Softdecrypt@firemail.cc / maxspeed-dcr@tutamail.com virus removal

The ransomware phenomenon still instills fear like it used to. Falling victim to one of these nasty programs is the worst-case scenario imaginable for the average computer user, because they run the risk of losing the critical attributes of their digital life, that is, personal data. The lineage of blackmail viruses called Rapid ransomware is a typical example of this plague you don’t want to encounter. Moreover, it has been recently replenished with a fresh variant.
Table of Contents
What is the softdecrypt@firemail.cc / maxspeed-dcr@tutamail.com virus?
File-encrypting ransomware continues to be a serious concern regardless of the nosedive that this shady industry took earlier this year. While the weakest players have abandoned the extortion arena, the high-profile cybercriminal gangs stick with it and are having just about as much success as before. The Rapid ransomware is one of the strains that survived the decline, having spawned a new edition that instructs victims to reach out to the crooks at softdecrypt@firemail.cc or maxspeed-dcr@tutamail.com. The other clues suggesting that you are dealing with this particular harmful species include the .no_more_ransom file extension, as well as a ransom message named “How Recovery Files.txt” or a “recovery.txt” edition. The number of victims is reportedly growing at a steady pace at this point, which hints at a successful distribution campaign being underway.
The primary attack vector employed by the wrongdoers behind this edition of the Rapid ransomware boils down to RDP hacks. Here’s how it works: the criminals utilize ad hoc tools to scan the Internet for active remote desktop connections. Then, they try to brute-force RDP credentials in order to gain access to these systems. Unfortunately, a great deal of these connections use trivial or default login information, so the malefactors will undoubtedly manage to infiltrate them remotely. The next phase is a matter of manually executing the bad binary – it can be an entity named eslf.exe or info.exe.
Alternatively, the threat actors can deposit their dangerous code onto Windows PCs by means of spam. This workflow is quite prosaic: the crooks send booby-trapped emails to as many users as possible – mainly acting in cahoots with botnet operators – with the intriguing subjects of these messages encouraging recipients to open the attachment. The latter is a JS file camouflaged as an invoice, receipt, job offer or something like that. Once opened, the JavaScript code downloads the malicious executable behind the user’s back and fires it up.
No matter how exactly the Rapid ransomware has infected a host, the subsequent attack chain is uniform. It runs the “vssadmin.exe Delete Shadows /All /Quiet” command in order to obliterate all the shadow copies (previous versions) of the victim’s files. Next, it scans the local drive, network environment and removable drives for widespread types of data and employs a multi-stage encryption routine involving AES-256 and RSA key pair to lock these files down. The name of every such object gets appended with the .no_more_ransom extension, which is quite sarcastic of the felons.
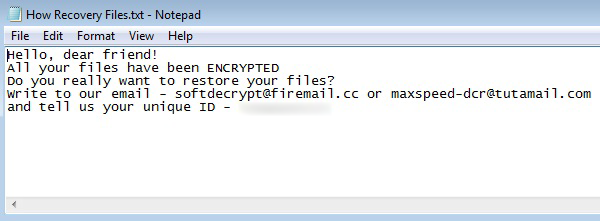
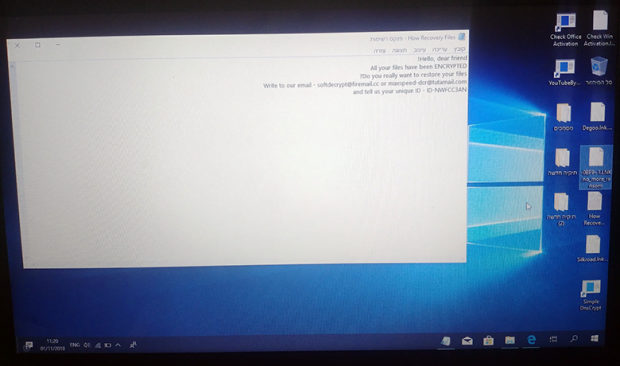
When done with this nefarious part of its raid, the malady drops ransom messages into encrypted folders. The name of these notes is “How Recovery Files.txt”, whereas some variants may use the “recovery.txt” document instead, or a combination of both. The text in these is quite laconic, saying:
Hello, dear friend! All your files have been ENCRYPTED
Do you really want to restore your files?
Write to our email – softdecrypt@firemail.cc or maxspeed-dcr@tutamail.com and tell us your unique ID.
The identifier is a victim-specific string in the following format: ID-[8 alphanumeric characters], so it may be something like ID-O12DWFRC. Having sent this information to either of the indicated email addresses, the victim will receive specific demands in response. The extortionists typically demand about $1,000 worth of Bitcoin for the private RSA key and data decryption software. However, some victims have stated that even after the payment they never got their files back. So think twice before engaging in the ransom deal. As a side note, it’s worth mentioning that a couple of other campaigns are currently also in rotation, in addition to the softdecrypt@firemail.cc (maxspeed-dcr@tutamail.com) version. They use the lub@wizrac.com, returnthefile@cock.li or sheldonleecooper@india.com contact email addresses instead.
Regardless of the Rapid ransomware mod, the ultimately effective decryption is only feasible in case the right RSA key is at the victim’s disposal. Otherwise, a few tips and tricks can be used to perform recovery based on data forensics.
Softdecrypt@firemail.cc / maxspeed-dcr@tutamail.com extension automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Softdecrypt@firemail.cc / maxspeed-dcr@tutamail.com ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the extension and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by Softdecrypt@firemail.cc / maxspeed-dcr@tutamail.com extension
Workaround 1: Use file recovery software
It’s important to know that the Softdecrypt@firemail.cc / maxspeed-dcr@tutamail.com extension creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the extension under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether Softdecrypt@firemail.cc / maxspeed-dcr@tutamail.com extension has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the extension itself does not belong inside your computer. Incidentally, it often comes with other extension, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this extension and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓