Do we Live in a “Post Antivirus” World?

Ten years ago, many people’s strategy for keeping their computers secure began and ended with installing some antivirus software and ensuring it was kept up to date.
As anyone with even a passing interest in cybersecurity now knows, the days where that was wise are long gone.
Antivirus software is still extremely important, and not something anyone would be wise to skimp on. However, it’s clear that a basic antivirus system – one that works by essentially maintaining a database of “definitions” that identify viruses – is not something anyone can employ as a “one size fits all” solution for online security.
Over the years, it’s become clear that antivirus vendors are very much aware of this fact. A quick glance at the features list of any mainstream antivirus or “Internet Security” product tends to reveal a raft of features that have little to do with viruses in the traditional sense.
Online identity protection is often highlighted as one of the key features of these products; Other things often seen include ransomware protection, banking security, and features to help people lock down their social media presence. Traditional definition-based antivirus protection is alive and well – but using it is increasingly becoming just one small part of what people need to do to stay safe online.
Table of Contents
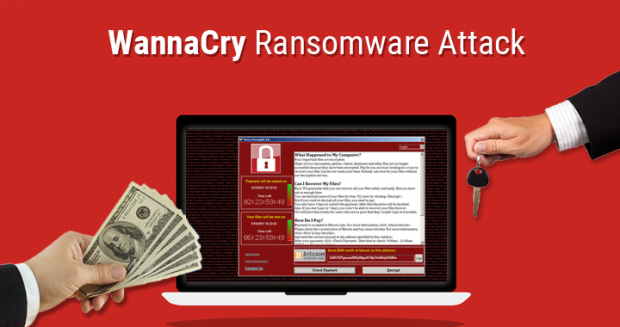
The Big Ransomware Attack
Internet security hit the headlines in May 2017 after a “global cyberattack” hit organisations across the world, including the National Health Service in the UK.
The relevance of this, in this context, is that it’s reasonable to assume that all of the big companies affected (which included the likes of Fedex, Deutsche Bahn and Telefonica) had antivirus software in place on their systems. But when it came to it, it did little to prevent them becoming infected with the WannaCry ransomware that locked down their desktops and demanded money to release file data.
One of the main things that affected the UK NHS specifically was the fact that a key operating system patch for Microsoft Windows hadn’t been widely deployed. Once the ransomware was able to find its way onto a single machine, it was quickly able to spread to others across the network via SMB network shares. There’s no evidence to suggest that some old-school antivirus software jumped in to stop the spread of the infection.
When it comes to unleashing malware like WannaCry onto a machine, it’s often done in a way the circumvents the antivirus anyway. Social engineering techniques mean that it’s often the case that a non-technical user gets fooled into downloading and installing the malware in the first place. For example, it can pose as an update to some regularly used software, or a browser plugin.
It’s for this reason that technical people (and IT staff) need to contemplate what I’m describing here as a “post antivirus” world. While we’re clearly not completely “post antivirus” because there’s still good reason to use it, we are becoming “post antivirus” in terms of the increasingly small part people can reasonably expect such software to play in keep their computers safe.
An Anecdote
When I’m not writing articles like this one, I work as a freelance IT consultant. I was recently attending an IT strategy meeting with a client, laying out the plans for their infrastructure for the years ahead.
When we moved on to IT security, it became clear the customer was seeking some form of “rubber stamp” guarantee that choosing the right antivirus product meant almost total IT security.
The news that it’s not possible to guarantee such a thing came as quite a surprise. The client was equally surprised when I said that despite spam filters and other measures, I still, on occasion, see phishing emails and other nasties in my own Office 365 email accounts. As such, I emphasised that he and his team should be prepared for the fact that they will have some potential malware slip through the net at some point.
The client was genuinely surprised that I couldn’t wave a wand and put in a software solution that made the network “malware proof” – regardless of how much budget he was willing to throw at the problem.
When he reached the point of saying, “so what IS the answer then?” all of the technical people in the room replied (in unrehearsed unison) with a single word: “education”.
The fact is that online safety nowadays is as much, if not more, about things like being wary of insecure websites, suspicious of emails and phone calls, and avoiding using easy but risky free Wi-Fi without the protection of a reliable VPN service.
It seems that despite the headlines and the constant news reports relating to IT security breaches, non-technical people are still yet to grasp the fact that antivirus isn’t going to save them from every online threat – or, indeed, for themselves, if, for example, they are fooled into installing something they shouldn’t.
Obviously, the technical people out there have quite a task on their hands explaining this, because the antivirus vendors, inevitably, continue to market their products as something that seems to mitigate every possible IT security threat.
We all still need antivirus – so we’re not in a “post antivirus world” in the literal sense. But everyone needs to realise that the next big malware attack will probably start from when someone is tricked into doing something online. It’s really unlikely that it will be because the IT team chose the “wrong” antivirus software.
Posted in: News
Leave a Comment (0) ↓