Spora ransomware decryption and removal techniques
Whereas the indicators of compromise in the average ransomware attack predicament are usually uniform, different file-encrypting strains still have their unique properties. In the case of the relatively new Spora ransomware, offbeat characteristics are to the fore. It uses a nontrivial cryptographic technique to deny access to one’s data, implements a smart victim gradation tactic, and features an outstanding payment service not every legit ecommerce resources can boast.
Table of Contents
What is Spora ransomware?
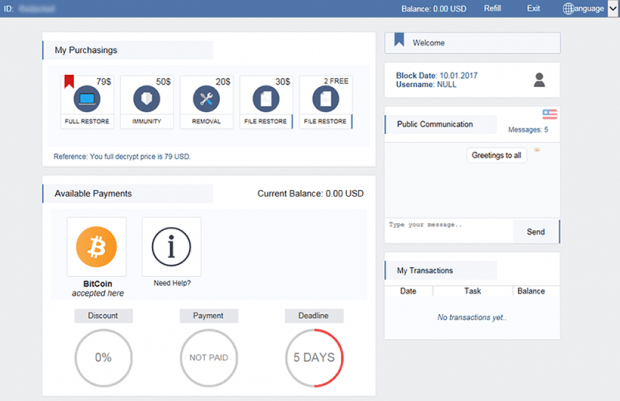
The Spora crypto virus applies an uncrackable cipher to render a victim’s files inaccessible and then requests a ransom in Bitcoin to restore this data. Although this modus operandi is commonplace for this category of malware, Spora went much further in terms of the complexity of its operation. Its encryption engages two different algorithms, asymmetric RSA and symmetric AES. Having deployed a series of data scrambling layers, the infection saves the encrypted keys to a separate .KEY file, which also contains system-specific metadata. This may sound like redundant work, but it certainly makes sense in the context of the subsequent extortion routine. Every victim is supposed to upload their .KEY file to the decryption service later on, and this synchronization results in personalized treatment of the infected user in terms of the ransom size.
Spora ransomware propagates by dint of social engineering. Its operators instigate various spam campaigns whose purpose is to deliver the malicious downloader to as many Windows workstations as possible. The spoof emails contain ZIP attachments that are mostly disguised as invoices. The format of the files inside these archives isn’t what it appears, because the crooks employ a double extension trick so that an HTA file looks like a Microsoft Word or PDF document. Unsuspecting users may therefore open the attached object out of curiosity and shortly discover that they have been owned. The malicious code injection takes place surreptitiously, and the perpetrating executable will start doing its dirty job. Spora ransomware kicks off with a scan for personal files. It looks inside local and network drives, focusing on the most popular data formats and skipping information that’s critical to the operating system.
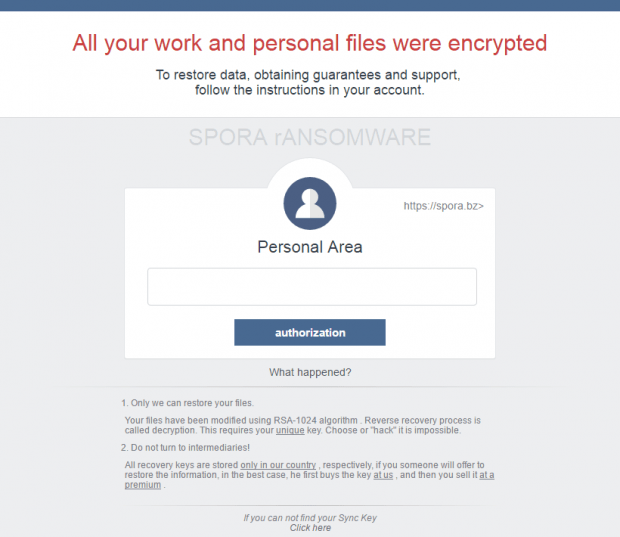
The encryption part of its nasty assignment does not bring about any external changes to the skewed files. Spora does not blemish them with any extra extensions, so their corrupted status isn’t clearly conspicuous. What it does in the open, though, is it drops the above-mentioned .KEY configuration file and a ransom note onto the desktop. The latter HTML document will have a random name consisting of five blocks of hex characters split by dashes. When this decryption manual is opened, it turns out to be a combo of a warning and login page that reads, “All your work and personal files were encrypted,” and displays a Personal Area field, located at https://spora.biz (https://spora.bz). The user is expected to enter their unique victim ID in this box, though it may sometimes be already filled out automatically. Doing so will get the infected person logged into their Client Page. Then, the user must upload the .KEY file in order to synchronize their machine with the decryption service. As it has been mentioned above, the ransom amount will vary depending on information gathered by the ransom Trojan. Big businesses will have to cough up more cryptocurrency for recovery than regular users.
Security analysts are at their wit’s end trying to decrypt Spora ransomware, but their efforts are futile thus far. They are confronted with high-profile threat actors who know what they are doing, so there is no obvious weak link in this extortion model. Here is an interesting point, though: Spora attempts to obliterate Shadow Copies of one’s files, but this process may not go all the way for whatever reason. Some of the instructions listed in this tutorial will help figure out whether this loophole can be leveraged to recover data. Last but not least, consider maintaining backups of the most valuable information in order to reduce the damage from ransom Trojans to a minimum.
Spora ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Spora ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by Spora ransomware
Workaround 1: Use file recovery software
It’s important to know that the Spora ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether Spora ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓