.Rapid ransomware decryptor and removal
When it comes to ransomware, the word ‘rapid’ is no longer just a regular adjective. It also designates a blackmail virus infecting Windows computers on a fairly large scale since late January 2018. The crooks at the helm of this extortion wave appear to be Russians and operate quite a weird malspam campaign. Keep reading to learn more details.
Table of Contents
What is the .Rapid ransomware?
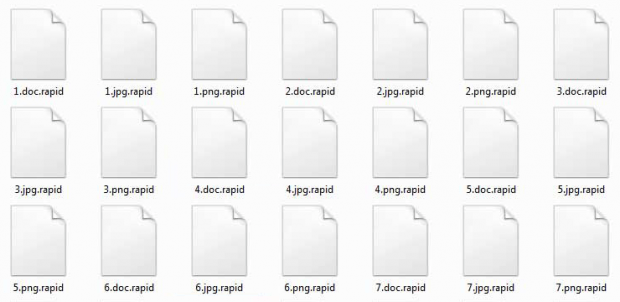
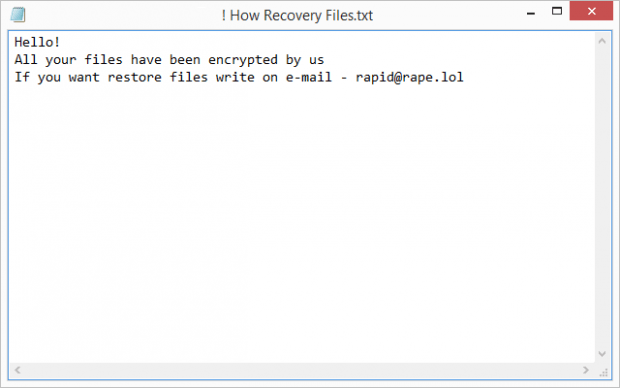
Rapid ransomware is one of the first competently designed file-encrypting infections that surfaced this year and stood out from the dull crowd of small and crude ransom Trojans popping up every so often. Whereas it goes a well-trodden route and doesn’t introduce any particular novelty, its cryptographic aspect is flawless and therefore the hostage data isn’t decryptable without the private key only the attackers have. The culprit does not go with a GUI and so it interacts with victims via a ransom note. In a nutshell, the main conspicuous symptoms of the Rapid ransomware attack are as follows: the names of encoded files are appended with the .rapid extension; and a ransom how-to named “! How Recovery Files.txt” is dropped on the desktop.
This offending program reaches new host computers via spam. One of these campaigns doesn’t make a whole lot of sense. The booby-trapped emails pretend to be urgent messages from the IRS (Internal Revenue Service). Although that’s a U.S. federal agency, the sending account is on a UK domain, and the contents of the malicious Word attachment are German. In spite of this surreal combo, the malspam wave is having some success infecting users. The attached file prompts recipients to enable editing, which translates to turning on Office macros. Once this happens, an obfuscated VBA script surreptitiously downloads the Rapid ransomware onto the system.
Having crept its way into a PC, the pest looks for data that potentially has the biggest value to the victim. In order to separate the wheat from the chaff, it scans the hard drive for items with specific extensions, the list thereof being predefined. When all the matching objects have been located, the ransomware utilizes RSA asymmetric cipher to lock them down. It means no regular software is capable of opening those files as long as they are in that state. Additionally, the troublemaking code skews filenames by adding the .rapid extension to each one. In the upshot of this activity, a sample file named, say, Bookmark.jpg will turn into Bookmark.jpg.rapid.
To inform the infected user on their options regarding the recovery process, the Rapid ransomware leaves a rescue note on the desktop. There have been several different variants of it reported by victims. The most common one is named “! How Recovery Files”, with others being “Recovery.txt”, “! How Decrypt Files.txt”, and “Readme.txt”. The note says, “Hello! All your files have been encrypted by us. If you want restore files write on e-mail – rapid@rape.lol.” Obviously, the victim is instructed to contact the villains over email, and the response from them will provide concise decryption steps. The main demand is for the user to send about $3,500 worth of Bitcoin to the crooks’ BTC address.
Interestingly, if a victim says they are from Russia and proves it, the extortionists claim to provide the decryptor and the secret key for free. This fact gives a clue about the black hats’ likely origin and location. Anyway, if you meet that geo-criterion, perhaps telling it to the attackers is worth a shot. Otherwise, follow the walkthrough below to get rid of the perpetrating code and try to recover .rapid files.
Rapid extension automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Rapid ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the extension and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by Rapid extension
Workaround 1: Use file recovery software
It’s important to know that the Rapid extension creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the extension under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether Rapid extension has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the extension itself does not belong inside your computer. Incidentally, it often comes with other extension, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this extension and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓