Remove Safebrowsing.biz virus in Chrome, Firefox and IE
Monetization of web traffic is a type of activity that cyber threat actors heavily engage in their malicious schemes. This tactic features a twofold benefit for the hackers. It is profitable due to third parties’ interest in the associated advertising opportunities. Furthermore, no one can really sue and prosecute them for hijacking web browsers, because it’s the end users who accept the obtrusive terms without realizing the risk.
Safebrowsing.biz seems like a fairly commonplace web search portal that accommodates a keyword lookup functionality and provides links to potentially useful resources in one place. In fact, there are no hidden scripts, exploits or drive-by downloads on that page that could harm a visitor’s computer in any way. When analyzing infections like this, though, it makes sense establishing the ties between a domain name and a supporting application that drives traffic to the site. There is an affiliated cross-browser add-on that configures popular Internet navigation clients to resolve Safebrowsing.biz URL upon certain standard events. The extension triggers an automatic redirect when the user opens Mozilla Firefox, Google Chrome or Internet Explorer. The same happens when the victim opens a new tab or uses the web address bar to type a search query and get the results.
The underlying effect involves a replacement of the user’s online preferences with the URL under consideration. This occurs without prior authorization of such changes, at least that’s what the infected users think. However, the phase of terms acceptance is typically in place across these attack incidents. When downloading a bundle of several freeware products, the default setup mode implies that all components of the package will end up on the PC as long as the person clicks ‘OK’ or ‘I Agree’ once. Most adware threats and other PUAs (Potentially Unwanted Applications) are distributed in this fashion, where technically users opt into using them but typically aren’t aware of it.
Having obtained unsanctioned control over the homepage, search and new tab preferences in all browsers running on the host machine, the adware keeps rerouting the victim to Safebrowsing.biz. The redirects may also occur when a random application is opened, because the offending code tends to alter the shortcut settings for software other than browsers alone. The unwelcome website in question returns search results by a different provider that’s legitimate. The results pages will contain ads above the fold – that’s the whole gist of this campaign.
Any sane user’s first reaction under these circumstances is to uninstall the troublemaking add-on and enter the correct values for the skewed preferences. Unfortunately, this methodology doesn’t always work with adware like Safebrowsing.biz. What does help is a tried and trusted anti-hijacking technique.
Table of Contents
Safebrowsing.biz adware automatic removal
The extermination of Safebrowsing.biz hijacker can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped out from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Safebrowsing.biz remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the adware removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the infection. However, it might be a good idea to consider ascertaining the adware is gone for good.
Remove Safebrowsing.biz adware using Control Panel
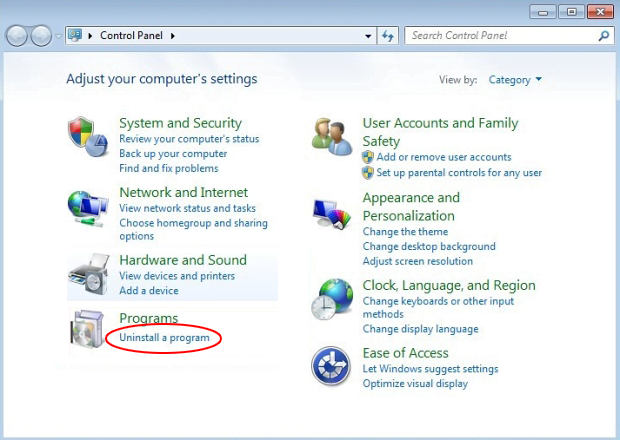
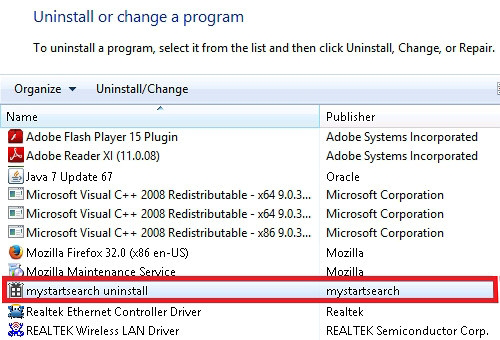
- Open Control Panel. On Windows XP / Windows 8, go to Add or Remove Programs. If your OS is Windows Vista / Windows 7 / Windows 10, choose Uninstall a program

- Look down the list and locate an app that appears fishy. Click the Uninstall/Change (Change/Remove) option to get the intruder removed if spotted

Safebrowsing.biz adware removal by resetting the affected browser
Please take into consideration that as effective as it is, the procedure of restoring browser defaults will lead to the loss of personalized settings such as saved passwords, bookmarks, browsing history, cookies, etc. In case you are not certain this outcome is suitable despite its obvious efficiency, it’s advised to follow the automatic removal method described in one of the previous sections of this tutorial.
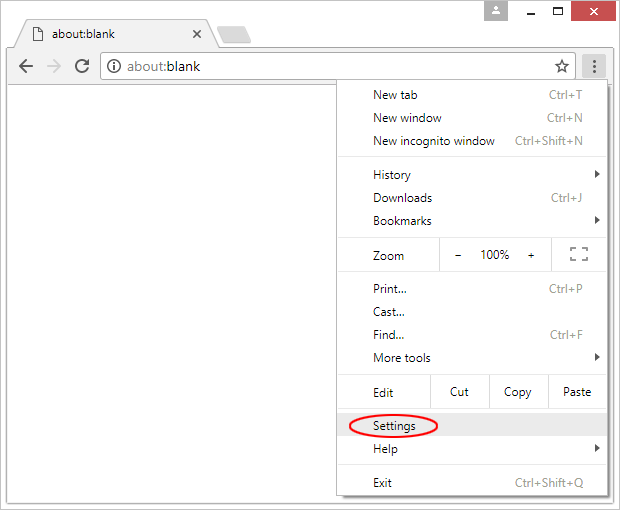
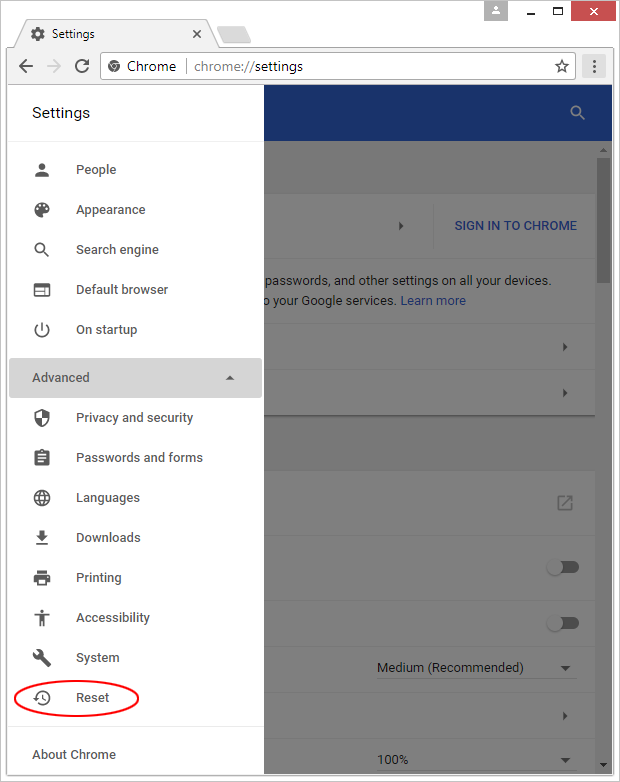
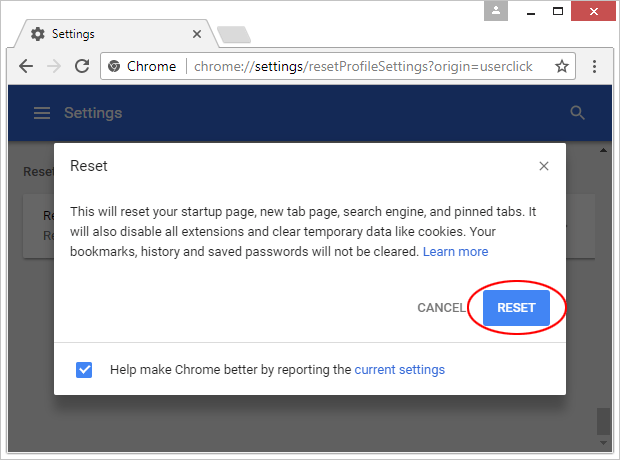
Reset Google Chrome
- Click on the Chrome menu icon and select Settings

- Locate the Advanced option under Settings and click on it to expand the menu. Then, pick the Reset button at the bottom

- When a new screen appears, hit Reset once again

- Chrome will now display a confirmation dialog box listing the types of data that will be lost if you proceed. Read the message carefully and, if you’re sure, click Reset

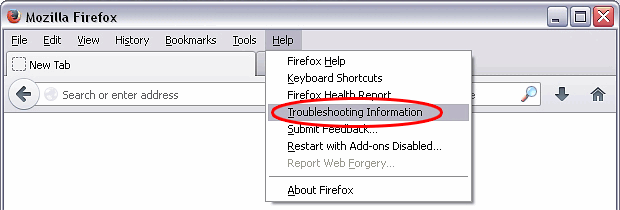
Reset Mozilla Firefox
- Click on Help menu and select Troubleshooting Information from the drop-down list, or type about:support in the URL field

- On the Troubleshooting Information screen, click Refresh Firefox option and confirm the procedure on another dialog

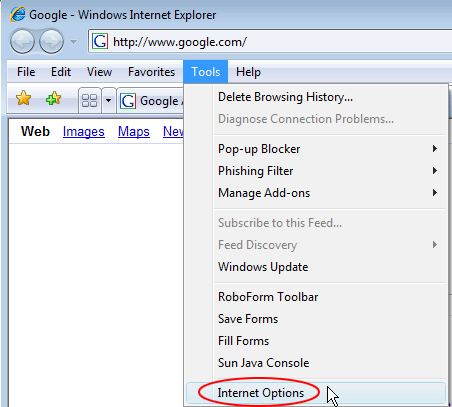
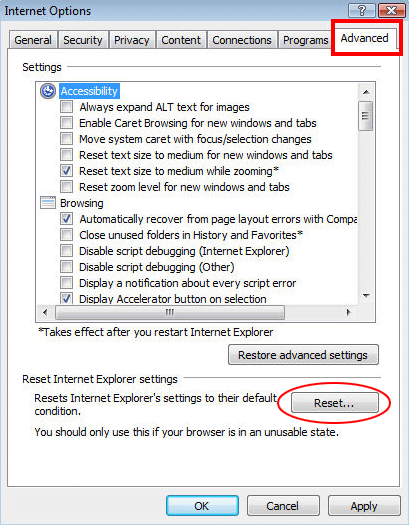
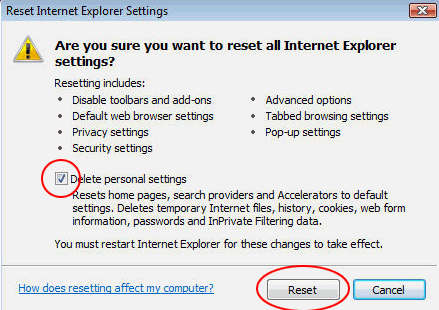
Reset Internet Explorer
- In IE, go to Tools and select Internet Options from the list

- Hit the Advanced tab and click on the Reset option

- IE will now display Reset Internet Explorer Settings box, where you should put a checkmark next to Delete personal settings option and click Reset at the bottom

Verify whether Safebrowsing.biz adware has been completely removed
For certainty’s sake, it’s advised to repeatedly run a scan with the automatic security software in order to make sure no harmful remnants of this hijacker are left inside Windows Registry and other operating system locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓