Remove Windows Accelerator Pro fake antivirus
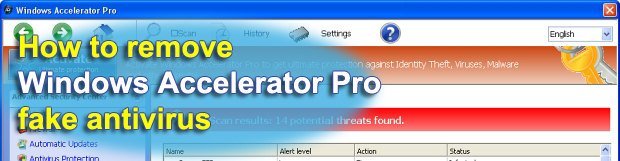
Detailed description of Windows Accelerator Pro rogue security software, symptoms of this infection and automatic as well as manual removal advice – all of this is included in this tutorial.
Scamming users is the primary goal of programs like Windows Accelerator Pro. This one is classified as a rogue antivirus, which means it is designed to install onto computers in a covert manner, make it look like your PC is contaminated with dialers, Trojans, backdoors, password stealers, and other nasty objects; and then recommend upgrading to commercial version to get the supposedly bad stuff removed. Nice try, but you won’t get tricked that easily, will you?
If you take a look at the above screenshot of this scareware, it becomes clear why rogue products of this sort are still afloat throughout the years that they’ve been around: this sample looks fairly trustworthy and resembles legitimate software. However, this application is not powered by an antivirus database at all therefore it cannot possibly detect anything. Despite this, the pest launches boot-time scans and reports tons of threats. Alongside the fake scanners, this rogue utility triggers misleading popup alerts stating that your system and data are at risk.
Here are some examples of what these spoof warning messages say:
Error
Trojan activity detected. System integrity at risk.
Full system scan is highly recommended
Error
System data security is at risk!
To prevent potential PC errors, run a full system scan
The activity of Windows Accelerator Pro is not restricted to only adopting a deceptive tactic. It also tends to prevent other software from accessing the Internet or being executed, thus making it unbearable to keep using the machine. Below is an illustration of the message that gets generated in this case:
Firewall has blocked a program from accessing the Internet
C:\Program Files\Internet Explorer\iexplore.exe
is suspected to have infected your PC.
This type of virus intercepts entered data and transmits them
to a remote server
Based on the outlined profile of this digital threat, it’s obvious that letting it stay on your PC is a bad idea; nor is it reasonable to register its licensed copy. The correct way to act if you got infected with this particular malware is highlighted in the removal section of this guide – be sure to review it and stick to the step-by-step recommendations provided.
Table of Contents
Windows Accelerator Pro fake automatic removal
The extermination of Windows Accelerator Pro fake can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped out from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Windows Accelerator Pro remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the fake removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the infection. However, it might be a good idea to consider ascertaining the fake is gone for good.
Windows Accelerator Pro – manual removal
While giving in to the automatic cleanup in terms of efficiency, you might want to give this method a shot. It implies that you locate all components of Windows Accelerator Pro inside your system and remove them manually. Here is what you should do:
1. Unhide protected operating system files
Go to Start menu, access Control Panel, and then select Appearance and Personalization
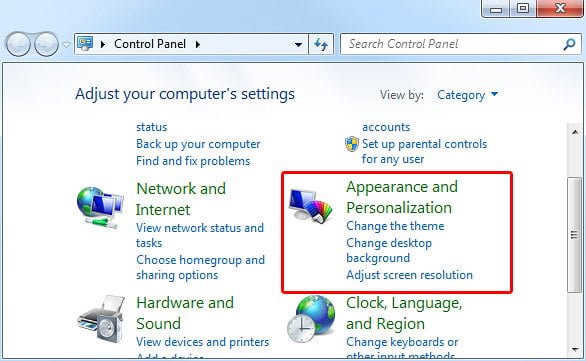 Choose Folder Options and hit the tab called View. Under Advanced settings, make sure Show hidden files, folders, and drives option is activated, and there is no checkmark next to Hide protected operating system files.
Choose Folder Options and hit the tab called View. Under Advanced settings, make sure Show hidden files, folders, and drives option is activated, and there is no checkmark next to Hide protected operating system files.

2. Remove files associated with Windows Accelerator Pro
Locate and delete the following files and folders:
%AppData%\result1.db
3. Delete registry information added by Windows Accelerator Pro
Type regedit in your Search programs and files field and press Enter.
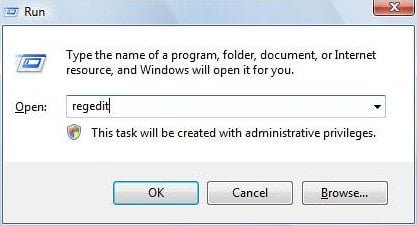 In the Registry Editor interface, click on look for the following entries under HKEY_LOCAL_MACHINE and HKEY_CURRENT_USER directories:
In the Registry Editor interface, click on look for the following entries under HKEY_LOCAL_MACHINE and HKEY_CURRENT_USER directories:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MpUXSrv.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MSASCui.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\msconfig.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\msmpeng.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\msseces.exe
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Associations “LowRiskFileTypes” = “.zip;.rar;.nfo;.txt;.exe;.bat;.com;.cmd;.reg;.msi;.htm;.html;.gif;.bmp;.jpg;.avi;.mpg;.mpeg;.mov;.mp3;.m3u;.wav;”
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Attachments “SaveZoneInformation” = “1”
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Settings
HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Winlogon “Shell” = “%AppData%\guard-.exe”
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system “ConsentPromptBehaviorAdmin” = “0”
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system “ConsentPromptBehaviorUser” = “0”
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system “EnableLUA” = “0”
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system “EnableVirtualization” = “0”
If found, right-click on each one of these and select Delete option.
Verify whether Windows Accelerator Pro fake has been completely removed
For certainty’s sake, it’s advised to repeatedly run a scan with the automatic security software in order to make sure no harmful remnants of this fake are left inside Windows Registry and other operating system locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓
