LeakerLocker ransomware breaks new ground with its tactics
Most of the extortion taking place online revolves around two things: applying crypto and locking the screen. The brand new Android ransomware called LeakerLocker utilizes one of above components and adds a unique one to the mix. It locks the home screen of an infected Android device and threatens to disclose the victim’s personal data to all their contacts.
LeakerLocker utilizes a novel mechanism for its blackmail. When trespassing on an Android device, it gains a sufficient scope of privileges to further access the user’s text messages, contacts list, personal photos, calls history and other sensitive information. The extortion involves defiant threats to hand over the entirety of this personal data to everyone from the infected person’s telephone and email contacts list. Therefore, while clearly being a ransomware strain, this sample does not engage cryptography in its modus operandi. Instead of encrypting files, it claims to transfer them to a “secure cloud” only the perpetrators can access. This unsanctioned data backup is the core of the whole extortion as it’s the commodity being held hostage.
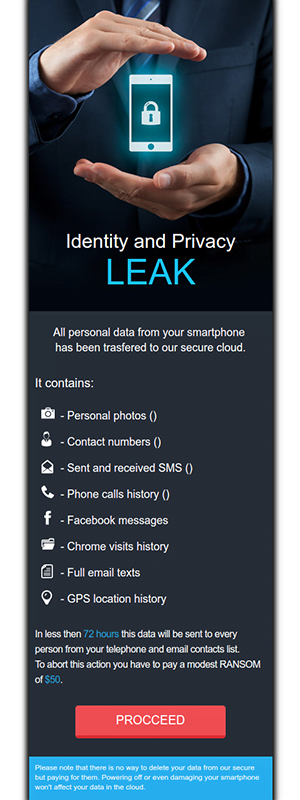
The LeakerLocker attack chain is accompanied by a classic indicator of compromise, a warning message that replaces the victim’s home screen. It reads, “Identity and privacy leak. All personal data from your smartphone has been transferred to our secure cloud.” Then goes a list of stolen information which, aside from the data mentioned above, also includes Facebook messages, Chrome visits history, full email texts, and GPS location history. The blackmail part at the bottom says, “In less than 72 hours this data will be sent to every person from your telephone and email contacts list. To abort this action you have to pay a modest ransom of $50.”
LeakerLocker ransomware is making the rounds via trojanized applications on Google Play. These apps are called “Wallpapers Blur HD” and “Booster & Cleaner Pro”. Google has removed both from their official download portal, but they had been installed on thousands of Android devices prior to this move. The categories that the apps fall under are popular with users, so no wonder they managed to get so many installs in a relatively short time span.
Each one of the booby-trapped programs displays a standard-looking permissions dialog during the setup process, a thing that people hardly ever peruse. In the upshot, granting these privileges allows the ransomware to gain a foothold on the device. The payload first launches a component named com.robocleansoft.boostvsclean.AdActivity, which ends up locking the screen. Then, it downloads some extra code from its Command & Control server in the background. This code performs reconnaissance on the device, harvesting a variety of private information.
It’s not fully clear at this point whether LeakerLocker will carry through with its threats if the 50-dollar ransom isn’t paid within three days as demanded. However, experts confirm its ability to collect a victim’s PID (personally identifiable data), so chances are it’s as menacing as it appears. Ultimately, it turns out that extortionists can do without crypto, so LeakerLocker ransomware is a game changer in a way.
Posted in: KnowledgeBase
Leave a Comment (0) ↓