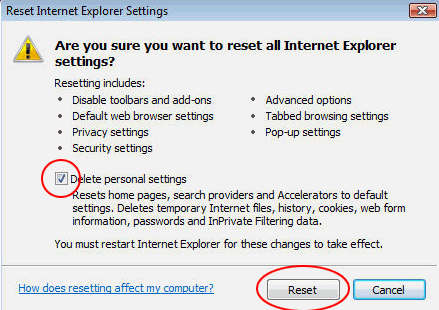
- IE will now display Reset Internet Explorer Settings box, where you should put a checkmark next to Delete personal settings option and click Reset at the bottom

Verify whether MySearch.com adware has been completely removed
For certainty’s sake, it’s advised to repeatedly run a scan with the automatic security software in order to make sure no harmful remnants of this hijacker are left inside Windows Registry and other operating system locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓