GandCrab v4 ransomware: how to decrypt .KRAB files

The GandCrab ransomware strain has been demonstrating amazing durability throughout its eventful timeline. Even the seizure of its Command and Control servers earlier this year didn’t stop the campaign in its tracks. Moreover, the pest is mutating, now stuck at version 4. The latest variant has quite a few new features under the hood. Keep reading to learn what those traits are.
Table of Contents
What is the .KRAB ransomware?
What Windows users refer to as the .KRAB virus is actually one of the few known editions of GandCrab, a ransomware species tailored professionally enough to become today’s top crypto extortion threat. Notice the dot before the capitalized combination – it means it’s an extension that the blackmail malware in question adds to every hostage file on a victim’s computer. For the record, this is a symptom of GandCrab v4, a mod that was released in early July 2018. This one is barely a game changer, but it does have a few distinctions that make it stand out from the forerunners. Aside from the extension proper, it introduces a new name of the rescue note, a different encryption tactic, as well as a new Tor page designed for ransom payments.
As far as the spreading mechanisms go, the .KRAB variant of GandCrab virus takes the previously used vectors a notch further. Another fresh technique is the involvement of pseudo cracks for widespread applications. These sorts of tools have traditionally enjoyed popularity with users as they can activate various programs without a license. The crooks in charge of the crypto culprit under scrutiny have set up a number of fake sites that push those cracks. Once a user follows the embedded link to download what they think is a wonderful applet, they unwittingly opt for the infection. GandCrab v4 is stealthy enough to slip below the radar of antimalware tools, so it’s likely that the trespass will take place unimpeded.
The infiltration stage is followed by a system-wide scan for potentially important data. The ransomware uses a predefined set of extensions to find all the matching files inside the host. It looks for hundreds of file types, including Office documents, databases, videos, pictures and so on. Whatever it spots during this traversal is subject to encryption. As opposed to previous versions that employed the RSA cryptosystem to lock down users’ data, the current one leverages an algorithm known as Salsa20 stream cipher. It’s unclear why the unscrupulous devs have decided to change their tactics in this regard – the earlier utilization of RSA was flawless and didn’t yield to decryption beyond ransom. Anyway, GandCrab v4 appears to be all about fine-tuning.
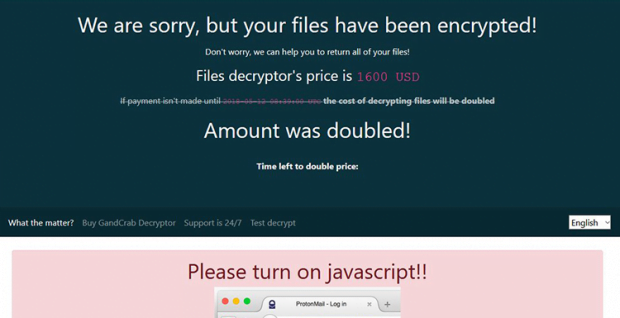
A byproduct of data scrambling on the inside is accompanied by a change on the outside. It’s the .KRAB string being concatenated to each encrypted object. Then, the pest drops a ransom note named KRAB-DECRYPT.txt onto the desktop and into folders with crippled data. It coerces the victim to visit a specially crafted payment page residing on the anonymous Tor network. The page lets the user know what they are supposed to do to redeem their valuable files. In particular, it includes the amount to be paid, and the deadline during which the payment is to be made. The original size is usually the Dash or Bitcoin equivalent of 1,200 USD. However, some victims have reported lower ransoms amounting to $800 worth of the specified cryptocurrency. After three days of nonpayment, the sum doubles.
All in all, the .KRAB file ransomware is a serious cyber adversary that keeps up the trend established by the sophisticated GandCrab ransomware lineage. It cannot be decrypted for free so far, so the options are to either buy the criminals’ decryptor or resort to some of the best practices of forensic data restoration. The latter strategy is highlighted below.
.KRAB extension automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download .KRAB ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the extension and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by .KRAB extension
Workaround 1: Use file recovery software
It’s important to know that the .KRAB extension creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the extension under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether .KRAB extension has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the extension itself does not belong inside your computer. Incidentally, it often comes with other extension, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this extension and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓