Nozelesn ransomware removal and decryptor
As weak as it is, the ransomware economy appears to be slowly regaining momentum. At least, that’s how things look on the arena of targeted attacks, where the preys are either specific organizations or countries. The Nozelesn ransomware campaign, which broke out recently, exemplifies this tendency as it mainly focuses on infecting users in Poland.
Table of Contents
What is the Nozelesn ransomware?
Whatever the name could mean, Nozelesn is a competently coded sample of blackmail malware used primarily in targeted attacks. It was first reported in early July 2018 and has since infected numerous home users and organizations in Poland, demonstrating its targeted essence. For the record, though, some users have been hit outside the country, which is a predictable collateral damage in these waves. Perhaps the accidental victims share some files with the intended ones in the cloud. Anyway, the original run of the attacks was mostly deployed using spam. The crooks sent out a bevy of spoof emails camouflaged as DHL invoices, where the attached file triggered the infestation chain on recipients’ machines.
In case this social engineering trick works out and the user gullibly opens the embedded fake invoice, the Nozelesn ransomware payload will be executed in a surreptitious way, with hardly any chance of detection. Then, the offending code will initiate a major scan for data on the host as well as external drives and network shares, both mapped and unmapped. Every object found during this scan will become encrypted. There are scarce details at this point about the exact encryption algorithm being applied, but it’s most likely a fusion of symmetric AES (Advanced Encryption Standard) and asymmetric RSA cipher. The crypto implementation appears to be done right, so there is currently no free fix for this predicament.
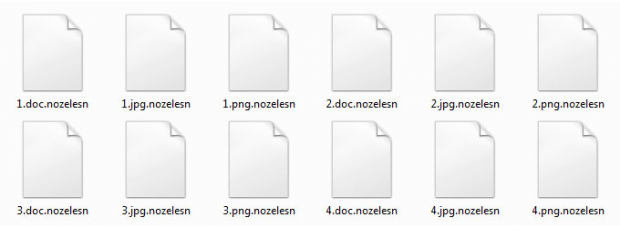
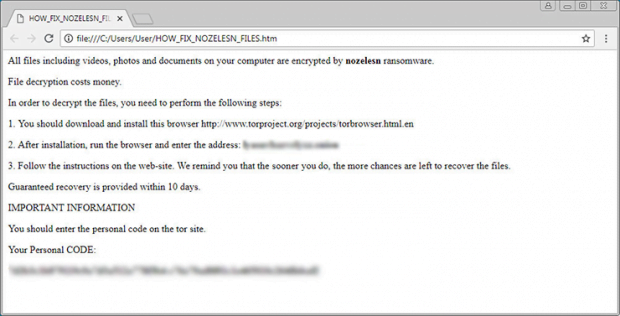
Not only do the encrypted files change on the inside, but their external manifestation undergoes a modification, too. The filenames get the .nozelesn string concatenated to them, so a sample one named Report.pdf will morph into Report.pdf.nozelesn. In order to give the victim some clues on what to do with the numerous weird objects that suddenly replaced their personal files, the virus adds a ransom note named HOW_FIX_NOZELESN_FILES.htm to the desktop. Just like the average how-to in crypto extortion scenarios, this one starts with a warning phrase, namely, “All files including videos, photos and documents on your computer are encrypted by nozelesn ransomware.” It also provides three steps to decrypt files, emphasizing that it will cost money.
Ultimately, the victim is forwarded to a Tor page called “Nozelesn decryption cabinet”. It demands 0.1 BTC, worth about 650 USD, for the secret key that will supposedly help decrypt files. Moving on with the payment is a terribly cold comfort, though, even if the criminals’ decryption routine works. The most important thing recommended in the Nozelesn ransomware raid scenario is to first try all the options that don’t involve interacting with the attackers. The part below will shed light on those methods.
Nozelesn extension automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Nozelesn ransomware remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the extension and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by Nozelesn extension
Workaround 1: Use file recovery software
It’s important to know that the Nozelesn extension creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the extension under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether Nozelesn extension has been completely removed
Again, ransomware removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the extension itself does not belong inside your computer. Incidentally, it often comes with other extension, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this extension and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓