Decrypt CRBR Encryptor ransomware and remove virus
According to recent reports on computer threat landscape, the Cerber ransomware family is the dominating one in its niche of cybercrime. It holds the top position owing to a number of characteristics. First off, the distribution channels have been consistently well-thought-out. Secondly, its code boasts anti-virtualization features to prevent analysis, and the crypto is uncrackable. The latest variant called CRBR Encryptor inherits all of these hallmarks.
Table of Contents
What is the CRBR Encryptor ransomware?
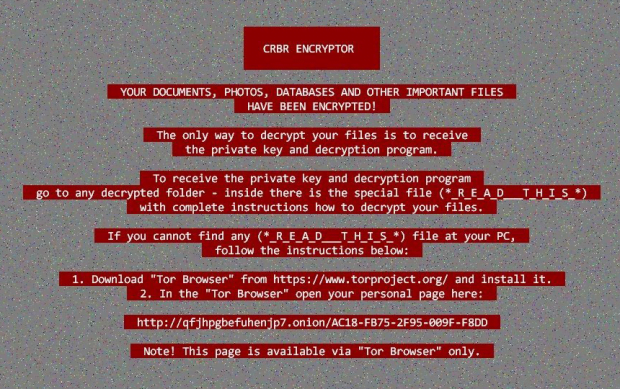
CRBR Encryptor is a new iteration of the Cerber ransomware, which gained notoriety for super-robust encryption, clever AV evasion and large-scale propagation. While said edition isn’t equipped with a bevy of new characteristics, the changes do come to the fore. The most prominent tweak is of course the name. The infection now replaces the victim’s desktop wallpaper with a JPEG image containing an allusion to CRBR Encryptor instead of Cerber. While a couple of earlier builds would indicate the version number next to the name, the one under scrutiny doesn’t. The rest of the warning text is pretty much a copy of the previously used wording, except it references “special files” named *_R_E_A_D___T_H_I_S_*. These are new ransom notes dropped in two different formats, _R_E_A_D___T_H_I_S___[random]_.hta and _R_E_A_D___T_H_I_S___[random]_.txt.
One of the two prevailing distribution vectors for CRBR Encryptor is spam. The current spam campaign involves emails disguised as though they were from Microsoft Security Team. According to the body of these messages, something unusual about recent sign-in activity to the Microsoft account has been detected. To get further instructions, the recipient is urged to check out the attached ZIP file. This attachment contains malicious JavaScript that ends up downloading the CRBR Encryptor executable onto the machine behind the scenes. Another propagation method is all about the use of the Magnitude exploit kit. This way, the threat actors spawn malicious payloads via a network of compromised sites, where embedded code checks the host system for known vulnerabilities and uses them to inject the infection.
This particular Cerber variant sticks with the same cryptographic routine as before. It still uses a symmetric AES key to render data inaccessible and then additionally encrypts this key with RSA, a yet stronger public-key cryptosystem. These two layers of cipher, if implemented correctly, pose a rock-solid obstacle to recovery. CRBR Encryptor looks inside local drives, removable drives and network shares to locate potentially most valuable files for the victim. When the crypto part has been completed, it additionally renames files to random 10 characters. It also substitutes the original extensions with a string consisting of four hexadecimal characters, making an arbitrary sample entry look similar to this: Nq0a71pRMz.a29s. The newly assigned extension is going to be the same for all data belonging to a specific victim. That’s because the ransomware fetches it from MachineGuid, a value uniquely assigned to the PC.
In its *_R_E_A_D___T_H_I_S_* ransom manuals, CRBR Encryptor provides up to five Tor links leading to the victim’s personal page. When the user follows one of them, they end up on a page titled Cerber Decryptor that demands 0.5 Bitcoin for the private key and decryption tool. If this sum isn’t submitted during five days, the ransom increases to 1 Bitcoin. At the end of the day, those infected have to make a choice: to pay up or try to get their files back by alternative means. Note that the former is a slippery slope with no guarantees that the threat actors will stay true to their promises.
CRBR Encryptor ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download CRBR Encryptor ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by CRBR Encryptor ransomware
Workaround 1: Use file recovery software
It’s important to know that the CRBR Encryptor ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether CRBR Encryptor ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓
![CRBR Encryptor’s _R_E_A_D___T_H_I_S___[random]_.hta ransom note CRBR Encryptor’s _R_E_A_D___T_H_I_S___[random]_.hta ransom note](https://soft2secure.com/wp-content/uploads/crbr-encryptor-_r_e_a_d___t_h_i_s___-hta-620x318.png)


