“Your files are encrypted”: Microsoft Decryptor ransomware virus
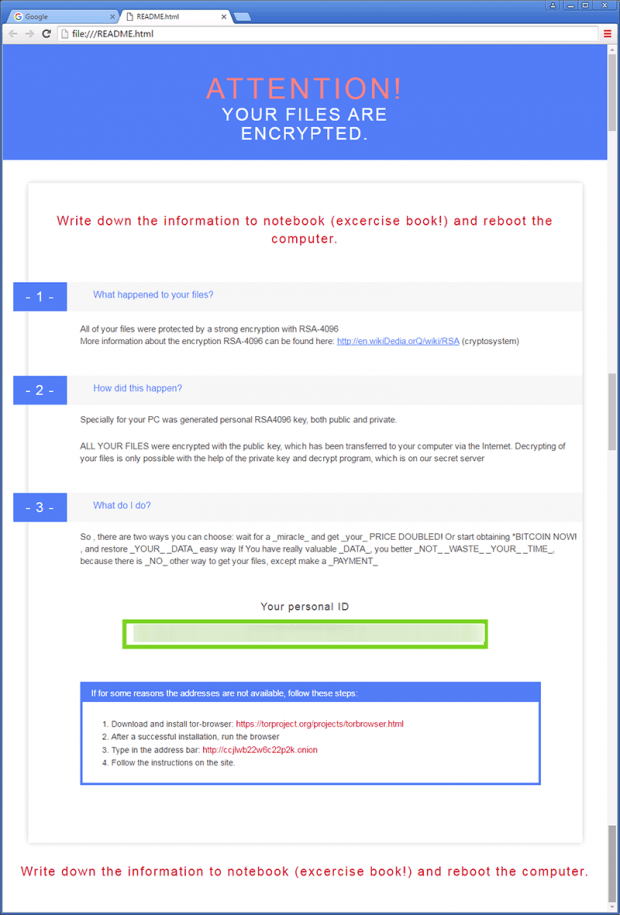
The updated edition of CryptXXX ransomware, also referred to as Microsoft Decryptor, has introduced a couple of new features. While the predecessor appended a random string at the end of filenames, such as .AF4D3, this one does not affect the look and feel of encrypted data at all. Furthermore, the Trojan now creates ransom notes titled simply Readme.html, Readme.bmp and Readme.txt, as opposed to using a victim’s personal ID as the main component of the name.
With all these tweaks in place, the common denominator across the totality of CryptXXX attributes is the warning that says “Your files are encrypted”, which appears in HTML, BMP and TXT ransom instructions. This introductory phrase is followed by step-by-step directions regarding data recovery, as well as a recommendation to write them down to a notebook and reboot the machine.
But before this guidance is presented to the victim, a furtive injection of the malicious program takes place. This process involves an exploit kit hosted on a certain domain on the Internet, and it also relies on a number of conditions related to the PC being targeted. In particular, the system is only vulnerable as long as there are unpatched flaws in software, chiefly Adobe Flash Player and Java. The Angler or Neutrino exploit kit instantly detects these weaknesses and executes the ransomware behind the scenes.
CryptXXX targets a variety of files on the infected computer’s hard disk, network repositories and removable media. A search for data that meets the pre-determined extension criteria is what the ransomware does on the early stage of the attack. Once the list is available, the infection applies a complex crypto routine in order to turn these files into jumbled entities that cannot be opened. The cyber rascals tailored this malady so that it leverages the asymmetric RSA algorithm, one of the most unbeatable cryptosystems to date. By the way, the Notepad edition of ransom instructions contains a misprint and mentions something called “RZA” instead.
As soon as the data has been reliably encoded, “Your files are encrypted” ransomware changes the desktop background and adds three versions of file restoration walkthroughs inside each folder with affected items. Again, this combo includes the following objects: Readme.html, Readme.bmp and Readme.txt.
Ultimately, the victims are redirected to an .onion site named the Decryption service, which suggests that they pay 1.2 Bitcoins and then download the rogue tool called Microsoft Decryptor that will supposedly restore everything automatically. There is a 100-hour deadline for payment, after which the ransom doubles and amounts to more than $1,500 (2.4 BTC). Although there are no fully effective recovery instruments at this point, the steps below are worthwhile as they may help regain access to a part of the ransomed data.
Table of Contents
“Your files are encrypted” ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download “Your files are encrypted” ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by “Your files are encrypted” ransomware
Workaround 1: Use file recovery software
It’s important to know that the “Your files are encrypted” ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether “Your files are encrypted” ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓