Remove Reyptson ransomware and decrypt .reyptson virus files
Ransom Trojan rarely deviate from the well-trodden extortion route. The new sample called Reyptson is one of the very few that leverage offbeat tactics when deploying its infection chain. It performs some extra reconnaissance on a contaminated computer, harvesting the victim’s email credentials in order to self-spread via spam automatically generated from the host.
Table of Contents
What is the Reyptson ransomware?
Reyptson ransomware does not appear to represent any known lineage of crypto infections. Not only does it feature unique IOCs (indicators of compromise), but it also behaves in a more opportunistic fashion than the average strain out there. If the perpetrating code discovers that the victim uses the Thunderbird email client, it tries to get hold of email login information. In case this part of the compromise is successful, Reyptson starts sending out rogue messages to the infected user’s contacts retrieved as part of this data harvesting routine. These emails with the subject “Folcan S.L. Facturacion” contain a link leading to a PDF document masqueraded as an invoice. The rest of the malign workflow is classic: once the recipient downloads the bogus invoice, the host system gets infected. This unusual infection loop keeps the campaign moving forward autonomously.
So much for the non-standard properties of this ransomware. Let’s now scrutinize its commonplace hallmark signs. Based on the names of files involved in the proliferation mechanism, it’s easy to figure out that the threat zeroes in on Spanish-speaking users. As soon as it gains a foothold on a machine, it reaches out to a C2 server to transmit system-specific data such as the username of the plagued person as well as timestamp of when the infiltration occurred. In response, Reyptson receives an encryption key from the Command & Control portal. Then, the infection scours the local drive, removable media and network shares for more than a hundred popular file types, skipping such paths as Windows, Program Files, Recycle Bin, AppData and System Volume Information along the way.
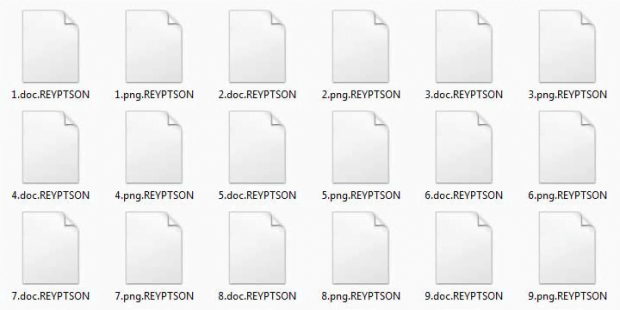
The ransomware then applies AES-128 cipher to lock down all personal files spotted during the stealth scan. As opposed to many counterparts, it leaves the original filenames intact. However, it appends the .reyptson extension to each one. To let the victim know what’s going on, the Trojan drops a rescue note called Como_Recuperar_Tus_Ficheros.txt onto the desktop and into folders with hostage data. The Spanish name of this document translates to “How to recover your files”. The ransomware also deposits an executable that generates an extra warning on the screen. All editions of the ransom note provide links to access the Reyptson payment service page via Tor. The page reads, “Todos tus documentos han sido cifrados por Reyptson,” which means “All your documents have been encrypted by Reyptson” in English.
To get their data back, victims are instructed to pay €200 worth of Bitcoin. If a deadline of 72 hours isn’t met, the amount will go up to €500. Although there is no free decryptor supporting the Reyptson ransomware at this point, it’s recommended to refrain from submitting the ransom. Crooks are crooks, whether they operate online or in real world. So there can be no certainty that they will carry through with their promises even if they receive a payment. The first thing to do is try alternate options, such as forensic techniques of data restoration. And be sure to get rid of the malicious code proper otherwise it may re-encrypt files after successful recovery.
Reyptson ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Reyptson ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by Reyptson ransomware
Workaround 1: Use file recovery software
It’s important to know that the Reyptson ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether Reyptson ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓