MOLE02 virus ransomware: how to decrypt .mole02 extension files
It’s not only legit software that’s subject to regular updates – malicious code like ransomware is far from being a stationary target, so it tends to undergo tweaks once in a while too. The extortion-oriented strain known as CryptoMix has recently given rise to a new variant that appends the .MOLE02 extension to enciphered files. Learn what other changes are under the newcomer’s hood.
Table of Contents
What is the MOLE02 ransomware?
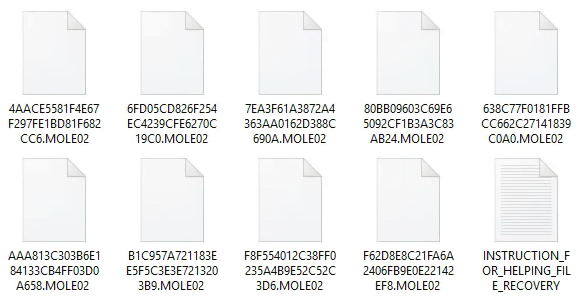
Almost like a person’s iris or fingerprints, a file extension can be a unique hallmark sign of a specific ransomware sample. Perhaps online extortionists hate to resemble each other and prefer showing off, so each campaign is typically associated with certain indicators that cannot be encountered elsewhere. In the case of a new derivative of the prolific CryptoMix ransomware lineage, such a characteristic is the .MOLE02 string that’s concatenated to every file encrypted in the course of the attack. Just like a few previous CryptoMix spinoffs called Revenge and CryptoShield, the one under scrutiny also makes it impossible to work out which encoded entry matches a specific personal file. It scrambles filenames as well, turning them into random sequences of 32 hexadecimal characters.
The MOLE02 virus drops ransom notes named _HELP_INSTRUCTION.txt or INSTRUCTION_FOR_HELPING_FILE_RECOVERY.txt. The wording of this how-to document has been slightly modified compared to previous iterations. The alert part of it now goes, “All of your files are encrypted with RSA 2048 and AES-128 ciphers.” This message, unfortunately, holds true for every attack incident. The cryptographic facet of this ransomware is quite robust due to its compound gist, which tangles decryption significantly. The rest of the ransom note’s text is rather classic for a file-encrypting infection, instructing the victim to install Tor Browser, type a specific URL in the address bar, and follow directions on the payment page using personal Decrypt-ID to proceed.
Aside from the format of file jumbling, all versions of this ransomware family share some other common ground. They are email-borne, whereas the subsequent infection chain may vary. Malicious spam with MOLE02 payload on board will usually contain a redirect URL leading to a rogue Word online website that states a plugin needs to be updated. Then, a victim will be prompted to open a ZIP archive containing extracted JavaScript (.js) file. This file, in its turn, downloads the ransomware and possibly drive-by threats like the Kovter click-fraud malware. When inside, the ransom Trojan scans local and shared drives for potentially valuable data and applies the above-mentioned ciphers to lock it all down. When infected with the .MOLE02 file extension virus, users should start the fix with eradicating the ransomware proper and possible accompanying cyber-pests. Then, it’s worthwhile to try best-practice data recovery methods, keeping in mind that coughing up the ransom is the last resort rather than an inescapable option.
MOLE02 extension automatic removal
Extermination of this ransomware can be efficiently accomplished with reliable security software. Sticking to the automatic cleanup technique ensures that all components of the infection get thoroughly wiped from your system.
1. Download recommended security utility and get your PC checked for malicious objects by selecting the Start Computer Scan option
2. The scan will come up with a list of detected items. Click Fix Threats to get the ransomware and related infections removed from your system. Completing this phase of the cleanup process is most likely to lead to complete eradication of the plague proper. Now you are facing a bigger challenge – try and get your data back.
Methods to restore files encrypted by MOLE02 extension
Workaround 1: Use file recovery software
It’s important to know that the MOLE02 extension creates copies of your files and encrypts them. In the meanwhile, the original files get deleted. There are applications out there that can restore the removed data. You can utilize tools like Stellar Data Recovery for this purpose. The newest version of the extension under consideration tends to apply secure deletion with several overwrites, but in any case this method is worth a try.
Download Stellar Data Recovery Professional
Workaround 2: Make use of backups
First and foremost, this is a great way of recovering your files. It’s only applicable, though, if you have been backing up the information stored on your machine. If so, do not fail to benefit from your forethought.
Workaround 3: Use Shadow Volume Copies
In case you didn’t know, the operating system creates so-called Shadow Volume Copies of every file as long as System Restore is activated on the computer. As restore points are created at specified intervals, snapshots of files as they appear at that moment are generated as well. Be advised this method does not ensure the recovery of the latest versions of your files. It’s certainly worth a shot though. This workflow is doable in two ways: manually and through the use of an automatic solution. Let’s first take a look at the manual process.
-
Use the Previous Versions feature
The Windows OS provides a built-in option of recovering previous versions of files. It can also be applied to folders. Just right-click on a file or folder, select Properties and hit the tab named Previous Versions. Within the versions area, you will see the list of backed up copies of the file / folder, with the respective time and date indication. Select the latest entry and click Copy if you wish to restore the object to a new location that you can specify. If you click the Restore button, the item will be restored to its original location.

-
Apply Shadow Explorer tool
This workflow allows restoring previous versions of files and folders in an automatic mode rather than by hand. To do this, download and install the Shadow Explorer application. After you run it, select the drive name and the date that the file versions were created. Right-click on the folder or file of interest and select the Export option. Then simply specify the location to which the data should be restored.

Verify whether MOLE02 extension has been completely removed
Again, file removal alone does not lead to the decryption of your personal files. The data restore methods highlighted above may or may not do the trick, but the ransomware itself does not belong inside your computer. Incidentally, it often comes with other extension, which is why it definitely makes sense to repeatedly scan the system with automatic security software in order to make sure no harmful remnants of this extension and associated threats are left inside Windows Registry and other locations.
Posted in: KnowledgeBase
Leave a Comment (0) ↓