Remove Search Encrypt (searchencrypt.com) extension in Chrome/Firefox/IE
Online privacy has been the talk of the town since it became clear that big data aggregates and governments can harvest people’s personally identifiable information on the Internet. Most people don’t care much about that, but some choose to keep their searches and web activity private by using anonymization services and the like. The Search Encrypt tool claims to meet the requirements of the latter category of users, but it turns out that its tactics are controversial.
Table of Contents
What is the Search Encrypt virus?
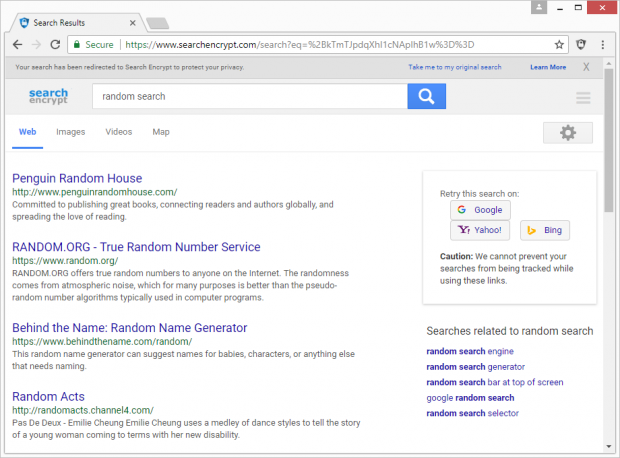
Search Encrypt is marketed as a solution built with privacy in mind. It purports to safeguard users’ sensitive online data from being tracked by major tech companies, but does it in a fairly bizarre way. In order to allegedly keep a person on the safe side and away from surveillance, it redirects their searches being made on popular search engines to its own service hosted at searchencrypt.com. Although people can opt out of these search redirects via the app’s menu accessible from an icon embedded in the browser, this may not appear to be an intuitive option for many and they keep visiting the unwanted page over and over. The results pages will typically include a bevy of ads, which are the main monetization channel of the service, according to its official site.
One of the clues pointing to the questionably benign essence of Search Encrypt is the way it is spreading. The tool is a cross-browser extension that users should normally be able to add to Chrome, Firefox and Internet Explorer. However, this add-on often ends up on computers without admins’ knowledge and consent. That’s because this propagation vector relies on bundling, a technique that may promote potentially unwanted applications along with popular freeware entities. The catch is in the installation client that’s supposed to streamline the setup process. While clearly disclosing the installation details of the main product, it tends to conceal the inclusion of extra items in the compound setup routine. As a result, people authorize the trespass while believing they are only accepting the terms for the app of choice.
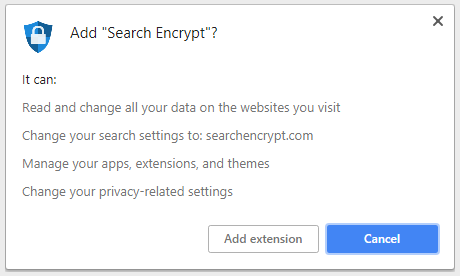
The privileges Search Encrypt gets on a host speak volumes about its intensions. It can change one’s privacy-related settings, read and modify data on all websites being visited, and replace the default search service with searchencrypt.com. Few people ever get to read those technicalities, so they find themselves in a predicament where recurrent diverts of web traffic interfere with their regular Internet surfing. When trying to look up arbitrary information on common search engines, victims get a prompt saying, “Your privacy will be protected by redirecting your search to Search Encrypt.” Consequently, any query entered in the box will return results via searchencrypt.com instead of the favorite provider. The SERPs will be inundated with sponsored links, which isn’t very welcome, to put it mildly.
All in all, while Search Encrypt supposedly encodes users’ searches locally and automatically erases browser history after 15 minutes of hiatus, it is a mixed blessing. A lot of people don’t remember installing this tool, because the setup is surreptitious and can take place beyond their awareness and approval. If this browser add-on is causing issues and diminishes user experience, it is recommended to uninstall it using the following workflow.
Search Encrypt extension automatic removal
The extermination of Search Encrypt hijacker can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped out from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Search Encrypt remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the PUP removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the infection. However, it might be a good idea to consider ascertaining the extension is gone for good.
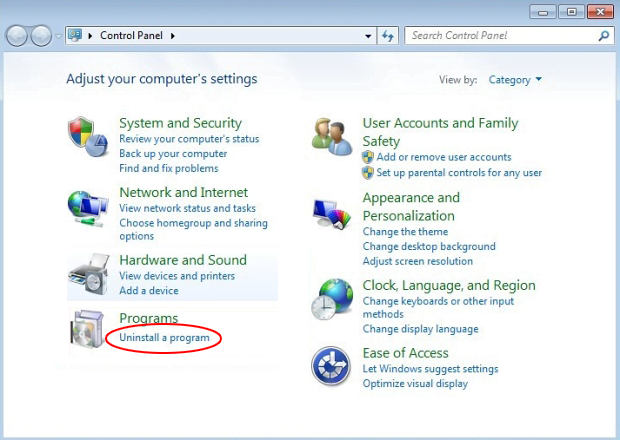
Remove Search Encrypt extension using Control Panel
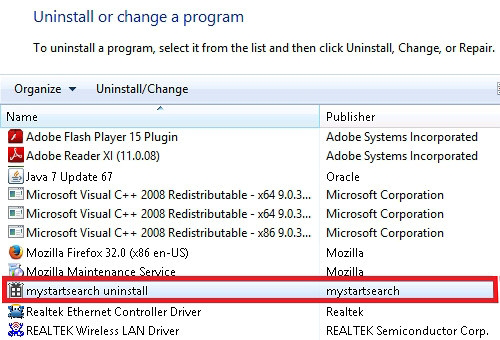
- Open Control Panel. On Windows XP / Windows 8, go to Add or Remove Programs. If your OS is Windows Vista / Windows 7 / Windows 10, choose Uninstall a program

- Look down the list and locate an app that appears fishy. Click the Uninstall/Change (Change/Remove) option to get the intruder removed if spotted

Search Encrypt extension removal by resetting the affected browser
Please take into consideration that as effective as it is, the procedure of restoring browser defaults will lead to the loss of personalized settings such as saved passwords, bookmarks, browsing history, cookies, etc. In case you are not certain this outcome is suitable despite its obvious efficiency, it’s advised to follow the automatic removal method described in one of the previous sections of this tutorial.
Reset Google Chrome
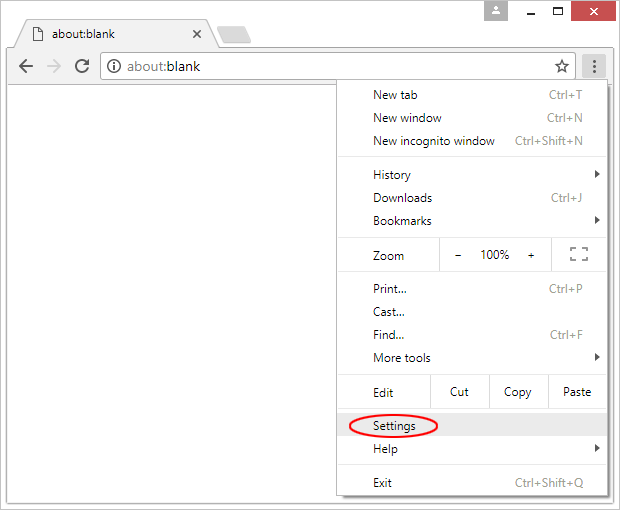
- Click on the Chrome menu icon and select Settings

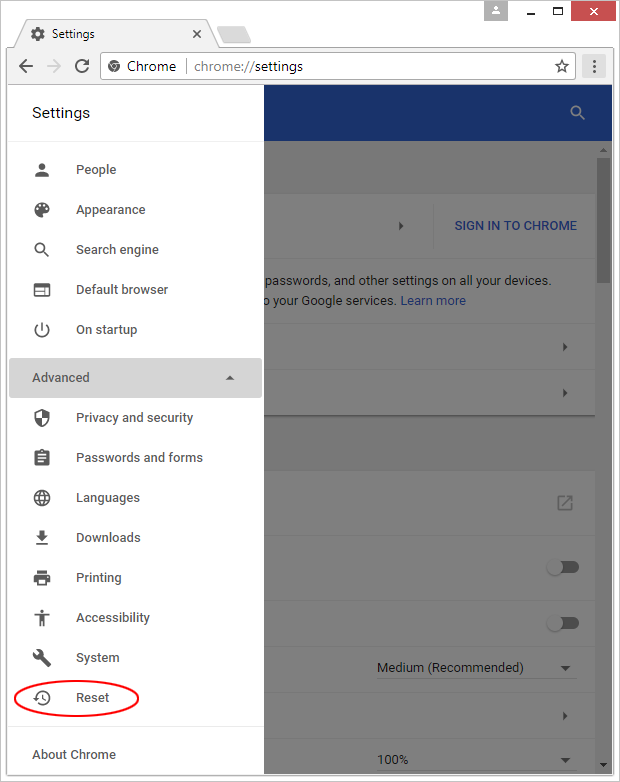
- Locate the Advanced option under Settings and click on it to expand the menu. Then, pick the Reset button at the bottom

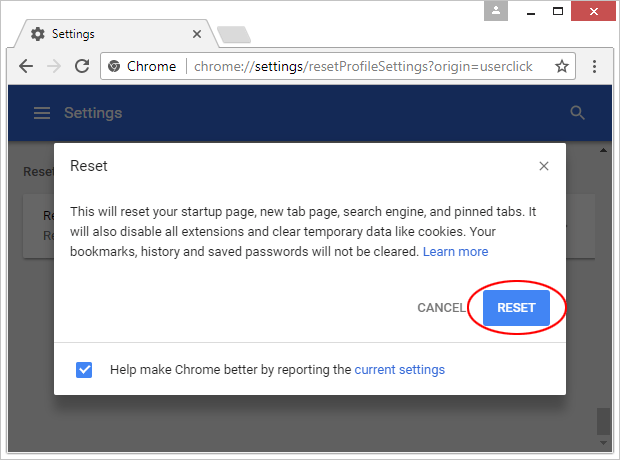
- When a new screen appears, hit Reset once again

- Chrome will now display a confirmation dialog box listing the types of data that will be lost if you proceed. Read the message carefully and, if you’re sure, click Reset

Reset Mozilla Firefox
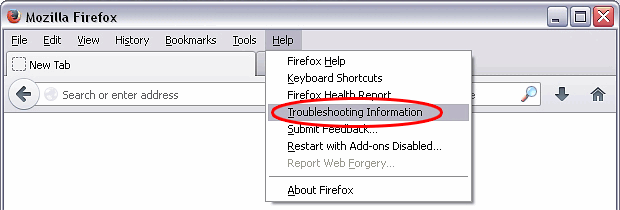
- Click on Help menu and select Troubleshooting Information from the drop-down list, or type about:support in the URL field

- On the Troubleshooting Information screen, click Refresh Firefox option and confirm the procedure on another dialog

Reset Internet Explorer
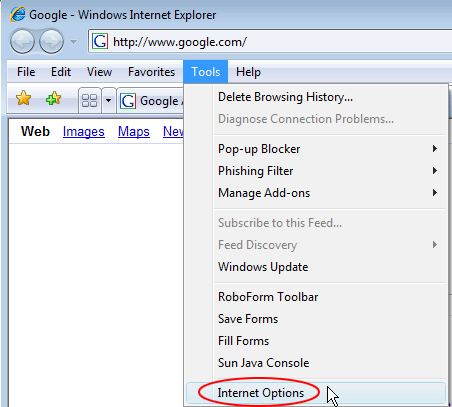
- In IE, go to Tools and select Internet Options from the list

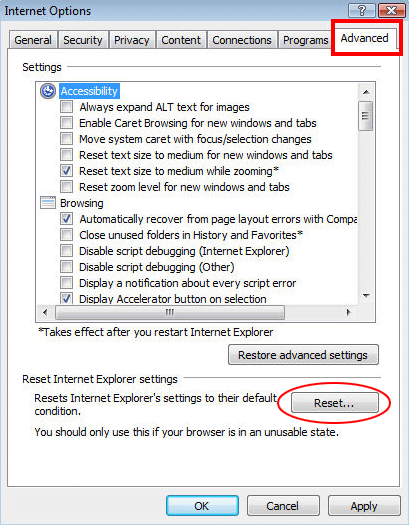
- Hit the Advanced tab and click on the Reset option

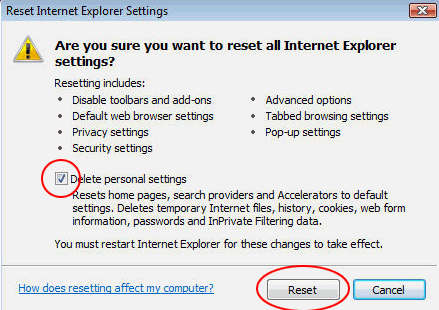
- IE will now display Reset Internet Explorer Settings box, where you should put a checkmark next to Delete personal settings option and click Reset at the bottom

Verify whether Search Encrypt extension has been completely removed
For certainty’s sake, it’s advised to repeatedly run a scan with the automatic security software in order to make sure no harmful remnants of this hijacker are left inside Windows Registry and other operating system locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓