How to decrypt .tfude/.tfudet file ransomware
What makes ransomware stand out from the crowd is its critical, or sometimes irreversible, adverse effects. As opposed to other malware deployers, the cybercriminals who run these campaigns don’t zero in on manipulation or information theft. Instead, they target the most precious digital asset of users and organizations – their data. One of the strains referred to as the STOP ransomware has seen a huge spike recently, with the latest .tfude, .tfudeq, and .tfudet extension variants wreaking lots of havoc.
Table of Contents
What is the Tfude ransomware?
The wicked crew behind the STOP ransomware appears to be back in business after nearly one year of hiatus. These ill-disposed individuals have been demonstrating an unprecedented fuss by coining one version after another since late 2018, with this uncomforting trend moving on in 2019. Following the now notorious .djvu and .pdff file mods, the most recent spinoffs have splashed onto the scene around mid-January, introducing the .tfude, .tfudeq, and .tfudet extensions to the malicious portfolio. This symptom is right on the surface as the infection concatenates one of the above strings to every filename on the contaminated host that underwent the offending cryptographic raid. The resulting distortion of a sample file Forest.bmp is therefore Forest.bmp.tfude, Forest.bmp.tfudeq, or Forest.bmp.tfudet. As seen in the example, the original filenames stay intact.
The most likely entry point for the .tfude (.tfudeq, .tfudet) ransomware is just about as old as malware itself. It comes down to the use of spam. The harmful payload typically arrives with an email that looks enticing enough for the recipient to get curious and open it. It can be disguised as an invoice from some utility services company, a parcel delivery notice, a job offer, a CV or something similar. The attached file, usually a Word or PDF document, is a wolf in sheep’s clothing. It contains obfuscated JavaScript or VB macros that, once fired up, connect to the extortionists’ Command and Control (C2) server and download the .tfude ransomware from it so that the victim remains clueless about this shady activity going on. When executed on the host, the parasite begins traversing the disks, including removable drives and mapped network shares, trying to spot as many potentially valuable files as possible. It goes with a long list of popular extensions to look for, so in the upshot the overwhelming majority of personal data will be located in a matter of minutes. Next, the pest applies a cipher to prevent the victim from accessing those files.
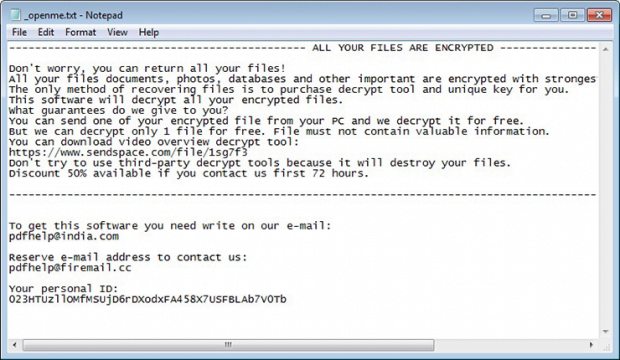
Any ransomware attack is only half-baked unless a ransom note is dropped. The .tfude virus and the clone variants go the full way, leaving a rescue message in a file named _openme.txt. This document ends up everywhere on the plagued computer, from desktop to each folder with encrypted data. It informs the victim that their files have been locked down and the only method to get them back comes down to purchasing the decrypt tool and unique key. One file can be restored for free – at least, that’s what that attackers claim in the recovery document, emphasizing that it shouldn’t contain any valuable information. To get started on the decryption process, the victim is urged to contact the criminals at pdfhelp@india.com or pdfhelp@firemail.cc. The response will include the size of the ransom along with the BTC wallet address to send it. The amount is $980 worth of Bitcoin, with a 50% discount available if the user reaches out to the malefactors within the first 72 hours. Even with the “discount” in place, doing what the crooks want is not recommended. Instead, try the options below and see if this can help address the ransomware issue.
Tfude file automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Tfude ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the file and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by Tfude file
Workaround 1: Use file recovery software
It’s important to know that the Tfude file creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the file under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether Tfude file has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the file itself does not belong inside your computer. Incidentally, it often comes with other file, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this file and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓