Cryptom27@yandex.com virus: HDDCryptor ransomware decryption and removal

What can possibly be a more harmful computer threat than file-encrypting ransomware? The only infection that beats this malware category in terms of the damage is the perpetrating code that affects Master Boot Record of a targeted machine. HDDCryptor, aka Mamba ransomware, completely denies access to a compromised operating system, encodes important files and instructs victims to reach the adversary at cryptom27@yandex.com.
Table of Contents
What is the cryptom27@yandex.com ransomware?
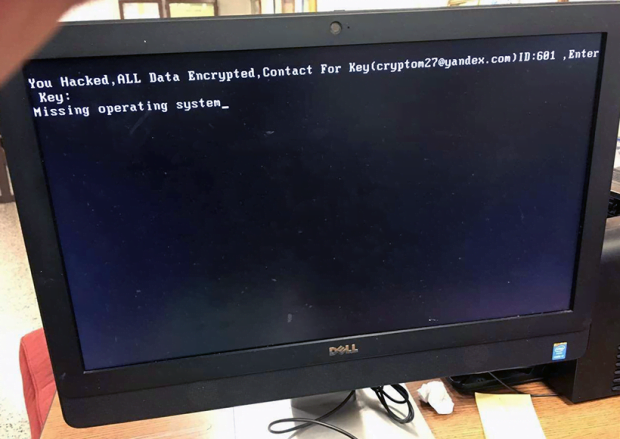
As opposed to the overwhelming majority of ransomware strains at large, the one in question renders plagued computers inoperable. That is, not only does it scramble files stored in popular data formats, but it also rewrites a workstation’s MBR (Master Boot Record). A number of samples with similar functionality have popped up during this year, including Petya and Satana bootkit, but the first specimens of the cryptom27@yandex.com ransomware had surfaced earlier, so it’s sort of a pioneer in utilizing such complex PC locking mechanisms. The ransom warning displayed on the boot screen of a contaminated computer says,
You Hacked, ALL Data Encrypted. Contact For Key (cryptom27@yandex.com) ID: [3_digits], Enter Key:
Missing operating system_
Each one of the previous versions of HDDCryptor featured a different wording and used a different email address to reach the threat actors. Obviously, the ransomware is evolving.
A particularly scary phrase on the lock screen is “Missing operating system”. This isn’t quite true. In fact, the infection emulates this effect by overwriting boot sectors so that a malware-stricken machine is forced to perceive this as the absence of the OS as such. The damage is reversible, though, but it’s a matter of submitting the requested amount of cryptocurrency to the crooks, who claim to provide the decryption key in return. The ransom is 0.5 BTC on average for every affected machine. The problem is, this ransomware mainly targets enterprise networks, so the amount may reach tens or even hundreds of Bitcoins for complete recovery.
The cryptom27@yandex.com virus ends up on computers as a result of drive-by downloads from malicious or hacked websites. In some cases, it has infiltrated systems over spam, where a booby-trapped attachment triggers the infection chain when opened by an unsuspecting recipient. This ransomware has extensive proliferation capabilities, so it propagates to other computers on a corporate network within minutes. Once deployed on all workstations, it drops and executes offending processes called dccon.exe and mount.exe. The former scrambles data residing on the hard disk, and the latter encrypts files on mapped network shares. The cryptographic algorithm used for this routine is RSA-2048, which is asymmetric hence extremely strong. Then, the virus overwrites all Master Boot Records for HDD partitions with a custom boot loader and forces the computer to restart.
The victims are, apparently, forced to shoot an email to cryptom27@yandex.com from a healthy PC for recovery instructions. The criminals will respond with the Bitcoin wallet address and the amount of digital cash to send for decryption.
The following news demonstrates how viable the extortion model behind HDDCryptor is: the threat actors were able to compromise thousands of computers on the San Francisco Municipal Transit Agency’s network on November 25, 2016. This attack has caused a temporary collapse of the computerized faring service, also hitting Muni’s email and SQL database servers, payroll system and other critical digital infrastructure components. The hackers demand 100 Bitcoin, or about $73,000, for unlocking the hostage machines.
Unfortunately, it’s impossible to get around the blocking by HDDCryptor, or Mamba ransomware, at this point. If a victim somehow manages to boot into Windows, though, it may be feasible to decrypt individual files using the methods below.
Cryptom27@yandex.com ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Cryptom27@yandex.com ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by Cryptom27@yandex.com ransomware
Workaround 1: Use file recovery software
It’s important to know that the Cryptom27@yandex.com ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether Cryptom27@yandex.com ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓