Decrypt and remove GandCrab 5.1.0 ransomware virus
What makes ransomware a groundbreaking phenomenon in the cybercrime landscape is that there isn’t and cannot possibly be a one-size-fits-all cure for it, contrary to virus signatures allowing security solutions to fix virtually any other malware issue. One of the strains at the forefront of this ecosystem has spawned a new variant called GandCrab 5.1.0 in mid-January 2019. Here’s the comprehensive profile of this nasty infection.
Table of Contents
What is the GandCrab 5.1.0 ransomware?
Real-world experience shows that only well-established ransomware families go the route of heritage. These prolific lineages produce malicious cyber offspring every now and then, each iteration featuring certain functional enhancements along with external tweaks. GandCrab is presently dominating this niche, having been in rotation for nearly a year and made enough noise in the security community to become a buzzword, really. The latest version of this king of the crypto extortion underground is GandCrab 5.1.0. It supersedes the previous 5.0.4 build. Compared to the forerunner, the newcomer isn’t much of a breakthrough whatsoever. Its outer manifestation is almost identical, including the desktop wallpaper and wording of the ransom note. Whereas some might consider this lack of big changes to be a sign of the crooks’ negligence, malware analysts aren’t so optimistic. Here’s why.
With only minor alterations made on the outside, GandCrab 5.1.0 boasts an improved encryption mechanism. Specifically, it applies the cipher in a much more time-efficient manner than its precursors did. The faster the unauthorized crypto routine the less likely it is that the victim takes notice of the onslaught and adopts an emergency measure, such as terminating the malicious process via Task Manager or powering down the computer. All in all, the current mod outstrips the predecessor considerably, except that most victims aren’t tech-savvy enough to notice this. Back to the point, after GandCrab 5.1.0 encrypts a target’s personal data, it labels all the hostage files by appending a random-looking extension to them. This extension is unique for every user, being a string of up to 10 characters. So, let’s say a file named Important.docx has been taken hostage – it will be modified into an off-limits item named something like this: Important.docx.ibptmqlbgf.
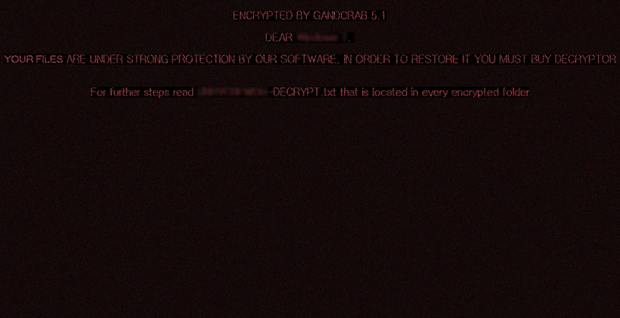
The above distortion of the filenames isn’t the final stage of the attack, though. The GandCrab 5.1.0 ransomware leaves a note so that the infected user gets an idea of what exactly has happened and what to do for recovering the inaccessible files. The name of this entity is going to vary for different users, because its first part matches the victim-specific file extension, the only discrepancy being that the characters are uppercase. In the hypothetical attack above, the ransom note will be IBPTMQLBGF-DECRYPT.txt. Its introductory part goes:
GandCrab v5.1
Under no circumstances do not delete this file, until all your data is recovered.
Failing to do so, will result in your system corruption, if there are decryption errors.
Attention!
All your files, documents, photos, databases and other important files are encrypted and have the extension: [victim-specific extension].
The only method of recovering files is to purchase an unique private key. Only we can give you this key and only we can recover your files.
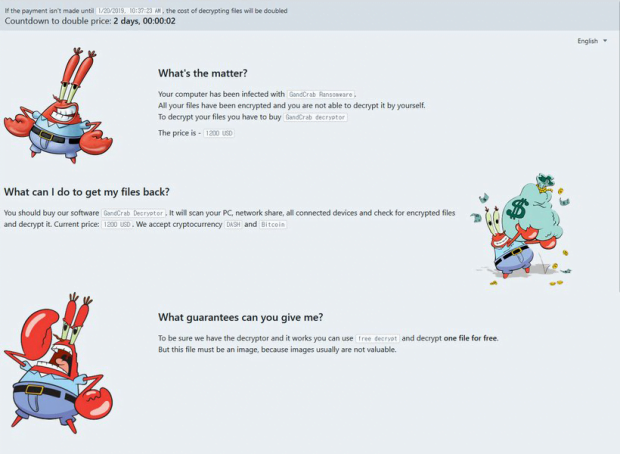
This brings us to the ransom options imposed by the villains. The user is instructed to visit a Tor page (.onion domain) that provides the size of the ransom along with the deadline to pay it. It also includes a chat section to reach out to the attackers. The amount demanded by GandCrab 5.1.0 distributors is 1,200 USD. It is payable in Bitcoin or alternatively in Dash, a less mainstream form of cryptocurrency. The wallet address for either type is indicated on the payment page, too. There is additionally a countdown script running that displays the time left before the price doubles. It is set to 2 days. The only update made to that page as part of the new release is the funny pictures of a crab that definitely don’t align with the unsettling situation.
Obviously, the incursion is a serious predicament. Researchers have yet to figure out a 100% effective way of decrypting files skewed by GandCrab 5.1.0. In the meanwhile, those hit by this plague are facing a dilemma: to pay the ransom and hope the cybercriminals will do what they claim, or try something else. It’s the latter that the sections below highlight in detail. Importantly, keep in mind that this ransomware is spreading through spam – one of the major campaigns involve “love letter” themed emails. So, be sure to refrain from opening such messages from a stranger the next time they end up in your inbox.
GandCrab 5.1.0 ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download GandCrab 5.1.0 ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by GandCrab 5.1.0 ransomware
Workaround 1: Use file recovery software
It’s important to know that the GandCrab 5.1.0 ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether GandCrab 5.1.0 ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓