Readme.hta – Cerber Ransomware update
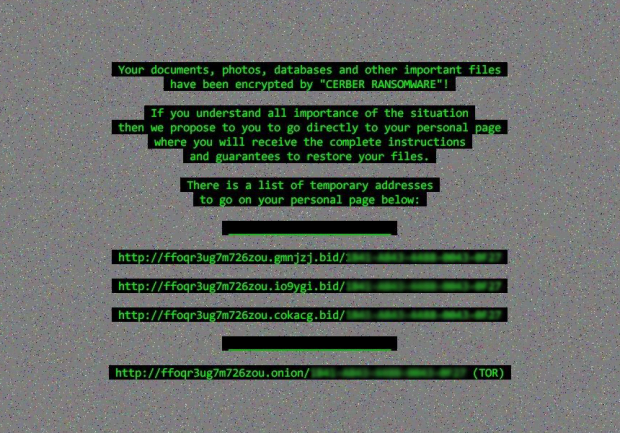
There are no extraordinary tweaks made to the prolific Cerber Ransomware in the course of the fresh update. It still leverages the same strong cryptosystem to lock a victim’s files. As before, it changes the desktop wallpaper to a grayish image with random pixels and some warning text in green font. The circulation peculiarities are also preserved in their tried and tested state. Some changes, however, are in place and noteworthy.
While the Cerber devs have apparently decided not to reinvent the wheel and modify what already works flawlessly, the new fourth edition has a number of traits that make it distinguishable from the three predecessors. The first difference that strikes the eye is that the infection has switched to the use of random extensions consisting of four hexadecimal characters. The extensions therefore take a shape similar to .bed5, .bf05, or .a7b6. These strings are generated uniquely for every victim. Just like the previous iteration of the plague, the one in question also scrambles filenames and replaces them with 10 symbols that have no obvious likeness to the original values. Ultimately, a regular file named report.docx will morph into something like pRvLk9osB0.bed5.
One more notable distinction is the ransom note. Whereas the forerunner would create three copies of recovery instructions, namely # HELP DECRYPT #.html (.url, .txt), the most recent variant of Cerber Ransomware only drops a file named README.hta into folders with ciphered data and on the desktop. This manual features language selection out of 13 available languages and provides down-to-earth directions on restoring the blatantly encrypted files. It reads, “Can’t you find the necessary files? Is the content of your files not readable? It is normal because the files’ names and the data in your files have been encrypted by Cerber Ransomware.” Then goes a part saying that the data isn’t damaged and the modification is reversible.
According to README.hta, the special tool called Cerber Decryptor poses the only way to decrypt the files safely. A victim is told to buy this software on their personal page. For anonymity reasons, this page is protected by Tor, or The Onion Router, therefore the infected user must download and install the Tor Browser first. The Cerber Decryptor page also has a language selection script and a graphical verification feature. Once logged on, the victim will see a generic warning message again, the size of the ransom to submit, a countdown clock, and the criminals’ Bitcoin address for payments. Within the first five days, the ransom amounts to 0.1394 BTC, or about 84 USD. After five days, the price doubles and thus reaches 0.2788 BTC, or 169 USD.
The text in the desktop background set by the updated Cerber Ransomware basically duplicates the instructions provided in README.hta ransom note and the personal decryption page. It lists several temporary Tor URLs to visit the dedicated recovery site. All in all, the latest update hasn’t introduced any appreciable sophistication to this nasty threat. It is still the same Cerber with unbreakable crypto and a robust Command and Control infrastructure. Although rescuing the encrypted files may only be doable by paying the ransom in many cases, it certainly won’t hurt to try a couple of additional recovery techniques.
Table of Contents
Cerber ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Cerber ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by Cerber ransomware
Workaround 1: Use file recovery software
It’s important to know that the Cerber ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether Cerber ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓