Philadelphia Ransomware virus decryptor and removal
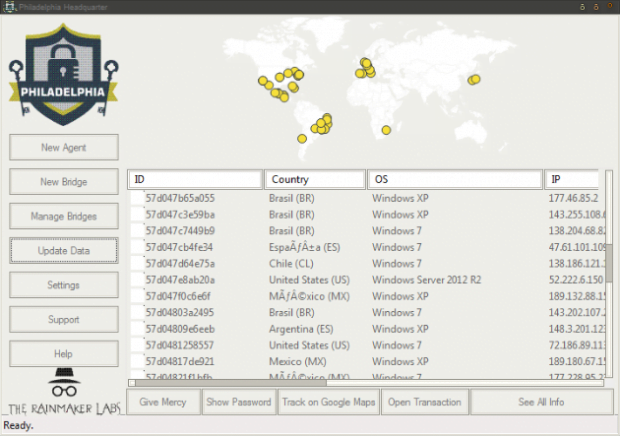
The ins and outs of the Philadelphia ransomware reflect the heterogeneity of the extortion-centered cybercrime underground. This sample is backed by a Ransomware-as-a-Service platform advertised on darknet sites and forums as an extensively flexible service to get the bang for one’s buck. Everyone interested can purchase a copy of the perpetrating program for $400 and cook up a money-harvesting campaign of their own.
Table of Contents
What is the Philadelphia ransomware?
This strain is affiliated with the notorious Stampado family, so it’s got an eventful background as well as its architects’ tried-and-tested tech skills behind it. The Philadelphia ransomware never stayed on the sidelines of e-extortion trends since it emerged. It is part of a well-orchestrated RaaS network boasting high customizability and advanced statistics tracking. Furthermore, here are some bare facts on this one: the code proper is written in AutoIT scripting language; the virus employs AES-256 cryptosystem to cripple victims’ files; it scrambles original filenames with RC4 stream cipher and appends the .locked extension to the mutilated strings. The crooks who buy a build of Philadelphia infection can define paths on plagued computers to scan for files, edit text on the program’s interfaces, add languages and do some further tweaking.
In terms of the propagation, the ransom trojan in question is email-borne. It contaminates Windows workstations via misleading debt notices attached to phishing emails. When opened, these files lead to an obfuscated JS artifact that stealthily downloads and runs the crapware on the computer. As soon as this happens, the Philadelphia ransomware starts cross-checking the victim’s files against a hard-coded list of targeted formats. It looks inside local drives, network directories, USB memory sticks and other types of removable drives. About 30 popular types of data are at risk, including Microsoft Office documents, various graphics formats, archives, audio and video files. While applying the above-mentioned Advanced Encryption Standard with 256-bit keys, the pest also replaces filenames with long lines of hexadecimal characters. Not only do these items become inaccessible, but it’s also impossible to work out what exactly has been encrypted. As the final stroke of the crooks’ brush to the nefarious masterpiece, the .locked extension gets concatenated to every entry.
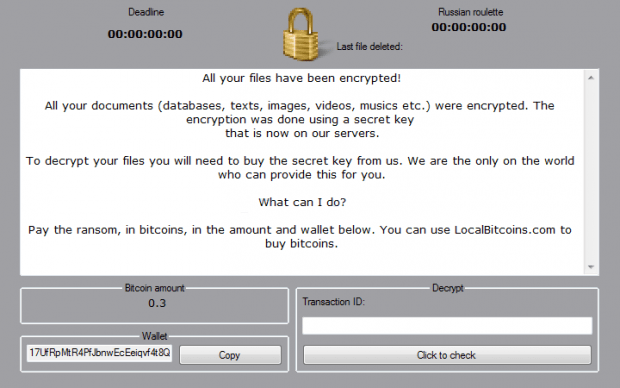
After the encryption and name skewing part of the compromise has been completed, the Philadelphia trojan displays a warning screen that also performs the function of a ransom note. Its default edition says, “All your documents (databases, texts, images, videos, musics, etc.) were encrypted. The encryption was done using a secret key that is now on our servers. To decrypt your files you will need to buy the secret key from us. We are the only on the world who can provide this for you.” In other words, the online predators want the victim to submit a ransom of 0.3 BTC to a Bitcoin wallet specified in the message. Otherwise, the so-called “Russian roulette” feature steps in. Its essence consists in the irreversible obliteration of a certain number of files after a specific amount of time expires. In addition to that, the ransomware provides a general deadline for coughing up the cryptocurrency. Note that the size of the ransom and all deadlines are set by every distributor individually via their personal Philadelphia Headquarter pane, so these values may vary.
Fortunately, there may be imperfections in the way the Philadelphia ransomware distributors configure and deploy their campaign. This may provide a loophole for successful data recovery through forensic and other methods described below. Meanwhile, users should bear in mind that prevention is the best cure. A bit of extra caution when handling spam emails can thwart the overwhelming majority of ransomware attacks.
Philadelphia ransomware automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Philadelphia ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by Philadelphia ransomware
Workaround 1: Use file recovery software
It’s important to know that the Philadelphia ransomware creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the ransomware under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether Philadelphia ransomware has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other ransomware, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this ransomware and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓