Gandcrab ransomware removal: how to decrypt GDCB virus
A new sophisticated strain of ransomware called GandCrab has been wreaking havoc since early February. It turned out to be revolutionary to an extent as it has pioneered in accepting altcoins for ransoms that no other blackmail malware family has used before. Furthermore, it boasts a diversified distribution routine that keeps evolving.
Table of Contents
What is the GandCrab ransomware?
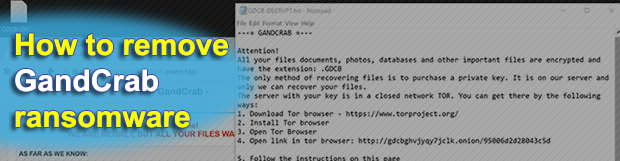
GandCrab represents a new generation of ransom Trojans featuring well-orchestrated propagation, advanced antivirus evasion, unbeatable crypto and a robust Command and Control infrastructure. With the general decline of ransomware prevalence on the cybercrime arena since late 2017, the emergence of a sample as high-tech as this one is quite an event. At the time of this writing, the architects of this extortion wave have released GandCrab v2.1. It is hardly different than the original variant, except that the spreading workflow has become more flexible. As before, the latest edition of the culprit adds the .GDCB extension to encrypted files and drops a rescue manual named GDCB-DECRYPT.txt.
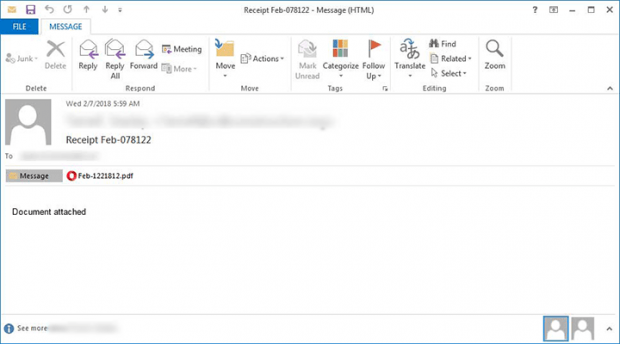
The tweak in the distribution methods is tangible. Whereas the previous version made the rounds via exploit kits, including RIG and GrandSoft, the current one reaches computers via malicious spam. Although this appears to be a downshift in terms of technical complexity, the success rate of payload deployment has probably grown. The adversaries leverage a botnet to mass-mail potential victims. The phishing emails being sent pretend to be receipts, with the subject being “Receipt Feb-[random numbers]”. The body of the message is prosaic, saying, “Document attached”.
The catch is all about the attachment camouflaged as a PDF file. Once a recipient opens it, they end up on a screen with a captcha where they are supposed to put a checkmark to confirm they aren’t a robot. Next, the rogue PDF object downloads a booby-trapped Microsoft Word file from butcaketforthen.com web page and loads it. Then goes a garden-variety “Protected View” notice asking the victim to enable editing and thus run Office macros. The malicious macros, in their turn, download and fire up a PowerShell script that completes the infection chain and executes the GandCrab ransomware binary on the targeted host.
The perpetrating program first traverses the contaminated machine’s hard disk partitions, removable drives and network shares in search of potentially valuable data. Before encrypting the detected items, it ends multiple processes that may be currently using some of the would-be hostage files. It also determines the victim’s IP address and geolocation in order to display this information in its decryption service page later on. Having received a public encryption key from its C2 server, GandCrab performs the data crippling job by means of RSA, asymmetric cryptographic algorithm.
A notable byproduct of this file skewing, aside from denial of access, is the concatenation of the .GDCB string to every encoded entry. The ransomware also leaves its recovery how-to document, GDCB-DECRYPT.txt, in folders with hostage data and also drops a copy on the desktop. Ultimately, the victim is instructed to visit the “GandCrab Decryptor” page. It is a Tor hidden resource designed for processing the ransom payments. The infection demands 1.54 Dash, a form of cryptocurrency that’s used by ransomware makers for the first time. No matter how big the temptation might be to pay the cybercrooks, get the data back and move on with your day, be sure to try everything else first. Start with the steps below to remove the GandCrab ransomware and check whether forensics can do the trick in terms of data recovery.
GandCrab extension automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download GandCrab ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the extension and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by GandCrab extension
Workaround 1: Use file recovery software
It’s important to know that the GandCrab extension creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the extension under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether GandCrab extension has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the extension itself does not belong inside your computer. Incidentally, it often comes with other extension, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this extension and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓