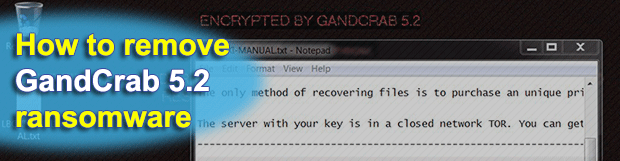
“Encrypted by GandCrab 5.2” – remove and decrypt ransomware virus
Here we go again, today’s most sophisticated and prolific ransomware called GandCrab has been updated and the new variant is already in the wild. GandCrab 5.2 is the version name, and it’s more competently designed than the predecessor in several ways. The fact that this build is not decryptable, unlike the forerunners, is perhaps the most serious concern.
Table of Contents
What is the GandCrab 5.2 ransomware?
There is no ransom Trojan inciting as much public discussion as GandCrab nowadays. It has been in rotation for more than a year now, and despite quite a few ups and downs of the campaign it’s afloat and continues to evolve. The seizure of the extortionists’ servers by law enforcement in early 2018 and several breakthroughs in terms of cracking the underlying cryptography – none of these have stopped the crooks in their tracks.
This time, shortly after researchers found a way to decrypt its editions up to version 5.1, the brand new GandCrab 5.2 was out that circumvented the benign efforts. The outward changes that stem from the tweak aren’t as dramatic as ones on the inside, which boil down to enhancements in the crypto implementation. The first symptom most victims encounter once the attack takes place is the “Encrypted by GandCrab 5.2” alert that replaces the desktop background image on the contaminated computer.
Just like the build that this variant has superseded, the raid in full swing starts with a scan of the host machine for common types of data. The logic of this process is about mapping all files on the local hard disk, removable media and network drives against a list of formats that the infection goes with. Given the improved data lookup algorithm in GandCrab 5.2, the scan takes very little time and runs entirely in the background in order not to attract the victim’s attention.
Once this routine is completed, the ransomware move on with the attack chain by applying a military-grade cipher to the spotted documents, images, videos, databases, and other potentially valuable items. The crypto is a rock-solid composition of AES and RSA standards, where the only viable recovery method requires the private key. This fragment of secret information, though, doesn’t touch the plagued computer and resides on the crooks’ Command & Control server. This is the fundamental issue with restoration of ransomed files regardless of the strain.
As soon as the scan and encryption milestones of the attack are reached, GandCrab 5.2 does a few things to let the victim know what happened and how to act. One of the external quirks is the concatenation of a random-looking extension to all hostage files. This is a string allocated uniquely to every user, and it consists of up to 10 characters. An example would be a distortion of a file named Meadow.jpg into Meadow.jpg.bxlqi or similar. This way, the victim will know for sure what has been encoded. Additionally, as mentioned above, the virus substitutes the desktop wallpaper with a warning message that reads, “Encrypted by GandCrab 5.2. Dear [username], your files are under strong protection by our software, in order to restore it you must buy decryptor”.
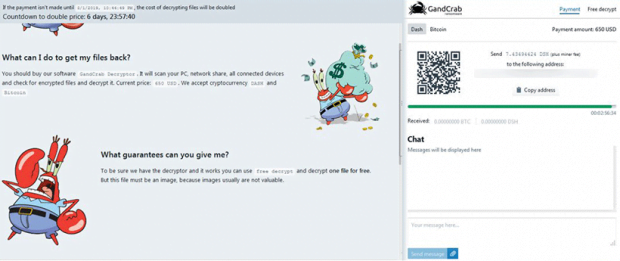
This brings us to the ransom note that the victim is told to read for further details. Interestingly, the name of the rescue file may vary – that’s something new for the campaign. Originally, when GandCrab 5.2 was just released, its instances dropped notes named [VICTIM ID]-DECRYPT.txt. The part in brackets is the same as the newly assigned file extension, only an uppercase one, so in our hypothetical onslaught it’s going to be BXLQI-DECRYPT.txt. Somewhat later, the operators of several sub-campaigns have switched to the following naming pattern for the ransom note: BXLQI-MANUAL.txt. The contents of both copies are identical, though, and coerce the user to visit a Tor-hosted payment page asking for 650-1,200 USD worth of Bitcoin or Dash cryptocurrency coins.
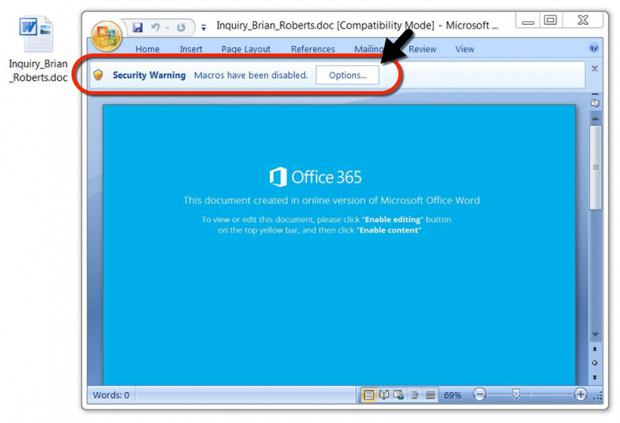
The current version of this major crypto hoax is distributed in quite a few different ways. The dominating attack vector is all about malicious spam, where the booby-trapped email attachments are disguised as an official inquiry of some sort, an invoice, or other eye-catching subject. When opened, the Microsoft Word macros trick comes into play as the recipient is encouraged to “enable content” to view the information inside. Doing so will trigger a script that downloads GandCrab 5.2 onto the PC. Another method of payload delivery that’s gearing up for a rise is RDP hacking. By compromising poorly protected remote desktop services, the malefactors are able to inject and execute the ransomware manually.
Furthermore, in quite a few reported cases the malicious binary was dropped via an exploit kit, such as the notorious Fallout EK. This technique is quite stealthy as well, because the perpetrators take advantage of unpatched software vulnerabilities on the computers whose users visit compromised sites. The impact is uniform regardless of the breach vector: the personal data gets encrypted and cannot be reinstated unless a ransom is paid within the deadline. While this might, indeed, turn out to be the only option to get the files back, a few workarounds below can be worth their salt.
GandCrab 5.2 ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download GandCrab 5.2 ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by GandCrab 5.2 ransomware
Workaround 1: Use file recovery software
It’s important to know that the GandCrab 5.2 ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether GandCrab 5.2 ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓