Uninstall Quick Swipe virus from Android
When downloading apps for the Android mobile platform, the last thing users want is get a piece of nagging code that constantly interrupts device usage. Most of these issues occur as a result of software downloads from unofficial resources – in the case of Android, it’s anything other than Google Play. The application called Quick Swipe, for instance, gets around the normal authorization and causes a great deal of problems when inside a smartphone of tablet.
Quick Swipe is available on questionably safe web portals but cannot be found on the operating system’s proprietary marketplace. This fact alone smells fishy. It turns out, however, that the majority of infected users never really get the chance to verify this applet’s origin and reputation. That’s because its installation is barely noticeable due to the bad facet of social engineering that the distributors leverage to peddle their worthless product. The furtive propagation chain is as follows: a user stumbles upon a free program such as a funny game and decides to install it; then, a package of apps slithers into the gadget rather than just the originally declared utility; in the long run, Android starts acting up. The aforementioned bundle includes Quick Swipe, therefore it appears without proper awareness on the customer’s end.
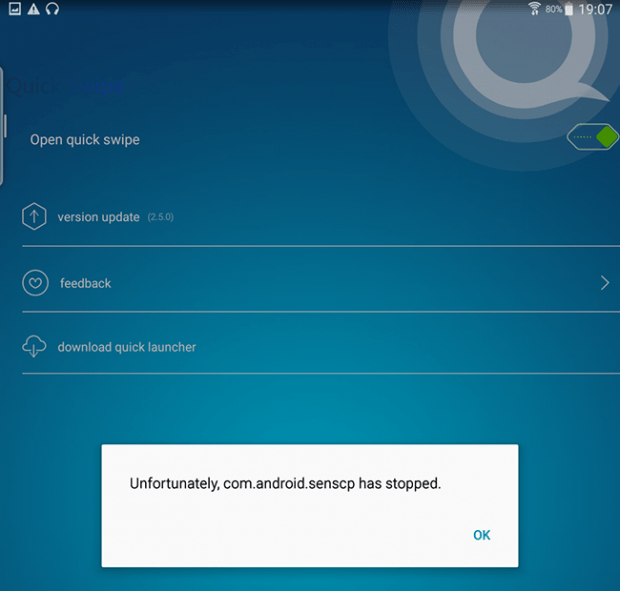
According to a description of Quick Swipe provided on one of the download repositories promoting it, the application features a floating widget that contains the most frequently used system settings and programs. Although this functionality doesn’t sound unwelcome at all, the way it is implemented in this case is a bummer. The victims experience an intense popup activity, where a message saying “Unfortunately, com.android.senscp has stopped”, or similar, keeps splashing up. This takes place a few seconds after a reboot and quite randomly in the course of the device use.
Quick Swipe also calls forth a predicament where the infected Android phone or tablet begins to operate slower. Even powerful gadgets with plenty of CPU and free memory space under the hood suddenly turn into sluggish nuisances that take twice as much time to process simple commands compared to the usual state of things. The affected digital appliances may also be forced to get into a reboot loop or shut down once in a while.
Another nasty effect has to do with the privacy violation aspect. The snag is all about the methodology that Quick Swipe uses to propagate. When a targeted user installs the virus-laden package, they unwittingly accept the imposed terms of service and thus give the malware a broad spectrum of permissions. The offending app can hence access the person’s messaging history, contacts, geolocation, microphone, camera, web browsing history and the like. It’s certainly best to get rid of this Android program as it makes the system unstable and slow, and it also puts the user’s privacy at risk. Keep reading to learn how.
Quick Swipe undefined removal
What you need to do is uninstall the application that’s causing trouble. As it has been mentioned, however, disabling and removing the virus in regular mode is to no avail, so the steps below are must-follow.
1. Boot the device into safe mode
– Press and hold the Power button until the respective screen pops up
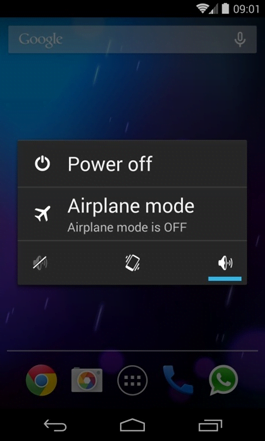
2. Now tap and hold the option that says Power off. Depending on the vendor and the phone model, the methods can vary. If nothing happens as a result of the above manipulations, power down the device, then press and hold the Volume Down and Volume Up buttons simultaneously while it’s starting back up.
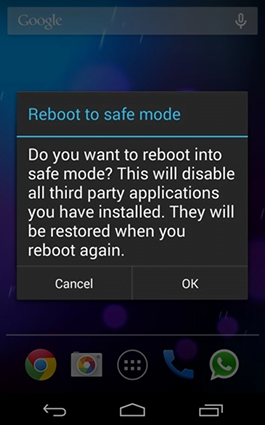
3. Confirm rebooting into safe mode by tapping OK
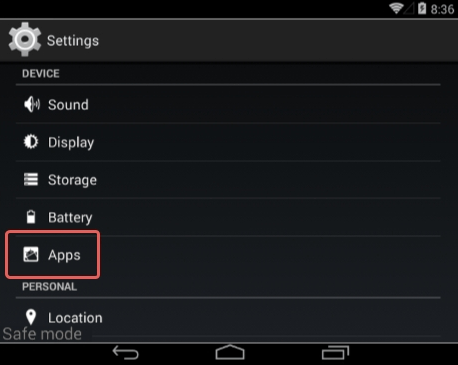
4. When in safe mode, go to Settings and select Apps
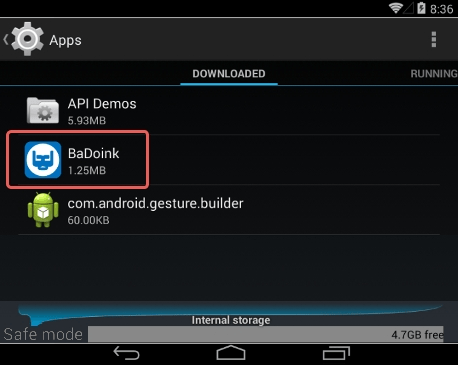
5. Look down the list of programs and locate a suspicious app or apps that were recently installed
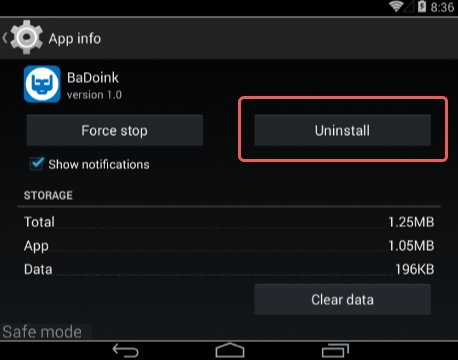
6. Tap each potentially unwanted app in turn and select the Uninstall option. If this button is not active, try Force stop first
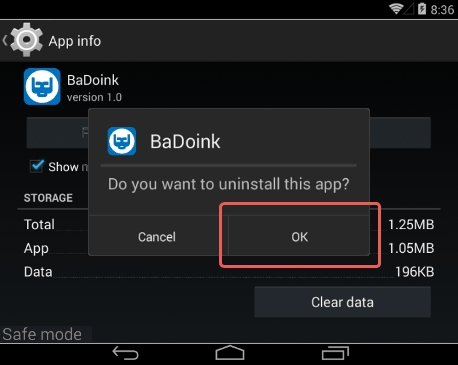
7. Tap OK on the confirmation dialog to uninstall the potentially unwanted app
8. Restart into standard mode. The Quick Swipe undefined should have now vanished from your Android device. You might also want to consider installing a mobile security solution to prevent attacks of this sort further on.
Posted in: KnowledgeBase
Leave a Comment (0) ↓