GandCrab 5.0.4 ransomware: decrypt and remove
The darkest side of the cryptographic science is all about ransomware. This is a category of aggressive computer code that makes users’ data inaccessible by encrypting it, and then demands money for recovery. By the way, these ransoms are typically payable in cryptocurrencies only, which is another abuse case somewhat related to cryptography. GandCrab 5.0.4, for instance, is the latest release of a common ransomware family that follows this exact tactic. Here’s the full profile of this variant.
Table of Contents
What is the GandCrab 5.0.4 ransomware?
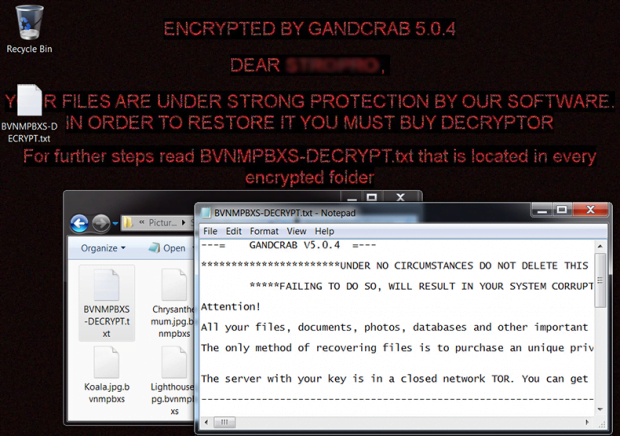
GandCrab 5.0.4 is a malicious upshot of fine-tuning endeavors made by the architects of GandCrab, one of the dominating and most progressive ransomware families currently in the wild. While differing a lot from the earlier iterations, this mod is nearly identical to the other sub-versions of this infection’s fifth generation. It still displays a gloomy desktop warning, concatenates random extensions of variable length to filenames, and drops basically the same ransom message into encoded folders. There is one crucial thing, though, that makes it stand out from, say, GandCrab v5.0.3. Whereas the latter is crackable, courtesy of the groundbreaking decryption tool by BitDefender, the edition under scrutiny already accommodates mechanisms that thwart the simple data restoration process. So, yes, it looks just like its immediate precursor on the outside, but functionally it’s revamped cyber-beast.
GandCrab 5.0.4 attacks Windows computers in a number of ways. None of these techniques is unique or super-sophisticated, but the competently orchestrated distribution campaign is what matters the most in terms of delivering the harmful program to thousands of PCs. The bulk of the infection instances have to do with spam. Some “affiliates” of the GandCrab RaaS (Ransomware-as-a-Service) network are in cahoots with botnet owners and can therefore deploy automated malspam waves to disseminate the dangerous payload. The users being targeted usually receive fabricated invoices, updates for some service subscription terms or other potentially intriguing messages with trojanized documents attached to them. The rest of the attack chain is a matter of the recipient launching a toxic Office macro or running a masqueraded JavaScript file, which results in stealthy malware download.
Sometimes the infection arrives through exploit kits that put the target host’s software vulnerabilities to bad use. In this case, there is hardly anything the user can do to prevent the incursion, moreover, it’s nearly impossible to even notice it happening. On-time application patches can help, but not everyone is as prudent as that. Yet another trick utilized by the peddlers of GandCrab 5.0.4 virus comes down to app bundles, where the troublemaking installer is craftily hidden underneath several other components of a freeware setup.
As soon as the nefarious digital dodger makes its way into a system, it shuts down the VSS (Volume Snapshot Service), usurps elevated access privileges and establishes persistence. Then, it scans all the local, attached and network disks for files with certain extensions that match its built-in list of data to find. This method allows the ransomware to spot most of the victim’s personal files. Next, cryptography enters the wicked game, with GandCrab v5.0.4 employing a virtual alloy of AES and RSA ciphers to lock down everything detected during the above-mentioned scan. Each encoded file is then appended with a random extension whose length can be up to nine characters. For example, a photo named Selfie.bmp will transform into an entry like Selfie.bmp.akwqnpko.
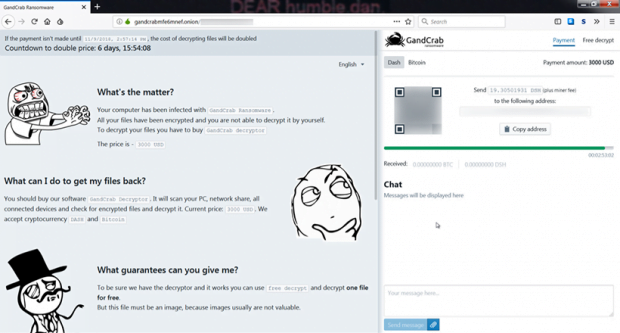
The ransomware also leaves a ransom message whose name begins with the same string as the new file extension, only with every character capitalized. In this hypothetic attack, it’s going to be AKWQNPKO-DECRYPT.txt. This document instructs the victim to install Tor browser and visit their personal payment page there. The demand is to pay a sum amounting to $800-$3000 worth of cryptocurrency (Bitcoin or Dash) until a specified date and time, otherwise the price will double. Notice the huge range in the ransom size – that’s an indication that different “affiliates” of this RaaS model have different commercial appetites. All in all, this is an awful predicament to come across, but the victims shouldn’t hurry with their payment. First off, the previously released free decryptor may be updated sometime soon to support GandCrab version 5.0.4. Secondly, there are alternative tips and tricks that may help reinstate the ransomed data. See below for more information.
GandCrab 5.0.4 ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download GandCrab 5.0.4 ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by GandCrab 5.0.4 ransomware
Workaround 1: Use file recovery software
It’s important to know that the GandCrab 5.0.4 ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether GandCrab 5.0.4 ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓