A Guide on Security Your Data and Online Privacy in Easy Way

Table of Contents
Digital media and privacy on the Internet
Digital media provide an easy, efficient and inexpensive way to share information, therefore have become an indispensable part of the daily work and leisure of a large number of people. Many services available online require users to register during which they need to submit personal information, most often an email address, name, and surname. Providing personal information such as last name and first name, year of birth or address Housing with an online application is a common occurrence, but it is easily possible to do your own thing if you give personal data to fraudsters and thus risk “identity theft”. One of the ways identity theft occurs and the way personal information is taken from us is called phishing.
Every internet user has a digital reputation and identity. It is acquired by publishing various content or by visiting websites. The contents can be positive or negative, and you can publish them yourself or someone can publish them for you. Everyone publishing content that includes you also creates your digital footprint. Every time we visit a website where we leave our data, we also leave our digital footprint. That is why it is important to separate private identity from the public. It is also important to protect your identity because in this way we reduce the digital traces that we leave on the Internet and the possibility that content about us is available on the Internet which we do not want.
Threats to privacy and identity
From the very beginnings of the human race, it was clear how to deal with certain information and act with confidence. Information security is often associated with computers and computer networks, but it should be noted that when we talk about information security, we’re not just talking about data stored on computers, but about everything information that needs to be protected from unauthorized access, alteration or destruction, regardless of the form and location where this information is stored. In today’s age of information, most companies and institutions rely on just that information system to accelerate improvements or, for example, centralize their own business.
Educational institutions, following this mode of action, do the same. Adequate protection of personal data remains a major challenge they face Internet users, schools, businesses, and the government. Technology can be threatening at the same time and protect privacy which largely depends on the way we use it. In the digital environment, the same postulates should be used as in the physical one. Such as we would never give personal information to someone we meet on the street, by the way, the same is the way to think when it comes to the digital world. Probably, in this case, the danger is even greater, since data can now be more easily sold or used for “Identity theft” but as early as possible.
Use an antivirus program
Be sure to install an antivirus program on your computer. If it is a personal computer, many programs on the market will prevent most attacks. If it is a business computer, then the company/organization you work for needs an antivirus program for efficiency in finding and removing viruses and other malicious programs that try to infect your computer.
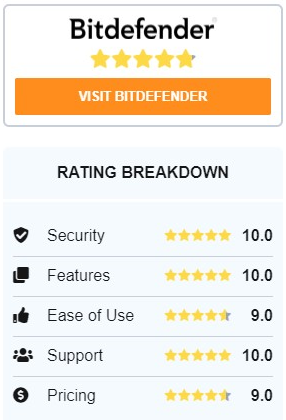
Bitdefender Antivirus is software that is constantly first at the top of the rankings when it comes to antivirus websites. This is really about good software, not “self-promotion” like some others do. It brings you basic functions, which means excellent protection against viruses, malware, ransomware, phishing, and other dangers lurking on the Internet. Furthermore, Bitdefender also offers real-time protection, which is a good thing. It takes little computing resources, but in the long run, it is profitable. Bitdefender is growing day by day and is in step with the best antivirus software. Make it easy for yourself, be safe and secure.
Operating system vendors regularly publish contributing security updates on computer security. By correcting security vulnerabilities, these updates prevent viral infections and other malicious attacks. Regular updates are very important because attackers can analyze the update immediately after posting it and try using it on all computers that are not updated.
A comprehensive model of data and content protection
The protection of digital content and personal data is a topic that needs to be constantly addressed when using a computer, whether personal or business context. If we do not think about protection and take appropriate steps, how if both we and the system were safe, we would most likely fall victim to someone’s malicious programs or malicious persons, or hackers. Unfortunately, most users today do not think about protection. Speaking today about the protection of computers, information systems, and digital content, it is very essential to have a comprehensive protection model. Comprehensive protection is the approach that protects information systems from as many parties as possible to make them more resistant to the various attacks we encounter. The model of comprehensive protection is based on five pillars that form a coherent whole.
These are computer security (with the help of regular updates, antivirus programs, and firewall) data security (data encryption and use of encrypted links for exchange data) network security (with our network administrators playing the biggest role, we are left to avoid connecting to the so-called unsecured networks) physical security (taking care not to leave the computer accessible to foreign people, keeping in mind the first rule of safety: If you allow someone physical access to the computer, it is no longer your computer) policies and procedures and user awareness.
With the advancement of technology most threats can be prevented, but with the necessary assumption: it is necessary to raise the awareness of users about potential hazards.
Always be careful, do not allow yourself to be put in an unwanted situation. Safety and security come first.
Posted in: KnowledgeBase
Leave a Comment (0) ↓