Remove nsmaking.com virus from Android, Chrome, Firefox, IE
Online criminals continue to look for tricky ways of disseminating their malicious code. Users have become wary of obvious malware distribution tactics, such as spam attachments and fishy ads on the Internet, so the new methods mostly work out as long as they are outside that prosaic paradigm. The nsmaking.com browser virus represents a different form of malvertising that engages one infection to distribute another.
Table of Contents
What is the nsmaking.com virus?
Nsmaking.com isn’t a run-of-the-mill website that users can visit to obtain some sort of information. Contrary to that, it was set up by unscrupulous netizens who seek to implement a large-scale malware distribution hoax. In fact, said web page is an element of a bigger ruse aimed at installing a dangerous piece of software onto visitors’ computers. The e-malefactors behind it employ a two-layered approach to deposit their bad code. The nsmaking.com component is the starting point. People don’t go to that site because they want to – instead, they visit it because of a redirect occurring in their preferred web browser. The hijacker, which is the conventional labeling for these infections, takes over Google Chrome, Mozilla Firefox, or MS Internet Explorer and forces hits to the rogue domain name without the user’s approval.
For the rerouting activity to take effect, a prior initial compromise needs to have taken place. It is usually a matter of bundling, where users unknowingly install the potentially unwanted application when getting what they think is a nifty free media downloader, software crack tool, Flash Player, or something similarly catchy. The whole gist of this shady mechanism is that you cannot see what you are actually installing unless you peek beyond the default (recommended) setup option. It’s only the custom mode that may disclose the bundled items and allow for unchecking the redundant ones. Anyway, lots of users get on this hook and discover the strange browser malfunctions shortly afterwards. No wonder – the nsmaking.com virus turns the victim’s browsing routine upside down. It installs a new add-on that forcibly replaces the original Internet settings to make sure the malicious page pops up instead of the homepage, default search engine, and new tab page.
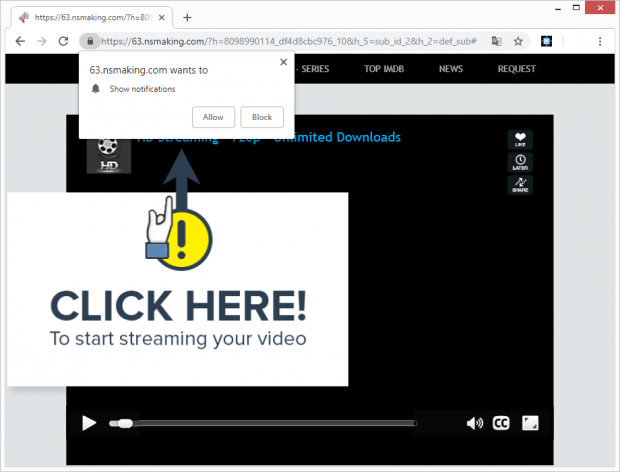
The brainwashing essence of nsmaking.com comes down to some kind of a streaming video session that won’t begin due to an allegedly missing plugin or other browser helper object. The URL of the intrusive page is going to start with a number that may swap from redirect to redirect, something like 16.nsmaking.com. Meanwhile, the domain name is appended with a long, gibberish-looking campaign identifier string. The page is inundated with pop-ups that instruct the victim to click on the “Allow” button at the top in order to watch or download the video. This button is on a browser dialog where nsmaking.com asks for permission to show notifications. The catch is that in case the victim gives that privilege, the number of annoying pop-ups will increase exponentially and they will be presented on random pages, not just nsmaking.com.
The worst trait of this activity, though, is that the unwelcome site will trigger a download in the background, and the resulting payload is most likely to be something much more harmful than the browser hijacker proper. The possible follow-up intruder can be ransomware, stealthy crypto miner, or banking Trojan. Given the overall severity of this compromise, it’s wise to remove nsmaking.com virus before it builds a whole chain of deleterious code plaguing the target computer.
Nsmaking.com redirect automatic removal
The extermination of Nsmaking.com redirect can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped out from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
2. The scan will come up with a list of detected items. Click Fix Threats to get the redirect removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the infection. However, it might be a good idea to consider ascertaining the redirect is gone for good.
Remove Nsmaking.com redirect using Control Panel
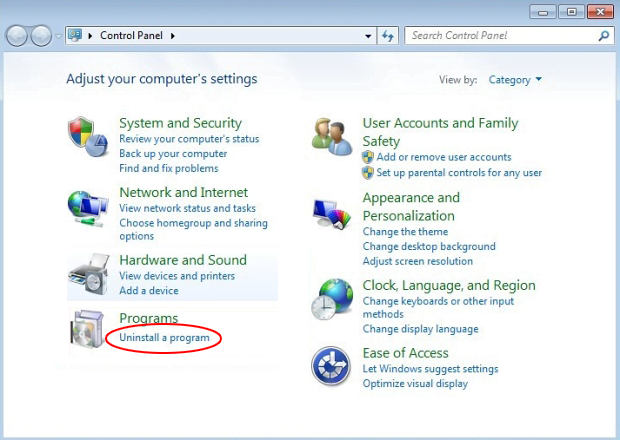
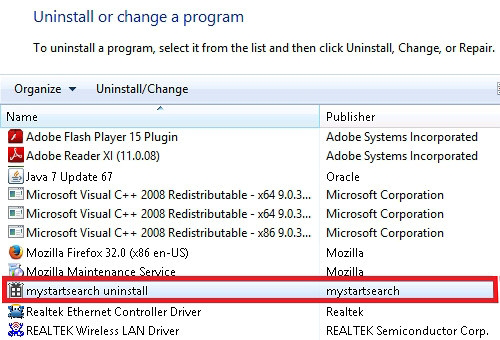
- Open Control Panel. On Windows XP / Windows 8, go to Add or Remove Programs. If your OS is Windows Vista / Windows 7 / Windows 10, choose Uninstall a program

- Look down the list and locate an app that appears fishy. Click the Uninstall/Change (Change/Remove) option to get the intruder removed if spotted

Nsmaking.com redirect removal by resetting the affected browser
Please take into consideration that as effective as it is, the procedure of restoring browser defaults will lead to the loss of personalized settings such as saved passwords, bookmarks, browsing history, cookies, etc. In case you are not certain this outcome is suitable despite its obvious efficiency, it’s advised to follow the automatic removal method described in one of the previous sections of this tutorial.
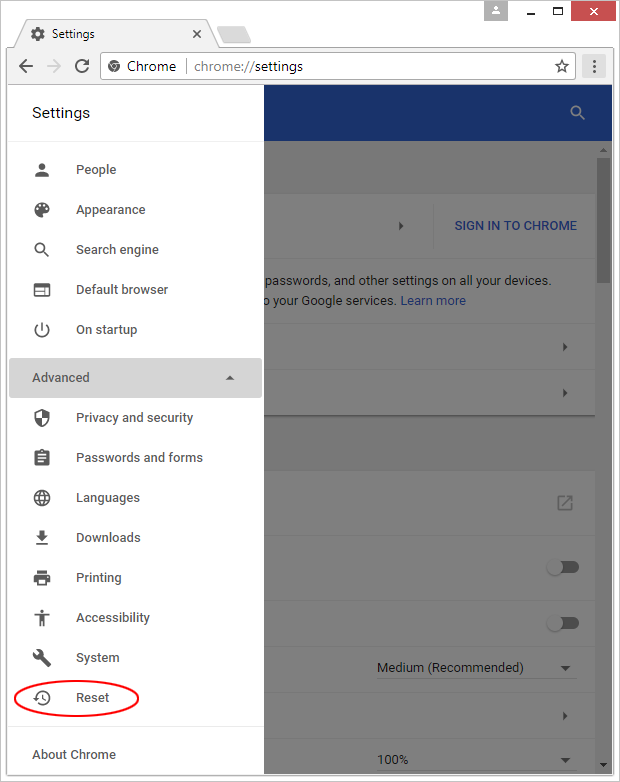
Reset Google Chrome
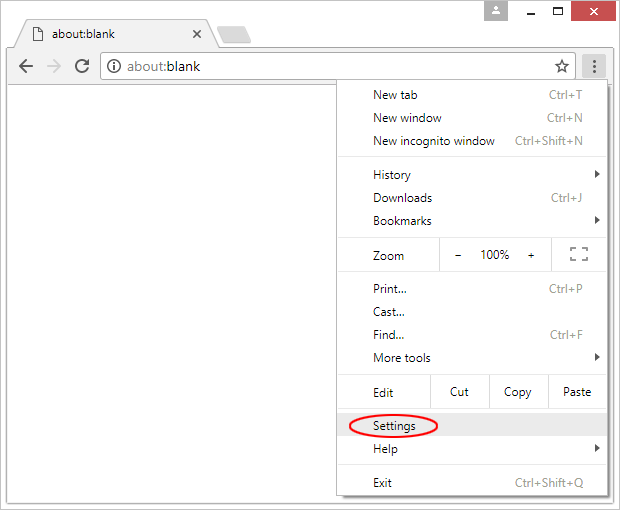
- Click on the Chrome menu icon and select Settings

- Locate the Advanced option under Settings and click on it to expand the menu. Then, pick the Reset button at the bottom

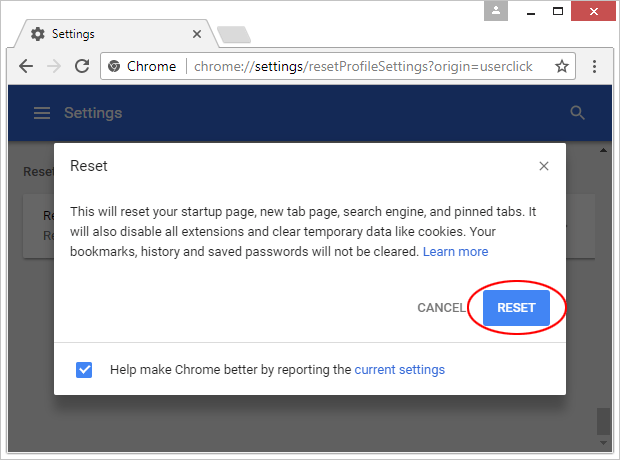
- When a new screen appears, hit Reset once again

- Chrome will now display a confirmation dialog box listing the types of data that will be lost if you proceed. Read the message carefully and, if you’re sure, click Reset

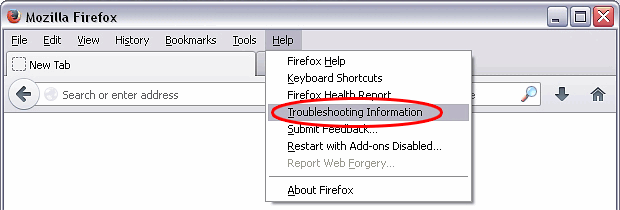
Reset Mozilla Firefox
- Click on Help menu and select Troubleshooting Information from the drop-down list, or type about:support in the URL field

- On the Troubleshooting Information screen, click Refresh Firefox option and confirm the procedure on another dialog

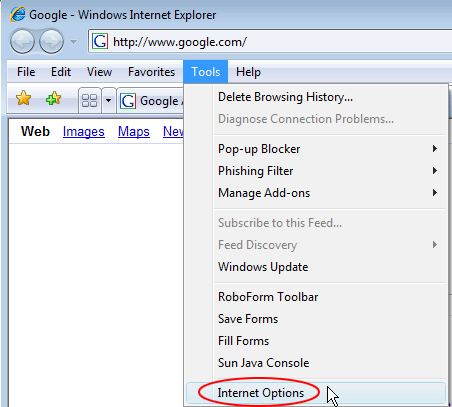
Reset Internet Explorer
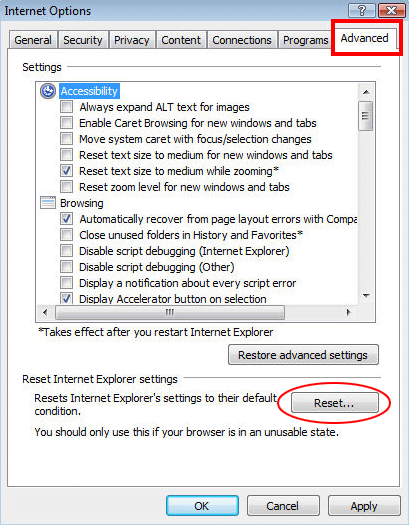
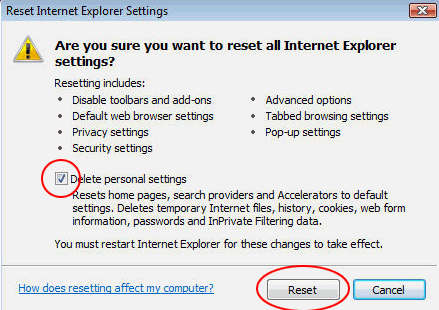
- In IE, go to Tools and select Internet Options from the list

- Hit the Advanced tab and click on the Reset option

- IE will now display Reset Internet Explorer Settings box, where you should put a checkmark next to Delete personal settings option and click Reset at the bottom

Verify whether Nsmaking.com redirect has been completely removed
For certainty’s sake, it’s advised to repeatedly run a scan with the automatic security software in order to make sure no harmful remnants of this redirect are left inside Windows Registry and other operating system locations.
Nsmaking.com redirect removal
What you need to do is uninstall the application that’s causing trouble. As it has been mentioned, however, disabling and removing the virus in regular mode is to no avail, so the steps below are must-follow.
1. Boot the device into safe mode
– Press and hold the Power button until the respective screen pops up
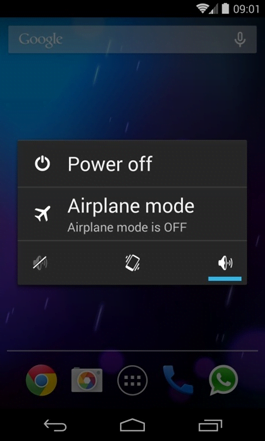
2. Now tap and hold the option that says Power off. Depending on the vendor and the phone model, the methods can vary. If nothing happens as a result of the above manipulations, power down the device, then press and hold the Volume Down and Volume Up buttons simultaneously while it’s starting back up.
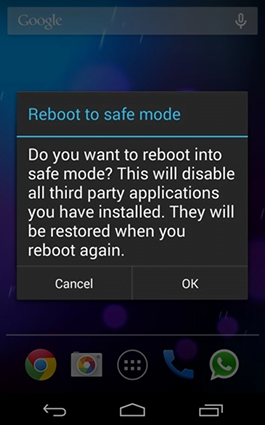
3. Confirm rebooting into safe mode by tapping OK
4. When in safe mode, go to Settings and select Apps
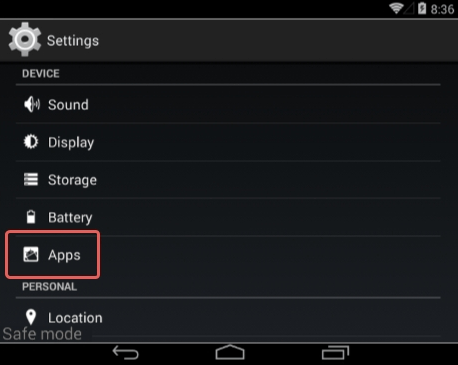
5. Look down the list of programs and locate a suspicious app or apps that were recently installed
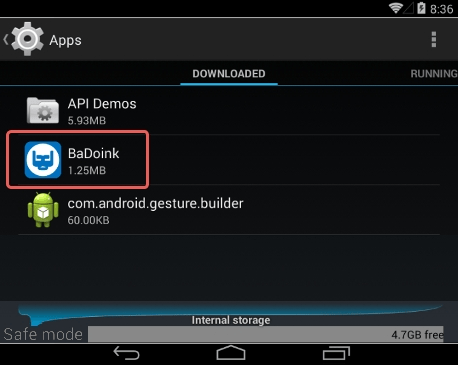
6. Tap each potentially unwanted app in turn and select the Uninstall option. If this button is not active, try Force stop first
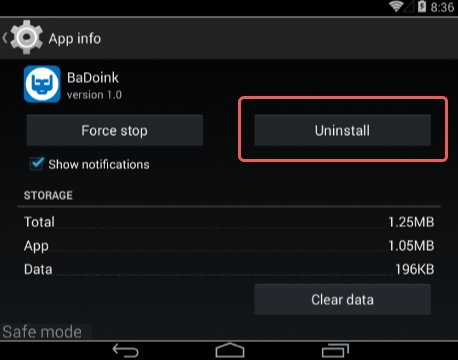
7. Tap OK on the confirmation dialog to uninstall the potentially unwanted app
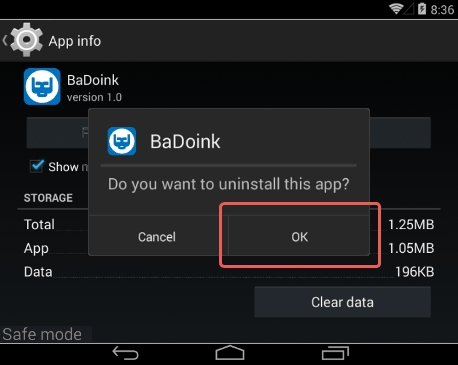
8. Restart into standard mode. The Nsmaking.com redirect should have now vanished from your Android device. You might also want to consider installing a mobile security solution to prevent attacks of this sort further on.
Highly recommended: scan your Android device for issues
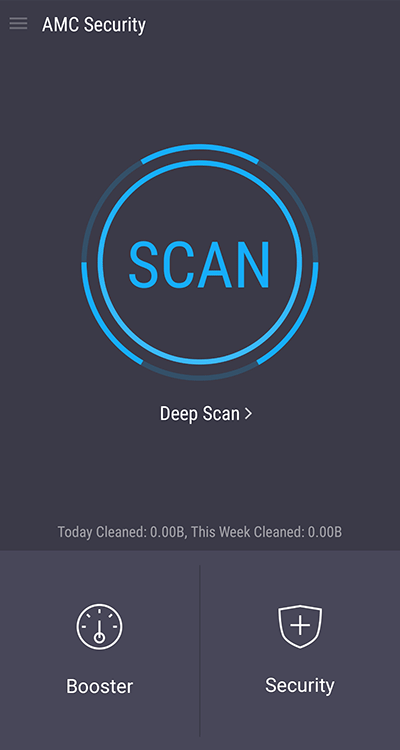
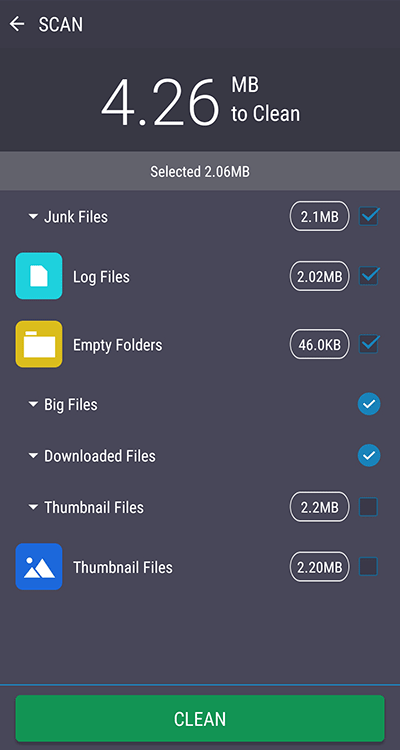
1. Download and install AMC Security Pro app onto your device. This is a one-stop solution to keep your Android gadget’s performance at its peak and ensure effective protection against known and zero-day mobile threats. Once the tool is up and running, go ahead and tap the SCAN button.
2. The scan report will list the detected issues, including PUAs (potentially unwanted applications), malware, and memory hogs such as junk and big files that might not belong on your device. Tap the CLEAN button at the bottom to complete the removal.
Now that the cleanup is done, check your smart device for malicious activity that brought you to this guide in the first place. Also, consider keeping this cleanup and maintenance tool on board as it’s equipped with additional useful features, such as real-time web security, privacy advisor, anti-phishing, payment security, battery saver, and more.
Posted in: KnowledgeBase
Leave a Comment (0) ↓