Remove Bad Rabbit ransomware and recover encrypted files
A group of cybercriminals deployed the much-spoken-of NotPetya ransomware campaign in June this year, and now in October crooks, presumably a different crew, followed suit by launching the Bad Rabbit ransomware. The two appear to be very similar on the outside: both encrypt victims’ files and lock down their computers. However, when it comes to code sharing, things aren’t so prosaic because there is a great deal of difference.
Table of Contents
What is the Bad Rabbit ransomware?
Bad Rabbit ransomware, also referred to as BadRabbit, is a perpetrating program abusing cryptography and causing much more damage than mainstream infections from this category. Just like its prototypes Petya and the infamous NotPetya, not only does this new strain encrypt plagued users’ personal files but it also locks them out of their machines altogether. The culprit achieves the latter effect by substituting the MBR (Master Boot Record) with a custom one. In the upshot of this interference, victims end up unable to log into Windows and see a ransom note screen instead. At this point, the victims mostly include governmental institutions and businesses in Ukraine, Bulgaria, Russia and Turkey, with only 1% of the victims being in the United States.
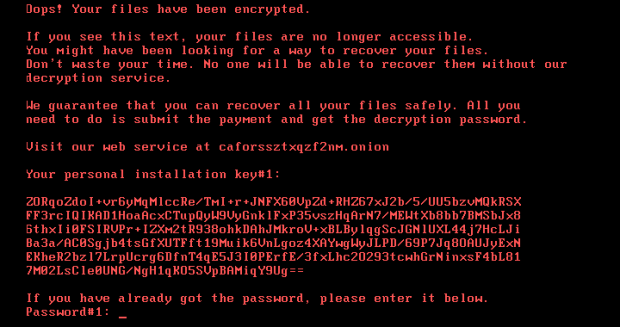
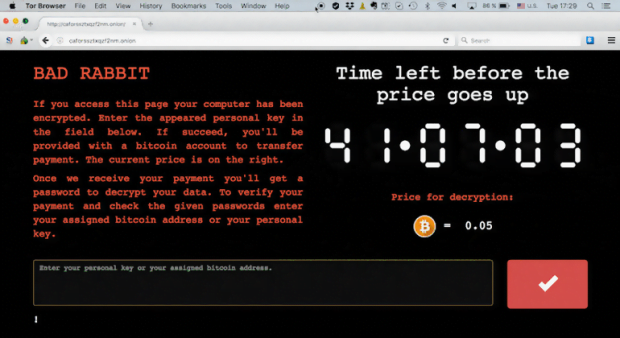
The warning screen presented to contaminated users says, “Oops! Your files have been encrypted. If you see this text, your files are no longer accessible. You might have been looking for a way to recover your files. Don’t waste your time. No one will be able to recover them without our decryption service.” Well, the bad news for those affected is that this information is true to life. All valuable data on the machine gets skewed through the use of AES cryptographic algorithm plus asymmetric RSA cipher. Victims are pressured into visiting the threat actors’ web service via Tor Browser. The page instructs them to submit 0.05 Bitcoin (about $270) for decryption, which is a comparably low ransom compared to most of the ‘competing’ blackmail Trojans. The payment needs to fit in a specified timeframe, which is somewhere around 40 hours, otherwise the size will increase.
The BadRabbit ransomware is making victims by dint of classic social engineering spiced with some hacking trickery. First, people visiting recently compromised popular news websites encounter a browser redirect. Next, a deceptive alert on the rogue landing site instructs them to trigger a Flash update immediately. It’s this pseudo update package to blame for the contamination proper. What happens afterward is the malicious code invokes a number of commands to establish persistence on the host, scan the machine for potentially important files and encrypt them. The above-mentioned MBR replacement trick takes effect after a forcible reboot caused by the pest.
As opposed to a commonplace ransomware scenario, troubleshooting in the Bad Rabbit case isn’t restricted to bad code removal and data recovery. It additionally presupposes regaining access to the system by fixing the corrupted Master Boot Record. A possible workaround is to use a bootable rescue media, such as a CD or USB. Doing so may help a victim get the system to load in the first place. If this endeavor turns out successful, proceed to steps below.
Bad Rabbit ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Bad Rabbit ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by Bad Rabbit ransomware
Workaround 1: Use file recovery software
It’s important to know that the Bad Rabbit ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether Bad Rabbit ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓