Remove Occamy.C virus (Trojan:Win32/Occamy.C)

Malicious code can be multipurpose and affect the host system in several ways rather stick with one vector of compromise. The Occamy.C virus is one of the culprits whose behavior cannot be unambiguously characterized impact-wise. However, its fundamental characteristic is all about the ability to communicate with a remote server. Here are the ins and outs of this tricky infection.
Table of Contents
What is the Occamy.C virus?
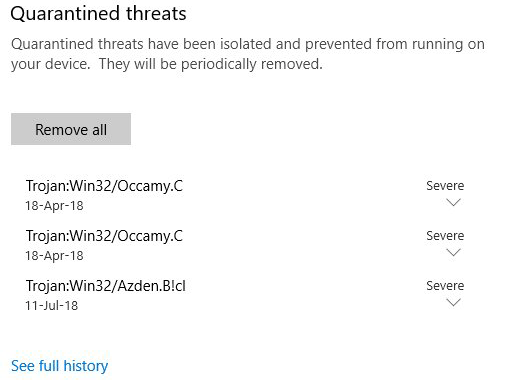
It’s difficult to find a one-stop security resource that gives you an idea of what the Occamy.C malware actually is. The only reason users provide feedback about it is because they are alerted by their antivirus suite, such as Windows Defender. Otherwise, they would probably not notice any signs of malicious activity on their computers. Also catalogued as Trojan:Win32/Occamy.C, this item can be reported off and on and automatically quarantined in compliance with predefined security rules and procedures of one’s AV tool. Its aliases in the definitions of other security solutions include Mal/Trickbt-A, Trojan.Win32.Generic.4!c, Trojan.IGENERIC, Artemis!EE40F798DB73, and Win32/GenBI.EE40F798!Olympus. By the way, the detection rate across the board is less than 10 percent, which means the infection is fairly stealthy by design.
The unsettling instances of Occamy.C detection typically commence after the user downloads some program over torrents hosted on dubious websites. Most of the time, the booby-trapped object is a computer game. For example, quite a few victims started experiencing the issues after downloading the Far Cry shooter game off of uncertified resources. The trojanized binary, when executed, spawns a number of processes reflected in Task Manager. These include nc.exe and dtdump.exe. If it weren’t for the AV service flagging the entity harmful, the entries in Task Manager would be the only signals of something potentially rogue running on the computer. So, the self-obfuscation hallmarks of the Occamy.C virus aren’t outstanding, to say the least. While hardly making itself felt on the outside, a quick peek into some elementary system maintenance stats will reveal the suspicious activity.
Why do security apps label this baddie severe then? There can be different speculations in this regard, but the most likely reason is the capability of Occamy.C to interact with a Command and Control server. It’s known for a fact that the Trojan exchanges traffic with its C2. It can also harvest system information, such as the OS version, IP address, geolocation, installed software and other details, along with the victim’s PID (personally identifiable data). If you put two and two together, you get a digital eavesdropper that collects sensitive information and sends it to its operators behind the user’s back. Furthermore, the Occamy.C virus can execute random commands given by the crooks in charge. It can thus download other malware components onto the host machine, such as a cryptojacker, adware or ransomware. Meanwhile, the perpetrating code continues to act as a backdoor, providing the malefactors with options for adverse maneuver in the future. To wrap up, Occamy.C doesn’t belong inside a PC and hence should be eliminated immediately.
Remove Occamy.C trojan using Control Panel
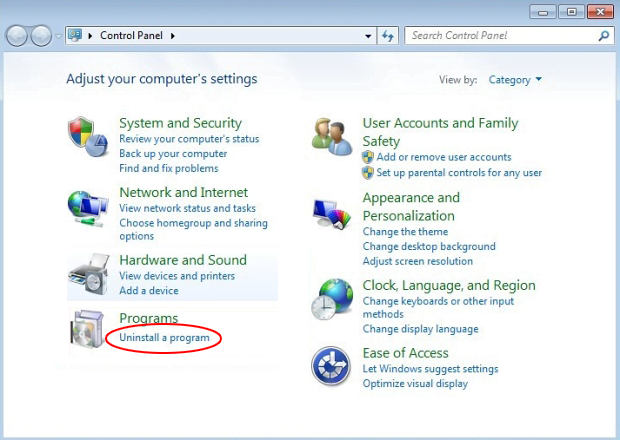
- Open Control Panel. On Windows XP / Windows 8, go to Add or Remove Programs. If your OS is Windows Vista / Windows 7 / Windows 10, choose Uninstall a program

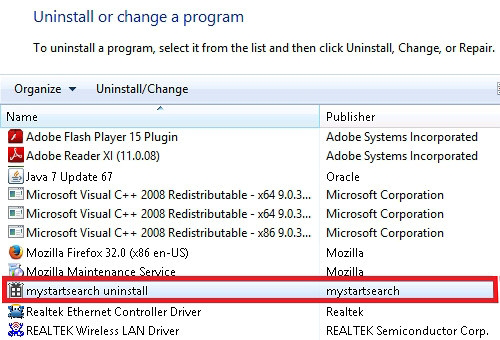
- Look down the list and locate an app that appears fishy. Click the Uninstall/Change (Change/Remove) option to get the intruder removed if spotted

Occamy.C trojan automatic removal
The extermination of Occamy.C trojan can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped out from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
2. The scan will come up with a list of detected items. Click Fix Threats to get the trojan removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the infection. However, it might be a good idea to consider ascertaining the trojan is gone for good.
Posted in: KnowledgeBase
Leave a Comment (0) ↓