Netalpha virus removal from Android

The crapware called Netalpha poses a serious security and stability issue for Android devices. It isn’t new, having originally surfaced around April 2016. The spike in the propagation of this mobile Trojan as of December, though, makes it one of the top infections in the current Android threat landscape. Users hit by this pest keep getting “Unfortunately, Netalpha has stopped” alerts and experience random bloatware being installed without permission.
Table of Contents
What is Netalpha virus?
The number of Android users contaminated with the Netalpha Trojan is skyrocketing. This app is harmful for a bunch of reasons. One of the biggest adverse effects is that it prevents the operating system and arbitrary applications from running in normal mode. It becomes problematic to launch Google Play and multiple legit programs, which recurrently get closed for no apparent reason. This activity is accompanied by annoying popup alerts appearing off and on, such as messages that say,
“Unfortunately, Netalpha has stopped”.
To top it all off, the infection promotes other potentially unwanted software without getting appropriate authorization from the user. The opportunistic malware may include perpetrating entities like Android.Xiny.19.origin, Key Chain, MonkeyTest, Quick Swipe, Measure, Engriks, Time Service, BaDoink, and Fast Search.
Sensitive data theft is a concomitant concern going alongside the rise of the Netalpha plague. Not only do the operators of this malware use it to push numerous malicious apps and cause performance issues, but they also attempt to pilfer personally identifiable information (PII). To this end, the offending code gets high-level privileges on an infected Android device. Doing so may grant it access to a victim’s mobile banking system and other online accounts. However, this effect is invisible to the naked eye, so the bug may sit inside a gadget and harvest confidential data on it for a long time without being detected. In light of this property of the Netalpha virus, the conspicuous side effects are probably on the plus side of the matter, because they are a hard-to-miss giveaway. These are obnoxious ads, warning messages, browser redirects, and new applications starting to show up on the device. Although this activity is a drag, it raises some red flags at the early phase of the attack and enables users to take measures before their identity is stolen.
Netalpha propagates mostly through bundling with other applications. Such a scheme is cybercriminals’ favorite, because people tend to accept a setup’s terms of service without really delving deeper than the default installation mode. Meanwhile, unwanted items may lay under the hood of such a preset. The only way to opt out of it is to select the Custom install option and untick everything redundant. Having crept inside this way, the Netalpha virus may attempt to root the device so that it runs with elevated permissions and cannot be uninstalled in the regular fashion. Luckily, there is a workaround that beats this Trojan’s persistence and allows people to get rid of it.
Netalpha undefined removal
What you need to do is uninstall the application that’s causing trouble. As it has been mentioned, however, disabling and removing the virus in regular mode is to no avail, so the steps below are must-follow.
1. Boot the device into safe mode
– Press and hold the Power button until the respective screen pops up
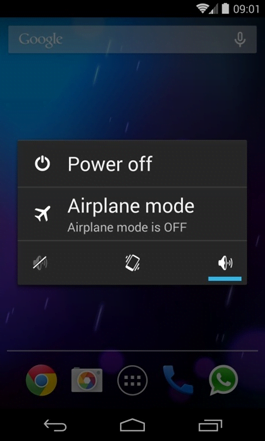
2. Now tap and hold the option that says Power off. Depending on the vendor and the phone model, the methods can vary. If nothing happens as a result of the above manipulations, power down the device, then press and hold the Volume Down and Volume Up buttons simultaneously while it’s starting back up.
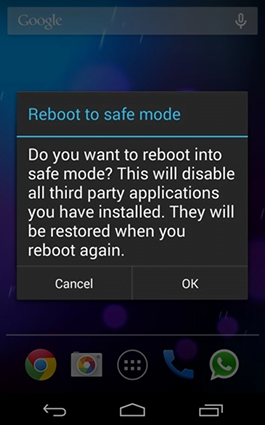
3. Confirm rebooting into safe mode by tapping OK
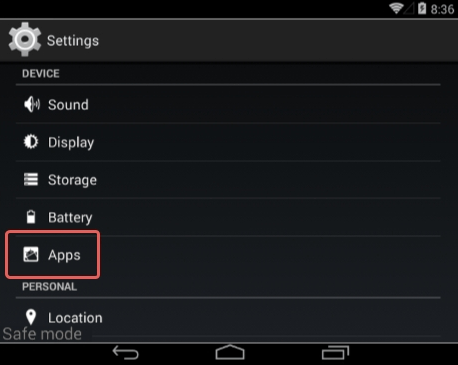
4. When in safe mode, go to Settings and select Apps
5. Look down the list of programs and locate a suspicious app or apps that were recently installed
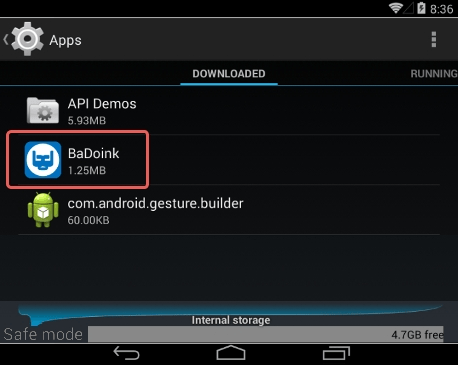
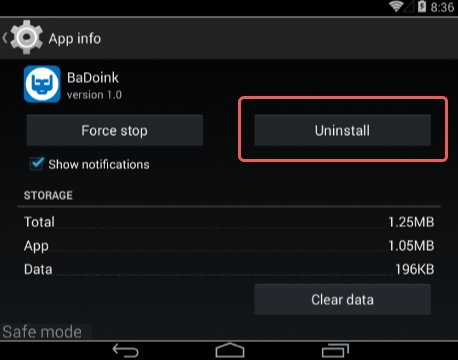
6. Tap each potentially unwanted app in turn and select the Uninstall option. If this button is not active, try Force stop first
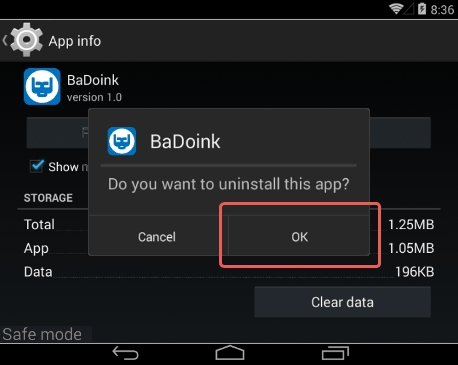
7. Tap OK on the confirmation dialog to uninstall the potentially unwanted app
8. Restart into standard mode. The Netalpha undefined should have now vanished from your Android device. You might also want to consider installing a mobile security solution to prevent attacks of this sort further on.
Posted in: KnowledgeBase
Leave a Comment (0) ↓
