My Best Store Inc. fake emails: ups@mybestore.com scam details
Malspam is, by far, the main vector of malware distribution nowadays. It has become cybercrooks’ favorite due to its universality – it allows them to spread virtually any malicious program by simply attaching booby-trapped files to such emails. Sometimes these campaigns harness well-known brand names or services to appear more persuasive, as is the case with the Mybestore.com email scam.
Table of Contents
What is Mybestore.com email scam?
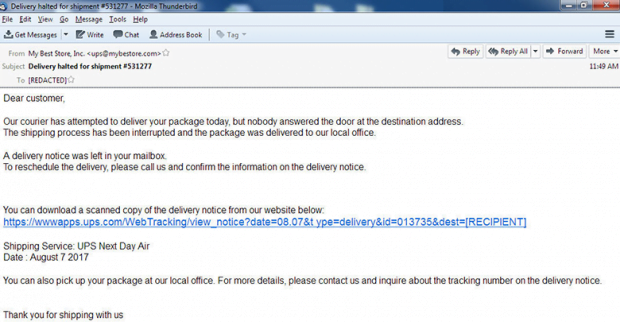
Mybestore.com, or My Best Store, is a popular ecommerce hub for a variety of goods, including health products, clothing, consumer electronics, travel and sports gear. It boasts wholesale prices and fast delivery. While being a godsend to customers, these types of online resources are traditionally a lure for scammers as well. In an ongoing fraudulent spam wave, an unidentified group of ne’er-do-wells have been camouflaging virus propagation activity as genuine notifications from Mybestore.com. The rogue messages pretend to come from ups@mybestore.com, the shipping service being “UPS Next Day Air”. Their subject is “Delivery halted for shipment #531277”, where the shipment number may vary.
The body of the phony message is as follows,
Dear customer, our courier has attempted to deliver your package today, but nobody answered the door at the destination address. The shipping process has been interrupted and the package was delivered to our local office. A delivery notice was left in your mailbox. To reschedule the delivery, please call us and confirm the information on the delivery notice. You can download a scanned copy of the delivery notice from our website below.
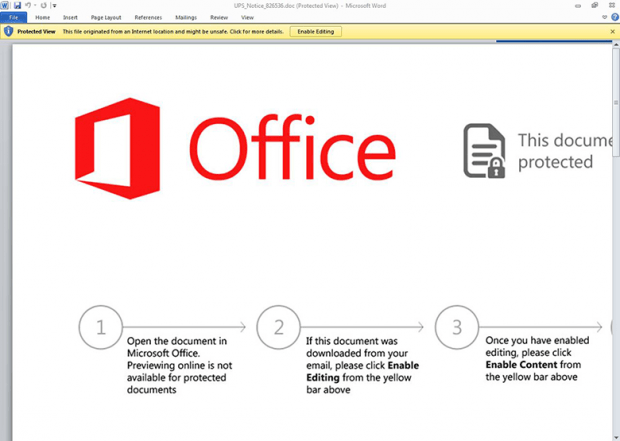
This part is followed by a rogue link, most likely starting with wwwapps.ups.com/WebTracking, that the recipient is instructed to click for further details of the purported delivery. This URL is the main catch in the whole scheme as it leads to a fraudulent download. The linked-to file is a malware-tainted Microsoft Office document named “UPS_Notice_[random digits].doc. Once opened, it says, “This document is protected.” To be able to view the contents, the victim is urged to click the “Enable Editing” button in a notification at the top. By doing so, the unsuspecting user enables macros, which in turn results in downloading malicious code behind the scenes.
Ultimately, Mybestore.com email scam initiates an infection chain engaging a notorious malware downloader called Hancitor or Pony. This peddling process takes place behind the user’s back and leads to promotion of follow-up malware. The infection being pushed this way may be anything from spyware to ransomware that will encrypt all personal data on HDD partitions and network drives and demand a ransom for decryption. The tandem of realistic-looking Mybestore.com email scam and Hancitor/Pony malware downloader is quite an effective way to deploy arbitrary harmful software on recipients’ computers. Since there is no file attached to these rogue notifications, most security suites won’t raise any red flags on them.
When dealing with suspicious emails like this, users should always look for clues that may indicate fraudulent activity. First of all, ask yourself whether you are expecting any shipment from My Best Store. If you aren’t, refrain from following any embedded links as they may get you infected. Office documents that ask you to turn on macros are a giveaway, too.
Mybestore.com email automatic removal
The extermination of Mybestore.com fake can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped out from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
Download Mybestore.com remover
2. The scan will come up with a list of detected items. Click Fix Threats to get the scam removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the infection. However, it might be a good idea to consider ascertaining the email is gone for good.
Posted in: KnowledgeBase
Leave a Comment (0) ↓