Goldeneye ransomware: decrypt and remove trojan virus
Most ransomware programs encrypt one’s personal files while keeping the operating system intact. Some, however, will hold the whole computer hostage, denying access to the target system altogether. The latter cluster isn’t as vast, with the most widespread strains being HDDCryptor, aka Mamba, the Satana bootkit, and Petya. The newest sample called the Goldeneye ransomware is a direct descendent of the Petya family.
Table of Contents
What is the GOLDENEYE ransomware?
Goldeneye is an offending program that overwrites the Master Boot Record (MBR) of an infected machine and encrypts its master file table (MFT) so that the victim ends up completely locked out of their PC. It was first spotted in the wild on December 6, with most of the contamination reports coming from Germany. The ransomware operators are leveraging a spam-backed tactic to spread the malicious payload. The campaign revolves around phishing emails impersonating a construction firm. The .xls job offer attached to these rogue messages returns a dialog to enable Excel macros. The criminals thereby take advantage of a macro vulnerability to launch the attack. The malefactors are likely to add more spam themes to their distribution strategy in the near future.
As soon as the Goldeneye payload is dropped, the ransomware starts with encrypting the victim’s important files. As a byproduct of this workflow, it concatenates a user-specific 8-character extension to the original filenames. The pest leaves a ransom note called YOUR_FILES_ARE_ENCRYPTED.txt, which outlines the process of decrypting the hostage data. Furthermore, it affects the Master Boot Record, replacing it with a custom boot loader. Essentially, this stage of the compromise is pretty much identical to the impact of regular file-encrypting ransom Trojans. This is the threat actors’ plan A.
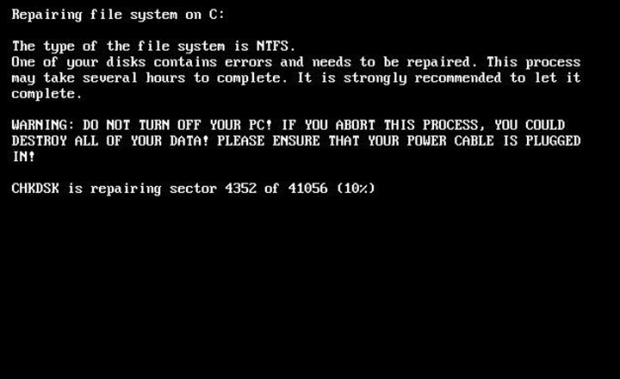
The plan B is much more devastating. Its objective is to completely block the infected PC. To this end, the Goldeneye ransomware attempts to automatically reboot the machine, disguising the subsequent crypto routine with a phony system maintenance notification. It displays a screen that says, “Repairing file system on C:”, with a spoof CHKDSK operation progress indicator at the bottom. To make sure the victim doesn’t abort this process, the screen contains a warning that highlights the possible critical damage, including data loss, if it happens. This whole trickery is nothing but a way to conceal the actual adverse activity of Goldeneye encrypting the master file table behind the scenes.
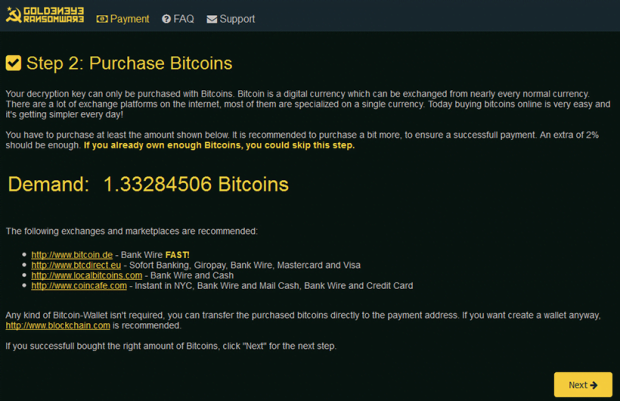
Ultimately, MFT encryption prevents the computer from booting up. The victim will bump into a lock screen that informs them of the attack deployment and provides a number of steps to kick off with the recovery. The infected user is instructed to visit the decryption service page using the anonymous Tor Browser. On the Goldeneye payment page, the step 1 is to enter the victim’s personal identifier. Step 2 is to purchase 1.3 Bitcoins, which converts to about 1,000 USD. Then finally on step 3, the extorted amount of cryptocurrency must be submitted to the criminals’ Bitcoin address.
In ransomware attack scenarios, some users opt for the lesser of two evils and pay the ransom to get their personal data back. This route should be one’s last resort, though. The first thing to do is check whether alternative recovery techniques can do the trick. Be sure to scrutinize the manual below and try these recommendations to defeat the Goldeneye ransomware adversary.
Goldeneye ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Goldeneye trojan remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by Goldeneye ransomware
Workaround 1: Use file recovery software
It’s important to know that the Goldeneye ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether Goldeneye ransomware has been completely removed
Again, trojan removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓