How to decrypt .CRAB files – Gandcrab v2.1 ransomware
Pretty much any computer user runs the risk of falling victim to crypto ransomware like GandCrab these days. Even with no potentially harmful action on one’s end, such as opening a virus-tainted email attachment, the malicious code can still be deposited on a machine via more sophisticated techniques like the use of exploit kits. The cybercriminal group behind the above-mentioned infection appears to be highly proficient in what they do.
Table of Contents
What is the .CRAB ransomware?
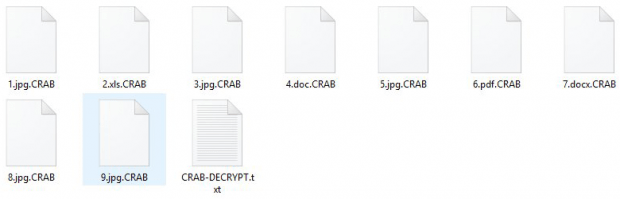
As stated above, the actual denomination of the blackmail malware under scrutiny is GandCrab, which is currently at version 2.1. However, most victims mention the .CRAB file extension when referring to their predicament. That’s, obviously, because people tend to notice the tip of the iceberg from the get-to. This file suffix is one of the early symptoms of the onslaught. Having completed unauthorized data encryption on a target host, the offending code concatenates .CRAB to every single item that underwent the scrambling. So, a sample graphics file named 1.jpg will turn into 1.jpg.CRAB while having also become inaccessible due to the adverse effect of a military-grade cipher.
The ransomware build in question splashed onto the scene in early March 2018, shortly after the Romanian police seized servers used to operate the first version of the malady. This law enforcement move must have called forth little harm to the crooks as they promptly released the fully functional and refined GandCrab v2.1. The updated culprit switched to using the new .CRAB extension and a ransom note named CRAB-DECRYPT.txt. Its Command and Control infrastructure underwent some changes as well, featuring three new .bit hostnames that have to be resolved for the encryption to take place successfully. The TXT ransom how-to got an additional section regarding an option to contact the malicious agents by means of the Tox peer-to-peer instant messaging service.
The .CRAB ransomware is mostly spam-borne when it comes to the propagation. Its payload usually lurks in an archive file attached to fraudulent emails with enticing subjects. These rogue messages can be disguised as an invoice, copyright law-related claim, job offer or some other catchy entity. The infection chain is a matter of the user opening the enclosed Office file and enabling macros in it, which allows for stealth JavaScript code execution on the computer. Then, GandCrab v2.1 silently traverses the host’s hard disk, network drives and removable media in search of valuable information. When this workflow returns a format match event, the pest instantly enciphers the spotted file using the RSA public-key cryptosystem.
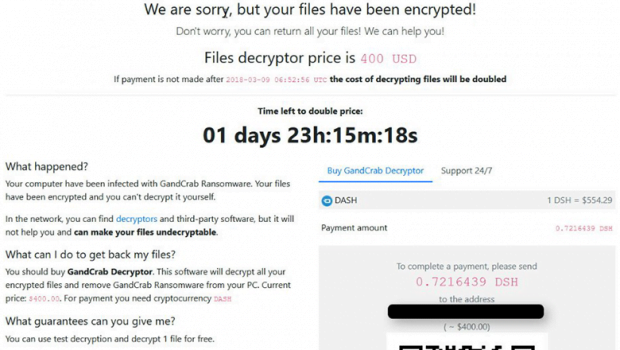
The CRAB-DECRYPT.txt rescue note, which can be found in every folder with hostage files, instructs the victim to visit the GandCrab Payment Page via Tor Browser. The extortionists have even addressed the issue of Tor being off limits in some locations, encouraging people living there to leverage the Tox tool mentioned above. One way or another, the data decryption process endorsed by the criminals boils down to submitting a ransom amounting to $400 worth of Dash. Incidentally, this is the first time said cryptocurrency has been used by ransomware peddlers, so the GandCrab crew is quite innovative indeed. Unfortunately, data decryption in this scenario is pretty much a no-go unless the user gets their RSA private key. It’s the threat actors who keep it, though. The applicable options are restricted to paying the ransom, which isn’t recommended, or trying some classic forensic data recovery tips and tricks.
.CRAB extension automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download .CRAB ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the extension and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by .CRAB extension
Workaround 1: Use file recovery software
It’s important to know that the .CRAB extension creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the extension under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether .CRAB extension has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the extension itself does not belong inside your computer. Incidentally, it often comes with other extension, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this extension and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓