WinSnare virus – amuleC adware removal

Malvertising is a term that emerged in the wake of computer crooks’ intensifying efforts to earn from ecommerce in malicious ways. There are different manifestations of this activity, ranging from hijacking victims’ browser preferences, to inserting sponsored content into web pages. The common denominator across these attacks is the use of specially crafted software referred to as adware. WinSnare is an example of this type of bad code which, once inside a computer, turns the user’s online surfing routine upside down.
Table of Contents
What is WinSnare?
For the sake of clarity, it should be stated upfront that WinSnare is not a high-profile computer infection. It won’t cram an infected system up with junk files to slow it down to a crawl, nor will it encrypt data and hold it for ransom. Instead, the application under scrutiny invades the Internet surfing environment only, sprinkling a slew of advertisements on virtually every website the victim visits. Although the impact seems moderate at first sight, it causes a great deal of frustration for the plagued user. A variety of ads by WinSnare will be displayed on top of the original website components, forcing the victim to close them to be able to actually read the content or view the media on the page. An important thing to understand is that these annoying sponsored objects only show up on PCs with the WinSnare applet running on them.
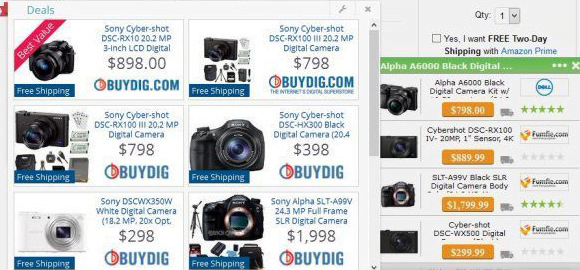
WinSnare adware may include boxes titled “Deals”, which pop up and float above web page elements. The products displayed in these advertisements match the victim’s interests, which proves that the adware monitors sites visited and search queries made by the user. One more type of unwanted items generated by WinSnare is comparison shopping, where prices for certain goods on different ecommerce resources are listed. The infection also turns random keywords into clickable text. These in-text links are especially obnoxious because they can be clicked accidentally. Yet another side effect has to do with interstitial ads, both full-page and smaller ones, being fired randomly and staying opened in the background until manually closed.
The makers of WinSnare didn’t reinvent the wheel as far as the distribution of their adware goes. This potentially unwanted application goes bundled with free programs like amuleC, uvconverter, interhop etc. This is a wily scheme because people don’t always look further than the main software they are about to install, in particular if it’s free. The thing is, some download sites monetize freeware distribution activity by incorporating perpetrating entities into what’s called installation clients. It’s remarkably easy to avoid contamination in these cases – all it takes is opting out of redundant third-party utilities by selecting the custom setup option. However, most people are fine with the default preset, and criminals know it. To fix the WinSnare.dll problem, it’s mandatory to get rid of the malicious browser extension and revert browsing settings to their normal state.
WinSnare adware automatic removal
The extermination of WinSnare adware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped out from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
2. The scan will come up with a list of detected items. Click Fix Threats to get the adware removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the infection. However, it might be a good idea to consider ascertaining the adware is gone for good.
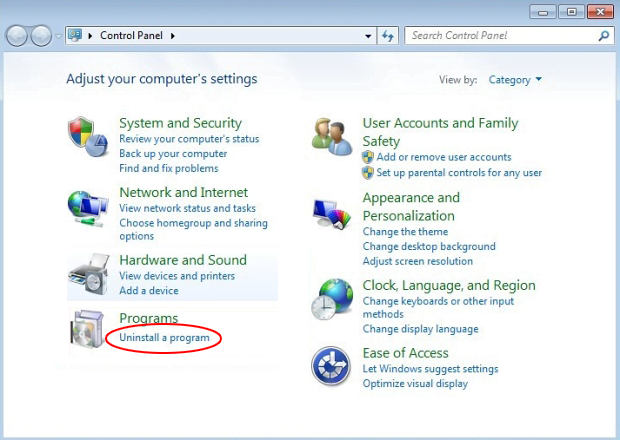
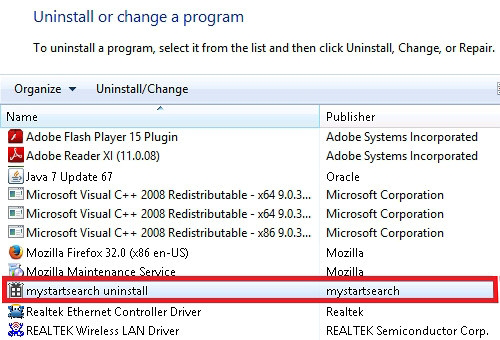
Remove WinSnare adware using Control Panel
- Open Control Panel. On Windows XP / Windows 8, go to Add or Remove Programs. If your OS is Windows Vista / Windows 7 / Windows 10, choose Uninstall a program

- Look down the list and locate an app that appears fishy. Click the Uninstall/Change (Change/Remove) option to get the intruder removed if spotted

WinSnare adware removal by resetting the affected browser
Please take into consideration that as effective as it is, the procedure of restoring browser defaults will lead to the loss of personalized settings such as saved passwords, bookmarks, browsing history, cookies, etc. In case you are not certain this outcome is suitable despite its obvious efficiency, it’s advised to follow the automatic removal method described in one of the previous sections of this tutorial.
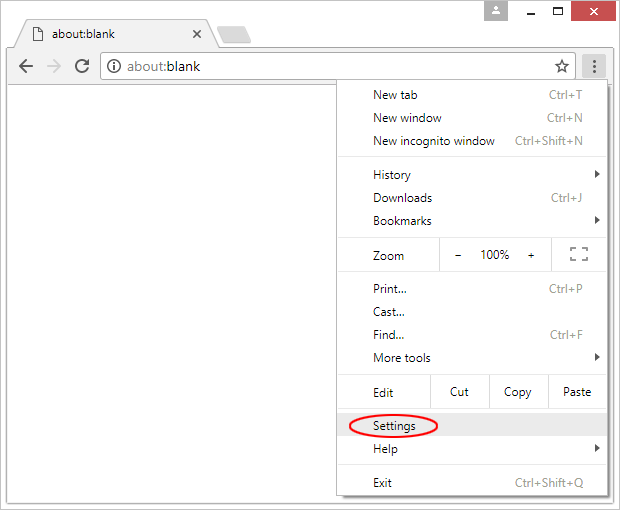
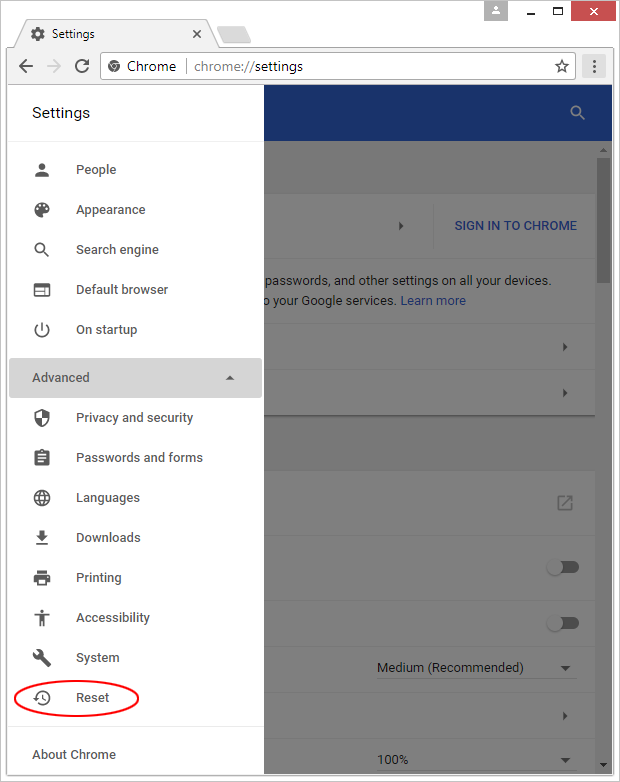
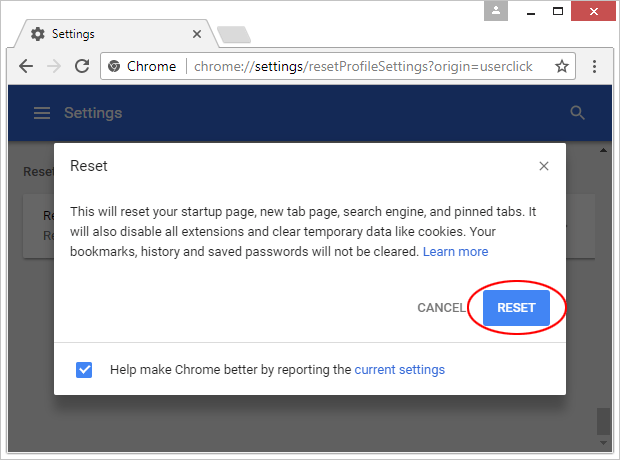
Reset Google Chrome
- Click on the Chrome menu icon and select Settings

- Locate the Advanced option under Settings and click on it to expand the menu. Then, pick the Reset button at the bottom

- When a new screen appears, hit Reset once again

- Chrome will now display a confirmation dialog box listing the types of data that will be lost if you proceed. Read the message carefully and, if you’re sure, click Reset

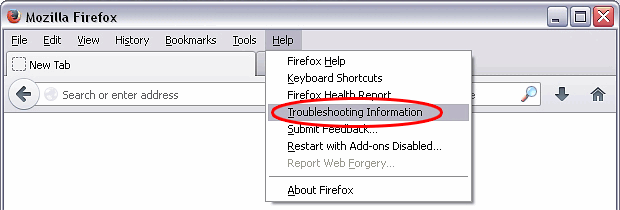
Reset Mozilla Firefox
- Click on Help menu and select Troubleshooting Information from the drop-down list, or type about:support in the URL field

- On the Troubleshooting Information screen, click Refresh Firefox option and confirm the procedure on another dialog

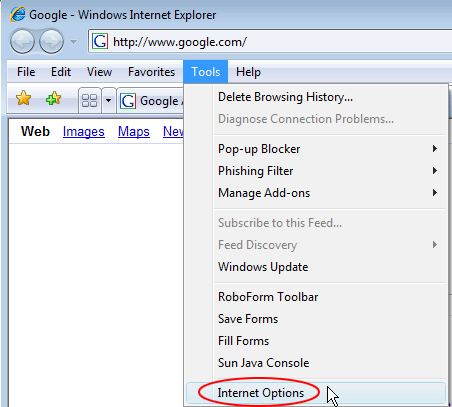
Reset Internet Explorer
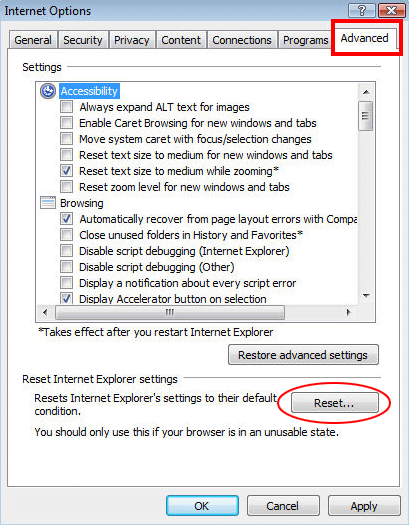
- In IE, go to Tools and select Internet Options from the list

- Hit the Advanced tab and click on the Reset option

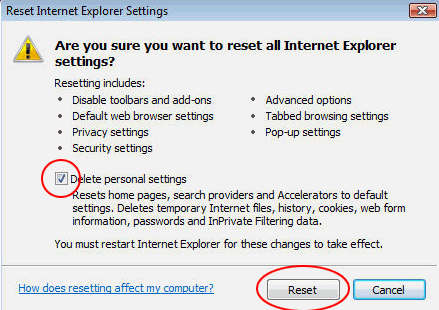
- IE will now display Reset Internet Explorer Settings box, where you should put a checkmark next to Delete personal settings option and click Reset at the bottom

Verify whether WinSnare adware has been completely removed
For certainty’s sake, it’s advised to repeatedly run a scan with the automatic security software in order to make sure no harmful remnants of this adware are left inside Windows Registry and other operating system locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓