Traffic Infringement Notice scam emails

It doesn’t take a genius to understand why spam is a godsend for online crooks. It can be used to pull off phishing and spear-phishing attacks, serve up malicious software and conduct a variety of Internet hoaxes. In other words, the present-day cybercriminals don’t necessarily have to leverage sophisticated tools like exploit kits to reach their goals – it may suffice to simply deliver emails with rogue links or malicious attachments.
Table of Contents
What is Traffic infringement scam?
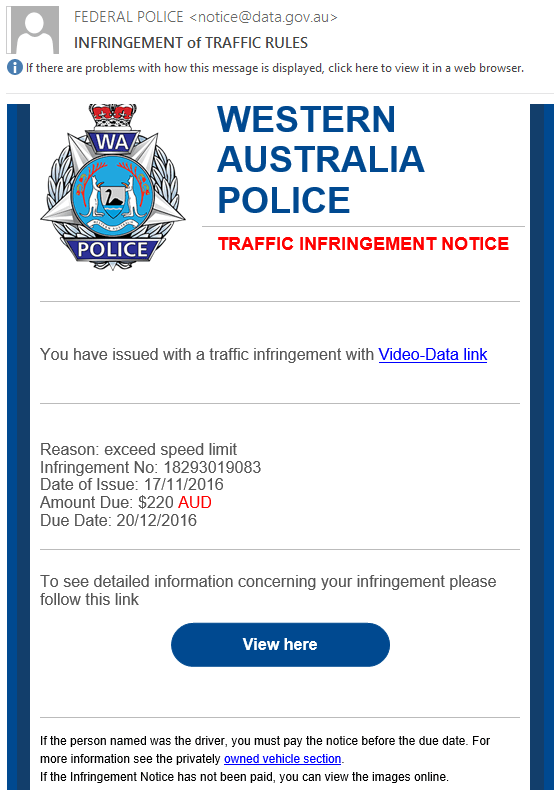
The traffic infringement scam is one of the oldest and most widespread online frauds. Over the past several months, though, security analysts have been observing a drastic spike in the exploitation of this theme to distribute malware and dupe users into handing over their sensitive credentials. The threat actors in charge of these campaigns are busier than ever, sending out bulk emails that impersonate the recipients’ local police. Obviously, there is a fair degree of geo-targeting in these hoaxes, although they are usually not person-specific. These emails are tailored quite professionally so that most users fall for the claims therein. The sender’s name may look legit, for instance it might read “Federal Police” or similar. Furthermore, the email will typically contain a logo of the purported agency for a more persuasive brainwashing effect.
Furthermore, the scam email will usually provide down-to-earth details of the inexistent offence. The reasons may vary, but they mostly revolve around exceeding the speed limit and negligent driving. The fraudsters tend to also add such information as the infringement number, date of issue, amount due, and due date. Aside from the cogency objective, these technicalities are aimed at feigning evoking the sense of urgency. When nervous and in panic, people are prone to making wrong decisions, and the bad guys know it. With the whole ostensible trustworthiness in place, there are quite a few attributes in these emails that should raise red flags. Well, first of all, this is not a commonplace way for the police to notify drivers about offences committed. Secondly, there is absolutely no real-world event that could be grounds for a traffic infringement notice that like.
Another giveaway is the presence of links or attachments in the rogue emails. These entities are the main catch here, because they pose the actual privacy and security risks. The confused recipients are wrongfully instructed to view the details of the phony violation. In some cases, the links are claimed to point to pages with video proof of the offence. By clicking on them, users will end up on sites hosting malicious scripts that trigger the contamination chain behind the scenes. Sometimes, though, the linked-to phishing pages will ask for the person’s banking credentials to proceed with paying the fee. There may also be booby-trapped files attached to the traffic infringement scam emails. In this case, the victim is supposed to download the file, which contains obfuscated JavaScript and executes perpetrating code like ransomware or spyware on the PC.
Given all of these facts, the number one recommendation is to ignore such messages. Of course, it’s unreasonable to click on the embedded links or download attachments, otherwise the computer may get infected with harmful code.
Traffic infringement scam automatic removal
The extermination of Traffic infringement scam can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped out from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Traffic infringement remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the scam removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the infection. However, it might be a good idea to consider ascertaining the scam is gone for good.
Posted in: KnowledgeBase
Leave a Comment (0) ↓