Remove Petya ransomware and decrypt files
The word “Petya” is the transliterated informal for Pyotr, a popular Russian name. A lot of its recent implications, however, have to do with a big computer security issue. Cybercriminals who are most likely operating from the above-mentioned state have devised a highly destructive piece of malicious code and named it the “Petya ransomware”. Not only does it encrypt one’s data but it also prevents victims from even launching the OS.
The modus operandi of the crypto virus in question explicitly demonstrates how rapidly this darknet industry’s mechanisms are advancing. Years back, ransomware infections would lock Windows and extort a fee under false pretenses of alleged law violations. Then, there was a shift toward a domination of file encryption techniques in this underground domain. Now, the scoundrels have come to combine the two – they are both locking computers and encrypting data. This is an extremely hard-to-tackle predicament, with no remedy available thus far. The Petya ransomware therefore denotes a whole new milestone that security experts around the world will have to come up with countermeasures for.
What this cyber threat does at the beginning of the attack is it substitutes the Master Boot Record with a malign payload. Since the task of MBR is to instruct the machine how to load Windows correctly, such a replacement has a critical impact upon the way the operating system launches. For these changes to take effect, the bad code forces the computer to reboot. The user will then see a counterfeit CHKDSK screen whose percentage progress designates a dangerous crypto routine rather than the claimed disk checking job. The ransomware actually encodes the so-called Master File Table, which leads to a devastating outcome because the PC will become completely blind in terms of establishing associations with the files stored on the hard drive.
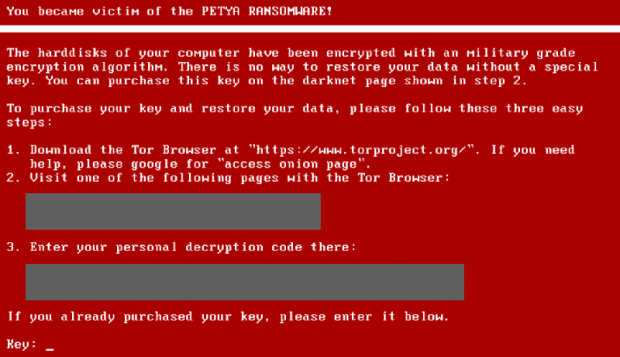
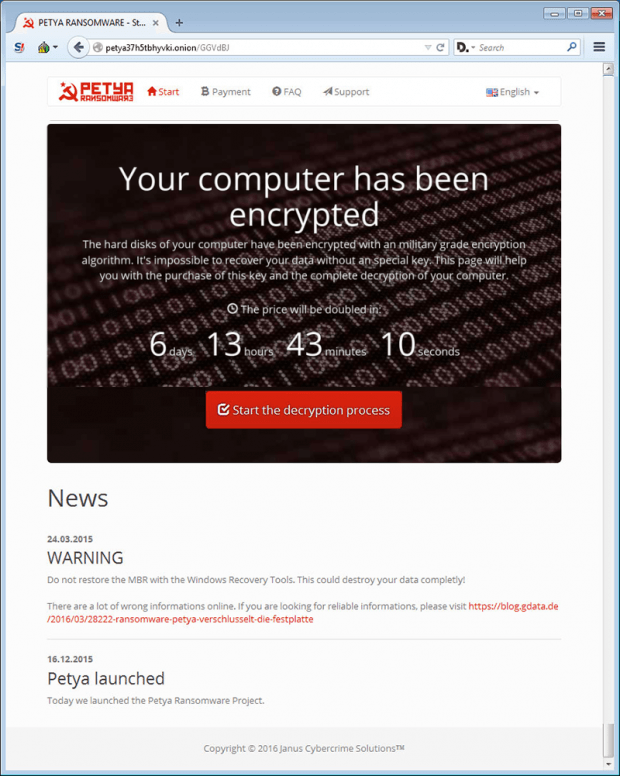
The next phase of the assault is accompanied by a lock screen that straightforwardly tells the victim what happened. In particular, it says “You became victim of the Petya Ransomware! The harddisks [sic] of your computer have been encrypted with an [sic] military grade encryption algorithm. There is no way to restore your data without a special key.” The attackers list several steps for recovery. The user needs to visit a CAPTCHA-protected Tor site, put in their personal decryption code provided on the warning screen, and submit about 1 BTC in exchange for a password that will unlock the PC and data.
Petya is also non-standard as far as the circulation is concerned. The perpetrators are conducting a spam campaign, where legit-looking emails encourage users to follow an embedded link and download a file hosted on Dropbox. The contagious folder contains a JPG image as well as an executable file which, once opened, covertly contaminates the system.
With no completely efficient ways to remediate infected computers at this point except coughing up some Bitcoins, users should try basic steps that may partially help.
Table of Contents
Petya ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Petya ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by Petya ransomware
Workaround 1: Use file recovery software
It’s important to know that the Petya ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether Petya ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓