WildFire Locker ransomware virus removal: decrypt .wflx extension files
Judging from the name of WildFire Locker crypto ransomware, one might perceive it as a high-profile threat that encrypts victims’ data in the blink of an eye and cannot be defeated. In fact, however, it isn’t unique. It does implement the Advanced Encryption Standard flawlessly, and the user interaction modules are crafted professionally enough. But still, it’s just a commonplace ransomware strain most likely representing the so-called Zyklon family.
Table of Contents
What is WildFire Locker
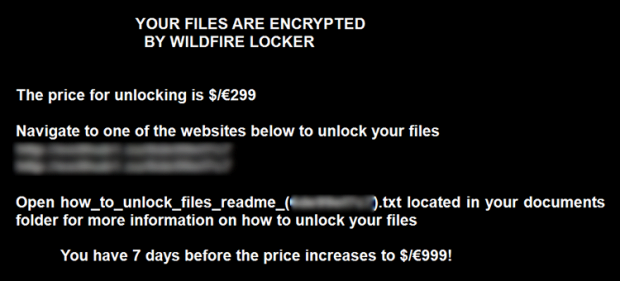
There are several noteworthy attributes that make WildFire Locker a standalone sample of file-encrypting code. First off, it’s the naming format for ransom notes and encoded files. Every compromised user gets a string of 10 hexadecimal characters assigned to him or her. This personal ID becomes the kernel, invariable component of the above-mentioned decryption walkthroughs’ names. For instance, if the ID is 12c5c17b1a, the files with recovery instructions will be titled HOW_TO_UNLOCK_FILES_README_(12c5c17b1a).txt, with .html and .bmp editions spawned across the system as well. The main message in these notes is conveyed via the phrase “All your files have been encrypted by WildFire Locker”.
Furthermore, this offending program assigns a user-specific array of 6 characters, such as 5c25ba, and the .wflx uniform extension to skew the look of filenames. If the name of a random file was ‘Postcard.jpg’ prior to the breach, it will transform into ‘Postcard #WildFire_Locker#5c25ba##.jpg.wflx after the fact. All in all, it’s hard to confuse this crypto virus sample with any other.
The operators of this ransomware are predominantly using social engineering tactics to deposit their infection onto Windows computers. They didn’t reinvent the wheel and chose to leverage spam for this purpose. Users therefore bump into a new message in their inbox, and those who get curious open it and take the bait. These emails may be disguised as a rogue invoice, a UPS delivery notification, or a resume. The messages themselves are harmless, unlike the file attached to them. It’s usually a ZIP archive that executes obfuscated JavaScript code when extracted.
Once the ransomware is up and running on a PC, it detects all local drives, removable drives and network shares. Then, it scans them all for files that are likely to be important to the victim. To this end, the program compares all data elements against a hard-coded list of file extensions, which correspond to popular formats. To encode the objects found during this traversing and matching routine, WildFire Locker employs CBC, which stands for cipher block chaining. This technique ensures that the data is inaccessible unless the user has the master key. This decryption password, unfortunately, is obtained from a secret server and cannot be retrieved with just the infected machine at one’s disposal.
In its ransom directions, WildFire Locker tells its victims to pay 0.5 Bitcoins. The equivalent is non-crypto currencies is about 300 EUR/USD. This amount tends to increase if the infected person fails to submit the initial ransom within a 7-day deadline. The affected user can have 2 files decrypted for free; at least, that’s what the criminals claim. If none of these ransom-related options suits you – which is hopefully the case – try the tips below to restore the .wflx files encrypted by WildFire Locker.
WildFire Locker extension automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download WildFire Locker ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the extension and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by WildFire Locker extension
Workaround 1: Use file recovery software
It’s important to know that the WildFire Locker extension creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the extension under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether WildFire Locker extension has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the extension itself does not belong inside your computer. Incidentally, it often comes with other extension, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this extension and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓