Remove Yoyodiy ransomware and recover encrypted files
Users hit by the average ransomware threat are in a serious quandary due to the deep-level impact incurred as a result of these attacks. Cybercriminals have become quite professional at utilizing cryptography for malicious purposes, as is the case with the new ransom Trojan called Yoyodiy. It bypasses antimalware defenses when infiltrating a computer, encrypts the prey’s important files and extorts Bitcoins for the private decryption key.
Table of Contents
What is the Yoyodiy ransomware?
Yoyodiy is quite an odd name for a crypto infection. This weirdness, though, doesn’t make this culprit’s adverse effect any less devastating. There is scarce information on the origin of the strain under scrutiny at the time of this writing. It appears to have been developed independently and most likely does not represent any known ransomware family, which isn’t a frequent encounter in the present-day cybercriminal underground. What is known for a fact is that Yoyodiy is potentially more harmful than other blackmail viruses as it goes equipped with a backdoor component and add-ons for harvesting victims’ PII (personally identifiable information). This toxic combo makes the sample really stealthy and extremely dangerous.
The Yoyodiy ransomware reportedly doesn’t deviate much from the majority of file-encrypting pests in terms of the propagation vectors. Its authors stick with a spam-based mechanism of payload delivery. The intended victims receive phishing emails disguised as high-priority invoices, billing information, missed delivery notifications, job offers, scanned fax messages or traffic infringement notices. The contagious element arriving with these rogue emails is an attached ZIP archive or Word document, which will execute the ransomware binary once opened. Owing to the above-mentioned backdoor properties of this perpetrating program, it can sneak inside without any peculiar telltale signals, thwarting detection by most security suites across the board.
As soon as the Yoyodiy virus finds itself on a computer, things get out of hand as it obtains privileges high enough to disable the volume shadow copy service so that the user cannot leverage earlier automatic snapshots of their files to restore them later on. That’s just a preliminary routine followed by a scan of the hard drive and network shares for potentially valuable data. The ransomware specifically zeroes in on Microsoft Office documents, personal photos, videos and databases while ignoring system executables and other objects required for stable operation of Windows. All the spotted files are subject to cryptographic skewing through the use of AES and RSA ciphers.
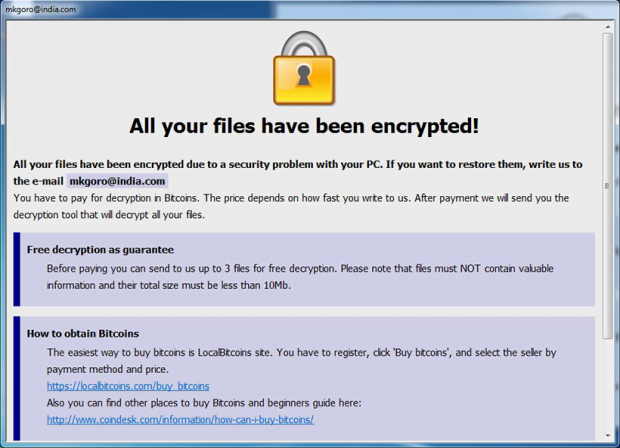
To add final strokes to the incursion, Yoyodiy drops ransom notes named ReadMe.txt or similar. These are manuals that instruct the victim to contact the attackers and send a certain amount of cryptocurrency to their Bitcoin wallet. The size of the ransom is typically in the range of 0.5-1 BTC. In return, the ne’er-do-wells promise to provide the secret key and automatic decryptor, but these might well turn out to be empty promises. So instead of trying to redeem data through ransom, give the instructions below a shot to get rid of the Yoyodiy virus and reinstate hostage files.
Yoyodiy ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Yoyodiy ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by Yoyodiy ransomware
Workaround 1: Use file recovery software
It’s important to know that the Yoyodiy ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether Yoyodiy ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓