Cry36 decryptor: how to remove Nemezis ransomware
When a ransom Trojan gains a foothold on one’s computer, things get out of hand as the infection intelligently spots the most valuable files and scrambles them using cryptography. This classic assault workflow fully applies to the Cry36 virus representing one of the most widespread ransomware lineages circulating in 2017. Peruse this article to get the lowdown on this sample.
Table of Contents
What is the Cry36 ransomware?
The file-encrypting malware strain to be dissected in this entry is known under several different aliases. Aside from the name of Cry36, it may be referred to as CryptON, Nemesis, or X3M ransomware. Why 36? It’s simple: an arbitrary file encrypted by this threat becomes 36 bytes larger than the original. This feature, though, is imperceptible to the average user who will instead identify it by other properties. When tweaking a data item, the Cry36 virus uses a peculiar filename modification format. It appends the original name of a targeted entry with a long extension consisting of a unique victim ID, email address or URL, and a 5-character tail.
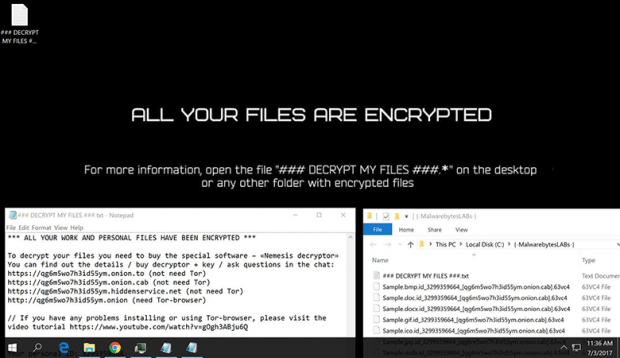
So for instance, a sample spreadsheet Dataset.xlsx will assume the form similar to the following: Dataset.xlsx.id-9238753229_[qg6m5wo7h3id55ym.onion.cab].63vc4. This file pattern itself provides clues on what to do to sort things out, namely visit the web page in square brackets, log in using the ID value, and then follow further directions on the site named the Nemesis ransomware. The 10-digit identifier is isolated to a specific victim, therefore it varies from incident to incident. So does the URL part of the extension, which is quite often replaced with an email address of the attacker. Some of the widely reported contact emails include mk.stryker@aol.com, mk.baraka@aol.com, liukang@mortalkombat.su, mk.rain@aol.com, mk.kabal@aol.com, m.reptile@aol.com, yotabyte@protonmail.com, don-corleone@mortalkombat.su, pay@cyberdude.com, and x3m@usa.com. These accounts probably belong to different “affiliates” distributing the offending code on a Ransomware-as-a-Service (RaaS) basis.
The Cry36 ransomware variant of Nemesis is usually deposited onto Windows computers via hacked RDP connection or malicious spam. If the trespass is successful, it instantly starts scanning local disk partitions, removable drives and network shares for potentially important personal files. The infection skips system directories during this reconnaissance so that the machine runs smooth throughout the extortion routine. Then, having encrypted all matching files inside the right folders, Cry36 renames them in conformance to the above principle.
Additionally, it drops ransom how-to documents named ### DECRYPT MY FILES ###.txt. Its contents go, “All your work and personal files have been encrypted. To decrypt your files you need to buy the special software – “Nemesis decryptor”. You can find out the details / buy decryptor + key / ask questions in the chat.” This part is followed by a number of links leading to the Nemesis decryptor page, where negotiations on the ransom size and decryption options are to be performed. It’s highly recommended to avoid making any deals with the threat actors. Some workarounds do exist, so give them a shot. Get further particulars on ransomware removal and alternative data recovery methods.
Cry36 / Nemesis ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Cry36 / Nemesis ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by Cry36 / Nemesis ransomware
Workaround 1: Use file recovery software
It’s important to know that the Cry36 / Nemesis ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether Cry36 / Nemesis ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓