Remove search.yahoo.com browser hijacker in Chrome, Firefox, IE and Safari

Malicious players proved to be really good at harnessing legit online services and applications to their own advantage. As useful as it is, software bundling has become a true scourge over the years, bolstering numerous adware distribution waves. This technique has been weaponized for the umpteenth time, to put it mildly, for spreading a series of hijackers that redirect victims’ traffic to search.yahoo.com.
Table of Contents
What is the search.yahoo.com “virus”?
There is an ongoing web traffic monetization campaign that exploits one of the world’s most popular providers of online services, search.yahoo.com. The cybercrooks engaging in this activity have been pimping rogue browser helper objects on a large scale that tweak users’ Internet surfing preferences in order to force hits to a search engine they never opted for. To run this nefarious scheme, the crooks didn’t reinvent the wheel and resorted to the good ol’ bundling hype. The idea is to embed a potentially unwanted program (PUP) into installation clients for regular widespread software, such as common web navigation tools, media downloaders, Java plugins, Adobe Flash Player editions, VPN solutions and the like.
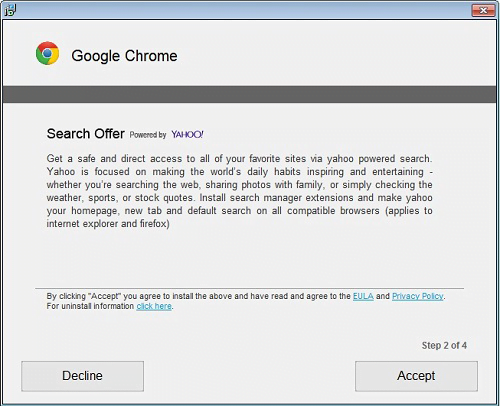
Unsuspecting users may be delighted to spot a free app they were looking for, so most of them will go ahead and click through all the setup steps in a headlong way. Some fine print on one of these steps, though, mentions that an extension like Search Offer powered by Yahoo, or Yahoo toolbar, will be added to their web browsers. Hardly anyone ever pays attention to these technicalities and, as a result, people end up in a loop of constant traffic redirects. The undesired add-on automatically modifies the main browsing preferences, including the default search engine, new tab page and the homepage. It doesn’t take a rocket scientist to understand that the outcome boils down to recurrently visiting search.yahoo.com.
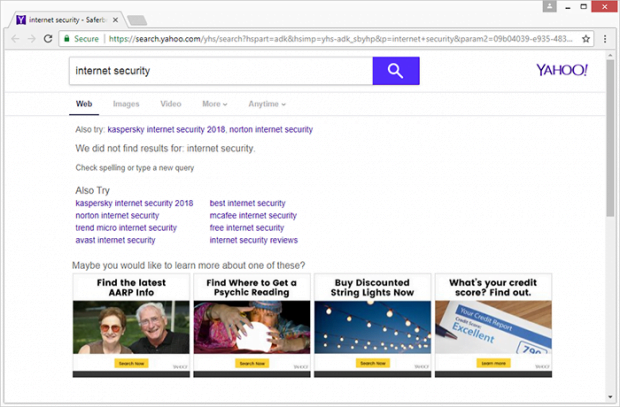
In some cases, the forcibly configured browsing defaults may resolve another pseudo search page, such as go.deepteep.com, search.searchvuzeau.com, search.searchtheweb.today, search.searchucp.com, search.searchidd.com, or go.pajosh.com, mybrowserbar.com. These are dummy domains with no informative value of their own that are set up to capture user hits and further divert all keyword lookup instances to search.yahoo.com. Most of the time, the resulting search results will contain nothing but sponsored links and other forms of advertisements. This gives a clue about the main goal of the criminals – they seek to monetize user hits via ad views and pay-per-click schemes.
An additional caveat to those infected is that the threat actors get access to their sensitive information, such as browsing history, bookmarked sites, and quite possibly even login credentials. At the end of the day, the search.yahoo.com related malware annoys victims a lot, poses risk to their privacy, and therefore should be removed from a contaminated system as soon as possible.
Search.yahoo.com hijacker automatic removal
The extermination of Search.yahoo.com PUP can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped out from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Search.yahoo.com remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the hijacker removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the infection. However, it might be a good idea to consider ascertaining the hijacker is gone for good.
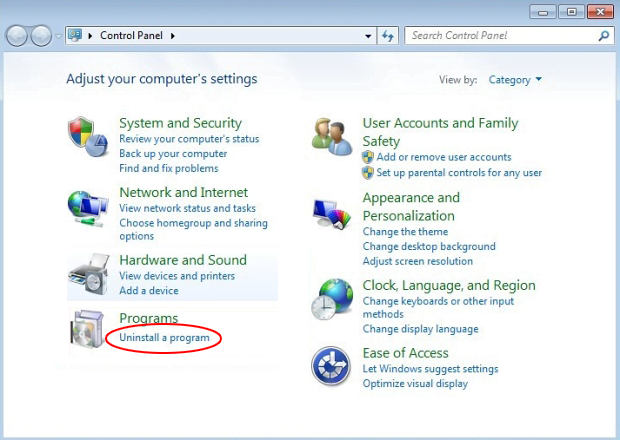
Remove Search.yahoo.com hijacker using Control Panel
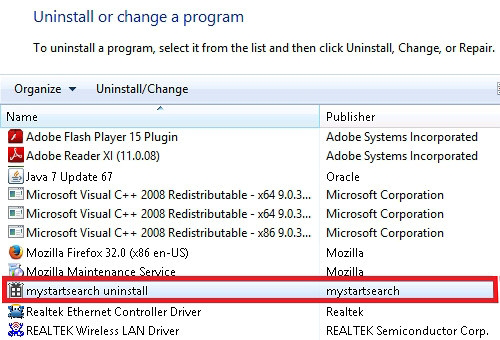
- Open Control Panel. On Windows XP / Windows 8, go to Add or Remove Programs. If your OS is Windows Vista / Windows 7 / Windows 10, choose Uninstall a program

- Look down the list and locate an app that appears fishy. Click the Uninstall/Change (Change/Remove) option to get the intruder removed if spotted

Search.yahoo.com hijacker removal by resetting the affected browser
Please take into consideration that as effective as it is, the procedure of restoring browser defaults will lead to the loss of personalized settings such as saved passwords, bookmarks, browsing history, cookies, etc. In case you are not certain this outcome is suitable despite its obvious efficiency, it’s advised to follow the automatic removal method described in one of the previous sections of this tutorial.
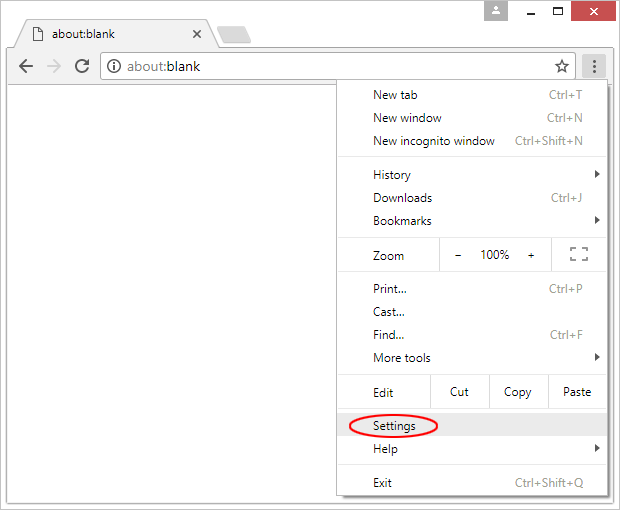
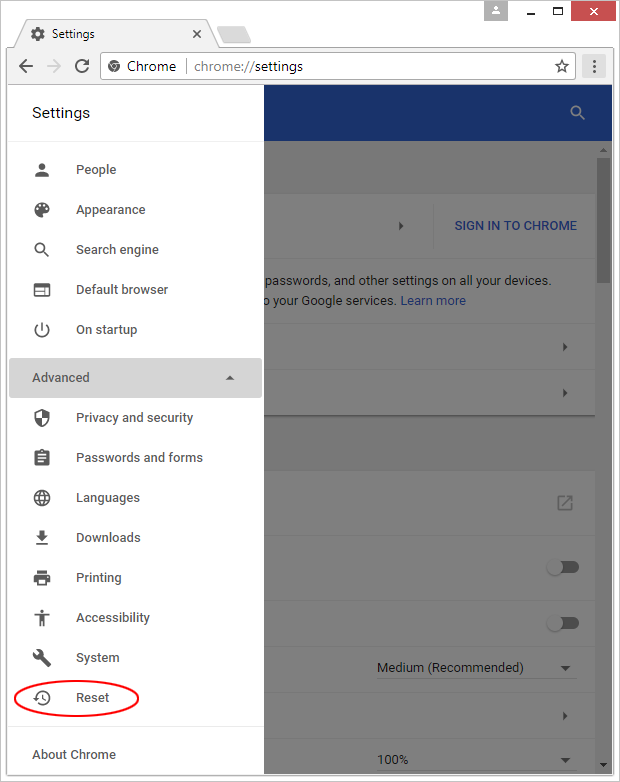
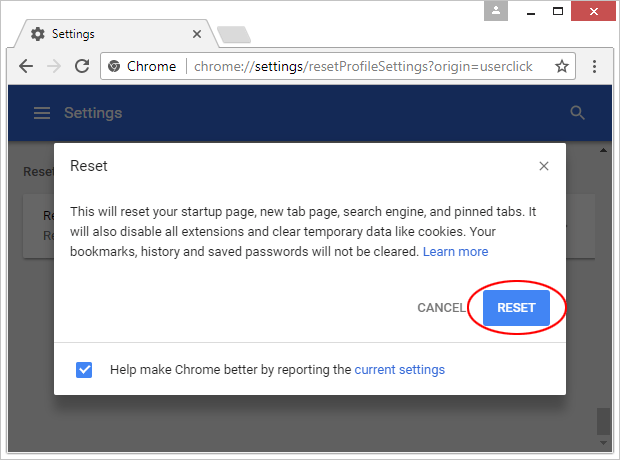
Reset Google Chrome
- Click on the Chrome menu icon and select Settings

- Locate the Advanced option under Settings and click on it to expand the menu. Then, pick the Reset button at the bottom

- When a new screen appears, hit Reset once again

- Chrome will now display a confirmation dialog box listing the types of data that will be lost if you proceed. Read the message carefully and, if you’re sure, click Reset

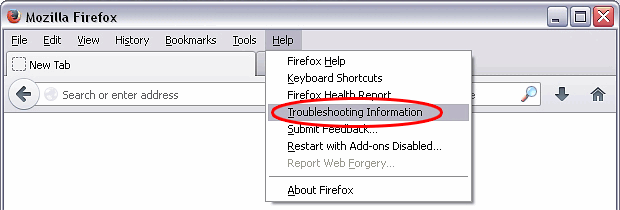
Reset Mozilla Firefox
- Click on Help menu and select Troubleshooting Information from the drop-down list, or type about:support in the URL field

- On the Troubleshooting Information screen, click Refresh Firefox option and confirm the procedure on another dialog

Reset Internet Explorer
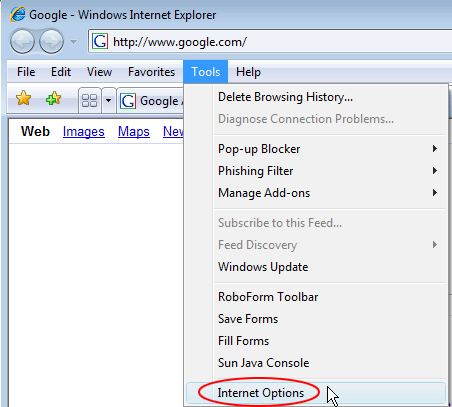
- In IE, go to Tools and select Internet Options from the list

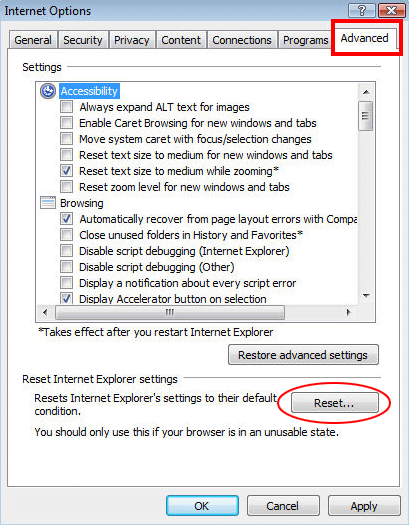
- Hit the Advanced tab and click on the Reset option

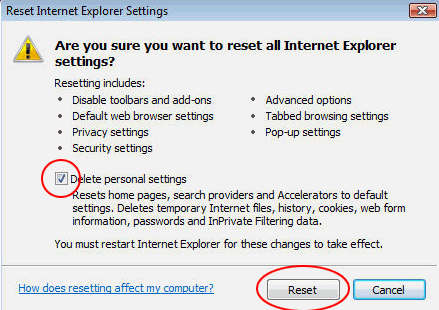
- IE will now display Reset Internet Explorer Settings box, where you should put a checkmark next to Delete personal settings option and click Reset at the bottom

Verify whether Search.yahoo.com hijacker has been completely removed
For certainty’s sake, it’s advised to repeatedly run a scan with the automatic security software in order to make sure no harmful remnants of this PUP are left inside Windows Registry and other operating system locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓